Beyond the Firewall: Smart Cyber Solutions for Modern Businesses

Why Cyber Security Solutions for Business Are More Critical Than Ever
Cyber security solutions for business are no longer optional—they’re essential. Businesses face daily threats that can shut down operations, steal sensitive data, and destroy customer trust.
Quick Answer: Essential Cyber Security Solutions Every Business Needs:
- Multi-Factor Authentication (MFA) – Blocks 99% of automated attacks on accounts
- Endpoint Detection and Response (EDR) – Protects devices and detects threats in real-time
- Next-Generation Firewalls – Stops threats before they enter your network
- Security Awareness Training – Turns employees into your first line of defense
- Managed Security Services – Provides 24/7 monitoring and expert response
- Cloud Security – Protects data in hybrid and multi-cloud environments
- Data Backup and Recovery – Ensures business continuity after incidents
The numbers are sobering: the average data breach now costs $4.88 million, a 10% increase in just one year. For small and medium businesses, a single incident can be catastrophic.
Effective cybersecurity isn’t about expensive tools, but the right approach for your business’s unique risks and resources.
Traditional security—relying on antivirus and basic firewalls—no longer cuts it. Modern threats like ransomware, phishing, and insider threats move too fast. Ransomware can encrypt a business in under 17 hours, phishing causes 31% of incidents, and insider threats account for over 43% of data breaches.
This guide breaks down what works, which solutions matter most, and how to choose them without breaking your budget. We’ll also cover why the human element is as important as technology.
I’m Reade Taylor, founder of Cyber Command. With over a decade of experience, including as an engineer at IBM Internet Security Systems, I built Cyber Command to make cyber security solutions for business accessible, understandable, and effective for all organizations.
Key terms for cyber security solutions for business:
The Evolving Threat Landscape: Why Traditional Security Fails

The digital world presents incredible opportunities but also evolving threats. Yesterday’s security may not work today. The increasing complexity and frequency of cyberattacks make robust cyber security solutions for business essential. A single breach can cause significant financial, reputational, and legal damage.
Primary Cybersecurity Threats Facing Businesses
Let’s break down the most common threats businesses face:
- Ransomware: This malware encrypts your data, holding it hostage until a ransom is paid. With an average time to ransom of just 17 hours, it can bring operations to a grinding halt. It’s a complex threat often involving multiple attack vectors. Learn more in our guide on A deeper look at Ransomware Attacks.
- Phishing Attacks: These deceptive emails or messages trick people into revealing sensitive information like passwords. Phishing is responsible for 31% of all security incidents and is becoming more sophisticated, sometimes using AI to craft convincing lures.
- Insider Threats: Risks can come from within, when a current or former employee, contractor, or associate gains unauthorized access. These threats, which can be malicious or accidental, account for over 43% of data breaches. Learn how to mitigate them in Understanding Proactive Insider Threat Detection.
- Supply Chain Attacks: Attackers target SMBs as an entry point to larger organizations. By compromising a vendor, they can access multiple downstream targets, making every link in your supply chain a potential vulnerability.
- AI-Driven Attacks: Cybercriminals now use AI to make their attacks faster and more targeted. This includes AI-generated phishing emails and malware that can adapt to defenses.
- Malware: A broad term for malicious software like viruses, worms, and spyware. It aims to damage, disrupt, or gain unauthorized access to systems. Understanding How Malicious Code Can Cause Damage is fundamental.
- Social Engineering: This tactic exploits human psychology to manipulate people into divulging confidential information. Phishing is one form, but it also includes pretexting and baiting.
- Zero-day Exploits: These attacks exploit a software vulnerability unknown to the vendor, for which no patch is available. They are dangerous because there’s no immediate defense.
- Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks: These attacks overwhelm a system, server, or network resource with traffic, making it unavailable to legitimate users.
The Rise of Sophisticated Attacks
The landscape isn’t just about more threats; it’s about smarter threats. Cybercriminals are using increasingly sophisticated methods:
- Automated Attacks: Bots and scripts scan for vulnerabilities and launch attacks at scale, making manual defenses quickly obsolete.
- Nation-State Actors: State-sponsored groups engage in cyber espionage and intellectual property theft, using vast resources and advanced techniques.
- Cybercrime-as-a-Service: The dark web offers a marketplace for cybercrime tools and services, lowering the barrier to entry for complex attacks.
These evolving tactics necessitate a shift from reactive defense to proactive, multi-layered cyber security solutions for business. For a broader perspective on the changing nature of threats, explore More on modern Cyber Attacks.
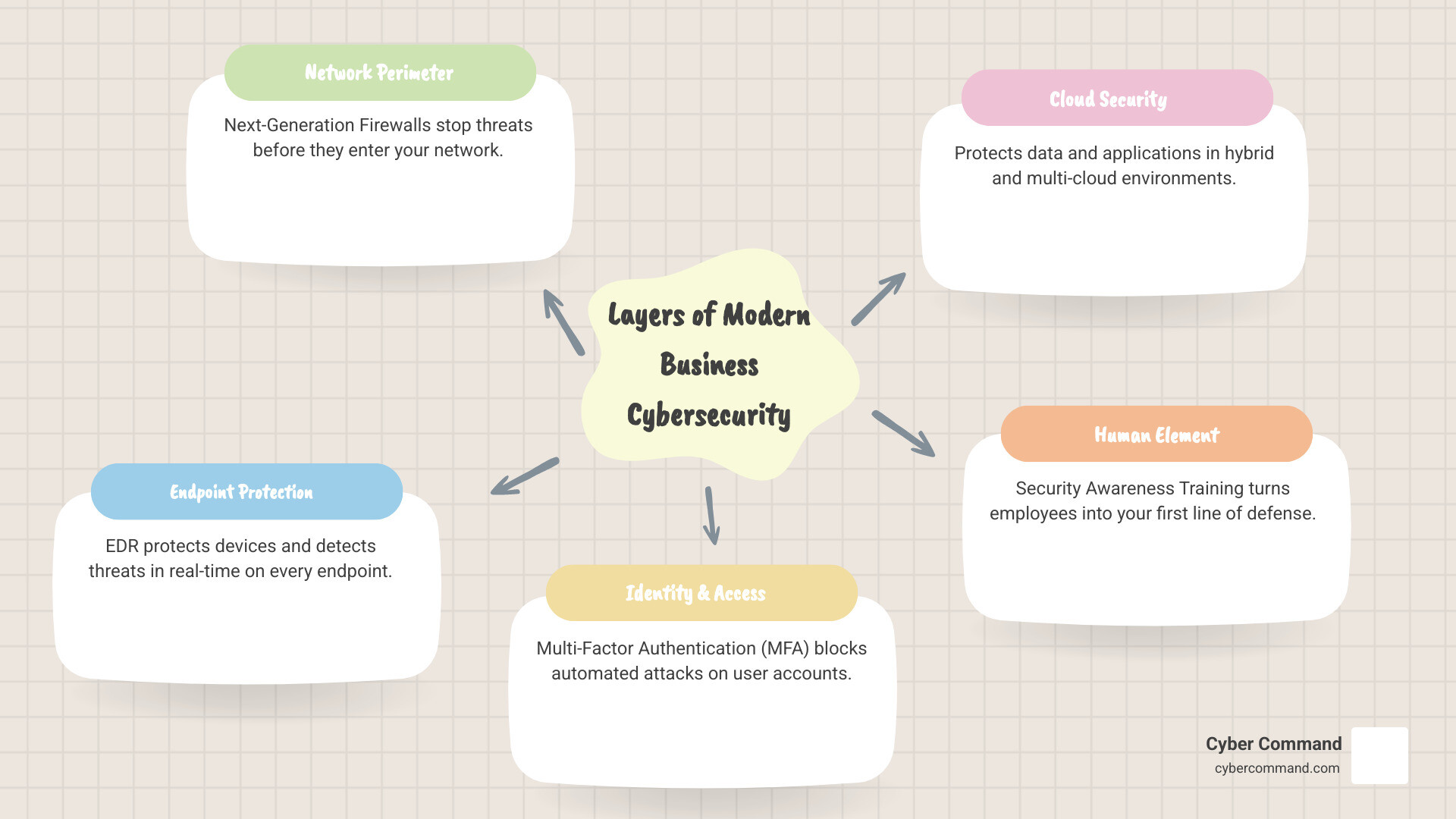
Core Components of a Modern Cybersecurity Defense

Today’s complex threats require more than a single tool. Modern cybersecurity uses a layered, “defense-in-depth” strategy with multiple controls across your IT environment. This proactive approach stops threats at entry points and detects what gets through.
To secure your business, you need to understand What are the Five Types of Cybersecurity, which cover network, application, cloud, critical infrastructure, and IoT security. Here’s a list of essential security tools for SMBs:
- Multi-Factor Authentication (MFA)
- Endpoint Detection and Response (EDR)
- Next-Generation Firewalls (NGFW)
- DNS Protection
- Email Gateway Security
- Intrusion Detection and Prevention Systems (IDS/IPS)
- Logging and Log Monitoring
- Authentication Services/VPN
- Cloud-based Security
- Web Application Firewalls (WAF)
- Enterprise Password Management/Privileged Access Management (PAM)
- Vulnerability and Threat Management
Foundational Network and System Security
Your network perimeter is your first line of defense. Strong foundational security makes it difficult for threats to get in.
- Next-Generation Firewalls (NGFW): Going beyond traditional firewalls, NGFWs inspect data packet content. They provide broad threat protection, secure external connections, and use machine learning to block unknown threats like zero-day attacks. Learn more about Strengthening Security with Next-Gen Firewalls.
- DNS Protection: The Domain Name System (DNS) is the internet’s phonebook. DNS protection blocks access to malicious websites by preventing your devices from resolving their domain names, stopping many phishing and malware downloads.
- VPNs for Remote Work: With more employees working remotely, securing access is paramount. Virtual Private Networks (VPNs) create an encrypted tunnel between a user’s device and your company network, ensuring data remains confidential.
- Data Encryption: This is a fundamental component of data protection. Encryption transforms data into an unreadable format, making it unusable to unauthorized parties. It’s crucial for data in transit and at rest. Dive deeper into Effective Data Encryption: Best Practices for Data Protection.
Advanced Endpoint Protection: EDR and Beyond
Endpoints—laptops, desktops, mobile phones, servers—are common attack vectors and potential entry points for attackers.
- Endpoint Detection and Response (EDR): EDR solutions continuously monitor endpoints for suspicious activity, collect data, and enable real-time threat detection, investigation, and response. Key features include:
- Continuous Monitoring: Always watching for anomalies.
- Threat Hunting: Proactively searching for threats that might have bypassed initial defenses.
- Real-time Response: Capabilities to isolate compromised devices, terminate malicious processes, and roll back changes.
- Behavioral Analysis: Identifying unusual patterns of behavior that indicate a threat, rather than just relying on known signatures.
- Forensic Analysis: Providing detailed logs and context to understand how a breach occurred and what was affected.
- AI-powered protection: Leveraging artificial intelligence to identify and block sophisticated threats like ransomware and phishing.
- Beyond traditional antivirus: Traditional antivirus is reactive, checking for known threats. EDR offers a more proactive defense by detecting and responding to threats. For a detailed comparison, see Understanding EDR & XDR for Enhanced SMB Cyber Defense. Also, ask yourself, Can Antivirus Prevent Ransomware?.
Cloud Security vs. On-Premises Solutions
As businesses increasingly use cloud services, understanding cloud-based versus on-premises security is vital.
Cloud-based security leverages cloud provider infrastructure, while on-premises solutions involve hardware and software managed in your own environment.
Here’s a comparison:
| Feature | Cloud-based Security | Traditional On-Premises Security |
|---|---|---|
| Scalability | Highly scalable, adapts to growing needs instantly. | Limited by physical hardware, requires manual upgrades. |
| Cost | Typically subscription-based (OpEx), lower upfront costs. | High upfront costs for hardware, software, and infrastructure (CapEx). |
| Maintenance | Managed by provider, less internal IT overhead. | Requires significant internal IT resources for patches, updates, and monitoring. |
| Accessibility | Accessible from anywhere, ideal for remote work. | Often restricted to internal network, complex for remote access. |
| Flexibility | Rapid deployment, easy integration with other cloud services. | Slower deployment, custom integration can be complex. |
| Expertise | Benefits from the provider’s dedicated security experts. | Relies on in-house expertise, which can be costly to maintain. |
Shared Responsibility Model: Cloud security operates on a “shared responsibility model.” The cloud provider secures the infrastructure, but you are responsible for security in the cloud—your data, applications, and configurations. This includes managing access controls, encryption, and identities. For businesses migrating to the cloud, our insights on Cloud Migration Security can provide a deeper dive.
The Human Element: Your First Line of Defense
People are often the weakest link in cybersecurity, which is why social engineering is so prevalent. However, this also means your employees can be your strongest defense.
- Security Awareness Training: This isn’t a one-time lecture. Effective training is ongoing, engaging, and customized. It should cover recognizing phishing attempts, handling suspicious links, strong password hygiene, reporting suspicious activity, and company data policies. Regular, bite-sized training is far more effective than annual sessions.
- Phishing Simulations: These mock phishing attacks test employee vigilance and provide real-time learning without real risk. They reinforce training and identify areas needing more education.
- Strong Password Policies: Enforcing the use of unique, complex passwords (or better yet, passphrases) for all accounts is fundamental. Combining this with Multi-Factor Authentication (MFA) drastically reduces the risk of credential-based attacks.
- Access Control: The principle of least privilege dictates that employees should only have access to the data and systems absolutely necessary for their job functions. This limits potential damage if an account is compromised.
- Upskilling Benefits: Investing in your IT employees to become cybersecurity pros pays off. A 2024 IBM report found that upskilling retained employees saved businesses an average of $259,000 USD. This strengthens your internal capabilities and saves recruitment costs.
By turning your employees into a “human firewall,” you significantly bolster your overall security posture. We dig deeper into this in Boost Human Security with Cybersecurity Awareness Training. For remote workforces, specific strategies like VPNs and MFA are crucial, as outlined in Strategies for Securing Remote Workforces with VPN & MFA.
How to Choose the Right Cyber Security Solution for Your Business
Choosing the right cyber security solutions for business can feel overwhelming. To decide what’s best for your company in Orlando, Jacksonville, or Plano, start by understanding your unique needs, risks, and goals. This ensures your investment delivers maximum value. We recommend starting with an evaluation, as detailed in How to Conduct a Cyber Security Risk Assessment.
Step 1: Assess Your Unique Risks and Needs
First, understand what you’re protecting and from whom.
- Identify Critical Assets: What data, systems, and processes are most vital to your business? This could include customer databases, intellectual property, or financial records. Understanding What is PII in Cybersecurity is a good starting point.
- Vulnerability Scanning: Conduct regular scans to identify weaknesses in your systems, networks, and applications.
- Business Impact Analysis (BIA): How would a cyber incident affect your business financially, reputationally, and operationally? This helps prioritize investments.
- Threat Landscape Analysis: Research industry-specific threats and common attack methods that target businesses like yours.
Step 2: Key Factors for Selecting a Cyber Security Solution for Your Business
Once you know your risks, evaluate solutions based on these critical factors:
- Integration with Existing Systems (SIEM): Tools shouldn’t operate in silos. Look for solutions that integrate with your current IT infrastructure and SIEM systems for a unified view and simplified response.
- Scalability for Growth: As your business grows, your security should too. Choose platforms that scale easily to accommodate more users, devices, and data without a complete overhaul.
- Vendor Support and Reputation: Choose vendors with a strong track record, positive reviews, and reliable support. A good vendor acts as a partner.
- User Experience (UX): Tools should be effective and user-friendly. Complex interfaces can lead to errors and workarounds. The best controls are often invisible to users, protecting them without hindering productivity.
- Cost-Effectiveness and ROI: Evaluate the total cost of ownership (TCO), including all associated costs. Weigh this against the potential cost of a breach to determine ROI. Prioritize high-impact, low-cost measures first.
For insights into the types of tools managed service providers use, check out Top Cybersecurity Tools for Managed Services Explained.
Step 3: Navigating Compliance and Data Protection Regulations
Compliance is about more than avoiding fines; it’s about building trust and protecting data. Businesses in Florida, Texas, and across the US must adhere to various data protection regulations.
- GDPR (General Data Protection Regulation): While a European regulation, GDPR impacts any business worldwide that processes personal data of EU citizens.
- HIPAA (Health Insurance Portability and Accountability Act): Essential for US healthcare providers, HIPAA sets national standards for protecting patient health information.
- PCI DSS (Payment Card Industry Data Security Standard): Any business that handles credit card data must comply with PCI DSS to ensure secure processing.
- CMMC (Cybersecurity Maturity Model Certification): For businesses working with the US Department of Defense, CMMC is becoming mandatory to ensure adequate cybersecurity.
Many cyber security solutions for business offer features designed to help meet these requirements, such as data encryption, access controls, and audit logging. We guide businesses through this complex landscape, helping them Master Cybersecurity Compliance for IT Managed Services. The Resources from the FTC on Cybersecurity for Small Business are also a great starting point.
The Future of Business Cybersecurity: Trends and Innovations
The cybersecurity landscape is dynamic, constantly evolving with new threats and technologies. Staying ahead means understanding the trends that will shape defense strategies for 2026 and beyond. We’re always looking ahead, as discussed in What is the Future of Cyber Security?.
The Role of AI and Machine Learning in Modern Cybersecurity
AI and Machine Learning (ML) are now integral to modern cyber security solutions for business.
- Predictive Analytics: AI can analyze vast amounts of data to identify patterns and predict potential threats before they materialize.
- Automated Threat Response: AI-powered systems can automatically detect and respond to threats in real-time, isolating infected systems or blocking malicious traffic without human intervention.
- Anomaly Detection: ML algorithms learn “normal” network behavior and flag significant deviations as potential threats.
- Reducing False Positives: Advanced ML models are becoming adept at filtering out benign events, reducing noise for human analysts so they can focus on genuine threats.
AI-based products are crucial for preventing multi-step attack chains and offering adaptive defense.
Embracing a Zero Trust Security Model
The Zero Trust security model is a transformative trend that fundamentally changes network security.
- “Never Trust, Always Verify”: Zero Trust assumes no user or device is trusted by default. Every access request is verified, regardless of location.
- Micro-segmentation: This involves dividing networks into small, isolated segments to contain breaches and prevent lateral movement.
- Principle of Least Privilege: Users and devices are granted only the minimum access rights necessary for their tasks, limiting potential damage.
- Identity and Access Management (IAM): Robust IAM systems are foundational to Zero Trust, ensuring identities are verified and authorized at every access point.
Implementing Zero Trust is a significant shift, but its risk-reduction benefits are substantial. We detail this in The Importance of Zero Trust Architecture for Modern Security.
The Benefits of Using Managed Cybersecurity Services
For many SMBs in Winter Springs, Orlando, or Jacksonville, building an in-house 24/7 cybersecurity team is not feasible. This is where managed cybersecurity services shine.
- Access to Expertise: MSSPs like Cyber Command provide a team of skilled experts—threat hunters, incident responders, and compliance specialists—that most businesses cannot afford to hire individually.
- 24/7 Monitoring and Response: Threats are constant. MSSPs provide round-the-clock monitoring to detect and address suspicious activity immediately, minimizing damage.
- Cost-Effectiveness: Outsourcing is often more cost-effective than an in-house team, considering salaries, training, and tool costs. Our transparent, all-inclusive pricing is predictable and budget-friendly.
- Focus on Core Business: Outsourcing cybersecurity lets your team focus on driving business growth and innovation without the constant worry of cyber threats.
- Proactive Defense: MSSPs use advanced threat intelligence and proactive threat hunting to neutralize threats before they impact your business.
- Compliance Assistance: MSSPs offer guidance and tools to help steer complex regulations like HIPAA, PCI DSS, and CMMC.
We offer enterprise-grade IT, cybersecurity, and platform engineering services, acting as an extension of our clients’ businesses. This proactive, 24/7/365 U.S.-based support is designed to give you peace of mind. To understand more, explore the Benefits of Cybersecurity in Managed Services. You might also find value in Local Managed Service Providers: My Go-To for Cybersecurity.
Frequently Asked Questions about Business Cybersecurity
What are the first steps a small business should take for cybersecurity?
For small businesses, the journey to robust cybersecurity doesn’t have to be overwhelming. Start with the foundational elements:
- Employee Training: Begin with basic security awareness training. As we’ve discussed, your team can be your strongest defense.
- Strong Passwords & MFA: Enforce strong, unique passwords for all accounts and implement Multi-Factor Authentication (MFA) everywhere possible. MFA is one of the most effective controls against credential theft.
- Regular Data Backups: Implement a reliable system for backing up all critical business data, ideally with offsite or cloud storage, and regularly test your restoration process.
- Basic Endpoint Protection: Ensure all devices have up-to-date antivirus/anti-malware software.
For a structured approach, leverage resources like the NIST Small Business Cybersecurity Corner to create a custom plan.
Is antivirus software enough to protect my business?
No, unfortunately, traditional antivirus software alone is no longer enough to protect your business. While essential for catching known malware and viruses, it’s largely reactive. Modern cyber threats, including sophisticated ransomware, zero-day exploits, and AI-driven attacks, can often bypass basic antivirus defenses. A comprehensive approach requires a layered defense that includes:
- Endpoint Detection and Response (EDR): For real-time monitoring, threat hunting, and rapid response on all devices.
- Next-Generation Firewalls (NGFWs): To inspect and filter traffic at a deeper level.
- Email Security Gateways: To protect against advanced phishing and malware delivered via email.
- DNS Protection: To block access to malicious websites.
- Security Awareness Training: To empower your employees to recognize and report threats.
How can my business securely manage remote workers?
Securing a remote workforce in Florida, Texas, or anywhere else requires a dedicated strategy, especially with the increased attack surface. Here’s how we recommend doing it:
- Robust Remote Work Policy: Establish clear guidelines for device usage, data handling, and secure internet access.
- Company-Approved VPNs: Mandate the use of Virtual Private Networks (VPNs) for all remote access to company resources to encrypt data in transit.
- Enforce Strong Authentication (MFA): Require MFA for accessing all company applications, cloud services, and VPN connections.
- Secure Home Wi-Fi Networks: Educate employees on securing their home routers with strong passwords and encryption (WPA2/WPA3).
- Endpoint Protection on All Devices: Ensure all devices used for work, whether company-issued or personal (BYOD), have EDR solutions installed and are regularly patched and updated.
- Secure Collaboration Tools: Use secure, encrypted communication and collaboration platforms.
- Regular Security Training: Continuously train remote employees on remote work-specific threats like unsecured Wi-Fi risks and increased phishing attempts.
Conclusion
In today’s interconnected world, cyber security solutions for business are not just a technical necessity—they are a strategic business investment. From the busy streets of Orlando to the growing tech hubs of Plano, businesses face a relentless barrage of evolving threats. Relying on outdated security measures is like trying to stop a flood with a sieve.
By embracing a proactive, layered security approach that combines advanced technology with a well-trained human element, you can build resilience, protect your valuable assets, and maintain the trust of your customers. Continuous adaptation, informed decision-making, and access to expert guidance are the keys to staying ahead.
At Cyber Command, we’re dedicated to making enterprise-grade cybersecurity accessible and manageable for businesses like yours. With our proactive, 24/7/365 U.S.-based support and transparent pricing, we act as your dedicated cybersecurity extension, ensuring your peace of mind so you can focus on what you do best.
Ready to strengthen your defenses and secure your future? Strengthen your defenses with our comprehensive cybersecurity services.

