Hipaa for Business Associates: A Central Florida Compliance and Cybersecurity Guide
If your company works with clients in the healthcare industry, you've probably heard the term HIPAA Business Associate. It’s a role that often comes as a surprise. Even if you never see a patient, the moment you handle their data, you’re legally on the hook to protect it just as rigorously as a hospital or doctor's office.
This isn’t a minor detail—it’s a serious responsibility with significant cybersecurity risks attached, especially for businesses in Orlando's thriving professional services sector.
Are You a HIPAA Business Associate?

Here's a reality check for many businesses in Orlando, Winter Park, and across Central Florida: HIPAA compliance isn't just for doctors. If your company provides services to a healthcare client and you create, receive, maintain, or transmit their data, you’ve just stepped into the world of Protected Health Information (PHI).
Think of it like this: a hospital or clinic is the "owner" of the sensitive patient data they collect. When they hire you—whether you're an IT provider, a law firm, an accounting practice, or a software developer—they’re entrusting you to be a "custodian" of that data. Under federal law, this makes you a Business Associate (BA), and you become directly liable for keeping that information safe from cyber threats.
Covered Entity vs. Business Associate
It's critical to understand the difference between a Covered Entity (CE) and a Business Associate. The CE is the primary healthcare organization. The BA is the vendor serving that organization. Getting this distinction wrong can lead to crippling fines and a shattered reputation.
A common and costly mistake we see is companies assuming that because they don't provide direct patient care, HIPAA rules don't apply. If you handle PHI for a healthcare client in any way—from IT support for a Winter Park dental office to billing services for an Orlando medical spa—you are on the hook.
To make it even clearer, let's break down who's who in the HIPAA world.
Quick Answer: Who Is a Business Associate?
This table provides a fast way to distinguish between the two primary roles under HIPAA and their core duties.
| Role | Who They Are (Examples) | Primary Responsibility |
|---|---|---|
| Covered Entity (CE) | Hospitals, doctors' offices, dentists, health plans, healthcare clearinghouses. | To provide care and directly protect the PHI they create and manage. |
| Business Associate (BA) | IT providers, law firms, accounting firms, cloud storage providers, medical billing companies. | To protect PHI on behalf of a Covered Entity, as defined in a Business Associate Agreement (BAA). |
This relationship isn't just a handshake deal. It’s a legal requirement cemented by a contract called a Business Associate Agreement (BAA). This document is non-negotiable and spells out your exact duties to safeguard PHI against cyber attacks.
Your Cybersecurity Obligations in Central Florida
For professional service and tech companies in the Orlando area, becoming a Business Associate has massive cybersecurity implications. The moment you sign that BAA, you inherit the responsibility to implement specific safeguards against data breaches.
This isn't optional. You are required to have:
- Administrative Safeguards: This means creating policies and procedures for handling PHI, like documented employee training, risk assessments, and strict access controls.
- Technical Safeguards: This is where modern cybersecurity comes in. You'll need to implement measures like end-to-end encryption, robust firewalls, multi-factor authentication, and secure access protocols to protect electronic PHI (ePHI).
- Physical Safeguards: You must also secure the physical locations and devices where PHI is stored, from locked server rooms to secured workstations and mobile devices.
Ignoring these obligations is a high-stakes gamble. A ransomware attack or data breach that starts with a Business Associate is just as devastating as one from the healthcare provider itself, leading to the same hefty fines and a complete loss of client trust.
The Business Associate Agreement Explained
If handling protected health information (PHI) for a healthcare client makes you a Business Associate, then the Business Associate Agreement (BAA) is your legally binding rulebook. This isn't just another piece of administrative paperwork to sign and file away; it's the contract that underpins your entire HIPAA compliance and cybersecurity strategy. For any Orlando IT firm or Winter Park accounting practice working with healthcare clients, this document is where the rubber meets the road.
Think of it like this: a healthcare provider (the Covered Entity) hands you the keys to their most valuable asset—their patients' private data. The BAA is the detailed contract outlining exactly how you must protect that data, specifying your duties down to the last detail. Signing one without fully grasping these cybersecurity obligations is like agreeing to guard a bank vault without knowing how to work the lock.
Core Components of a BAA
While the exact language can vary, every BAA is required by law to have specific, non-negotiable components. It's a contract that explicitly states you will safeguard the PHI you access, create, or transmit on behalf of the Covered Entity.
A compliant BAA will always clearly define:
- Permitted Uses of PHI: It establishes the only reasons you are allowed to access and use PHI. Any action outside this defined scope is a violation.
- Safeguard Implementation: The agreement legally binds you to implement the required Administrative, Physical, and Technical Safeguards outlined in the HIPAA Security Rule.
- Breach Notification Duties: It outlines your responsibility to report any data breach to the Covered Entity "without unreasonable delay"—a critical and time-sensitive requirement.
- Subcontractor Compliance: It mandates that any of your own vendors or subcontractors who touch the PHI must also sign a BAA and agree to the exact same protections.
The Real-World Risks of a Weak BAA
A poorly written or misunderstood BAA can create staggering liability. Imagine an Orlando-based software company developing a patient portal for a local medical spa. They grab a generic BAA template online, sign it, and assume they're covered.
Six months later, a hacker exploits a vulnerability in their code, exposing thousands of patient records. Because their BAA was vague about incident response timelines and failed to properly address cybersecurity monitoring, they delayed notifying the spa. That delay led to compounded fines from regulators for both the software company and the spa, not to mention a devastating loss of public trust. You can learn more about how different compliance frameworks intersect by exploring our guide on GDPR and HIPAA mapping.
A BAA is not a shield you hide behind—it’s a promise you must actively keep. It contractually obligates you to perform specific cybersecurity actions, and failing to do so is a breach of contract on top of a HIPAA violation.
Vetting Your IT Partner's BAA
When you engage a cybersecurity or managed IT partner, scrutinizing their BAA is one of your most important due diligence steps. It reveals how seriously they take their role as a Business Associate and gives you a window into their operational maturity. A strong IT partner’s BAA should be clear, detailed, and align directly with the proactive services they offer.
Here is a practical checklist for reviewing a BAA from a potential IT provider:
- Does It Explicitly Mention Safeguards? The BAA should clearly state their commitment to implementing and maintaining all three types of HIPAA safeguards, not just mention them in passing.
- Are Breach Reporting Terms Specific? Look for clear language on how and when they will report a security incident to you. Vague phrases like "in a timely manner" are a major red flag.
- Does It Address Audits and Investigations? The BAA must require the partner to make their practices, books, and records available to the Department of Health and Human Services (HHS) for audits.
- Are Termination Clauses Clear? It should specify that you can terminate the agreement if the partner violates a material term of the BAA. This is a critical protection for your business.
A partner whose BAA confidently outlines these duties is one that understands its role. They see the BAA not as a liability to minimize but as a commitment to be upheld through robust, 24/7 security services.
Essential Cybersecurity Safeguards for Business Associates
When you become a HIPAA Business Associate, you take on serious responsibility for protecting electronic Protected Health Information (ePHI). The law requires you to implement specific "safeguards," but this isn't just a technical checklist. It's about building a fortress around sensitive patient data.
Think of it like securing a bank vault. The rules for who gets a key are your Administrative Safeguards. The locks, guards, and alarms are your Physical Safeguards. And the high-tech surveillance and timed locks inside the vault are your Technical Safeguards. For businesses across Central Florida, from legal practices in Orlando to accounting firms in Winter Park, mastering these three pillars is the key to compliance.
Administrative Safeguards The Human Element
Let's be honest—technology can't stop a determined insider or a careless mistake. That's where Administrative Safeguards come in. These are the documented policies and procedures that govern how your team handles PHI.
These aren't "set it and forget it" documents collecting dust on a shelf. They are living, breathing rules that you must actively enforce, review, and update. They are the foundation of your entire security program.
Your administrative checklist needs to include:
- Security Officer Designation: You must officially name a Security Officer. This person is on the hook for creating, implementing, and enforcing your HIPAA security policies.
- Risk Analysis: You're required to perform a thorough and ongoing risk analysis. This process helps you identify potential threats to ePHI and figure out where your vulnerabilities are.
- Workforce Training: Every single employee with access to ePHI must get regular, documented training on your security policies. This is a common failure point during audits, so don't skip it.
- Access Management: You need a formal process for granting, changing, and revoking access to systems with ePHI. The rule of thumb is "minimum necessary"—people should only have access to what they absolutely need to do their jobs.
Physical Safeguards Securing Your Environment
Physical Safeguards are all about protecting the actual hardware and locations where ePHI lives. This means everything from the server in a closet to the laptops your team takes home.
It's easy to get caught up in digital threats, but physical security gaps are a huge risk. A visitor left unescorted could plug a malicious USB drive into a computer. A stolen laptop, if not properly secured, could expose thousands of patient records in an instant.
A critical but often overlooked area is the disposal of old equipment. Highlighting the growing importance of data security in IT asset disposition, it's clear that proper handling of retired hardware is as critical as active cybersecurity. Simply wiping a drive may not be enough.
Key physical safeguards for your business include:
- Facility Access Controls: Implement procedures to control who can physically enter your office, especially sensitive areas like server rooms or data centers.
- Workstation Security: Make sure all workstations that access ePHI are physically secure. This also means ensuring screens aren't visible to people who shouldn't be seeing them.
- Device and Media Controls: Create policies for the secure handling of hard drives, backup tapes, and laptops. This includes how they are moved, reused, and ultimately destroyed when they contain ePHI.
Technical Safeguards The Digital Fortress
Technical Safeguards are the cybersecurity tools and technologies you use to protect ePHI across your network and devices. This is where the tech does the heavy lifting to stop hackers in their tracks.
Cybercriminals are increasingly targeting Business Associates, viewing them as a softer entry point into the healthcare ecosystem. The statistics are clear: vendor-related breaches are soaring. Strong technical controls are no longer optional; they are essential for survival.
Your essential technical safeguards must include:
- Access Control: Every user needs a unique ID and multi-factor authentication (MFA). Your systems should also automatically log users off after a period of inactivity to prevent unauthorized access.
- Audit Controls: You must have systems that can record and examine activity on any system that contains or uses ePHI. If a breach happens, you need to know who did what, and when.
- Integrity Controls: Implement measures to ensure that ePHI is not improperly altered or destroyed, whether by accident or with malicious intent.
- Transmission Security: Use end-to-end encryption to protect ePHI whenever it’s sent over a network. This applies to everything from email to file transfers and cloud applications.
For Central Florida businesses facing these modern threats, a 24/7 Security Operations Center (SOC) has become a vital technical safeguard. A SOC provides the constant monitoring, active threat hunting, and immediate incident response needed to detect and neutralize attacks before they become catastrophic breaches, helping you meet HIPAA’s stringent demands.
Conducting a HIPAA Risk Analysis
Having strong safeguards in place is a fantastic first step, but it’s not the finish line. The HIPAA Security Rule mandates that every Business Associate conduct a regular, thorough Risk Analysis—a process that’s a surprisingly common point of failure and a huge focus for auditors.
This isn’t a friendly suggestion. It's a required process to prove you’ve actually identified and are actively managing the specific security risks your organization faces. Think of it as your strategic map, showing you exactly where your cybersecurity is weak before a hacker finds those same spots for you. It turns compliance from a guessing game into a targeted, evidence-based strategy.
The Four Steps of a Risk Analysis
A proper HIPAA Risk Analysis isn't a one-and-done checklist; it's a living, breathing cycle. It involves methodically combing through your environment to find any potential threat to the ePHI you handle. Here’s a straightforward breakdown of how to get started.
Identify Where All PHI Lives
You can't protect what you don't know you have. The first step is to create a complete inventory of every single system, application, and device that creates, receives, maintains, or transmits ePHI. This includes everything from cloud servers and accounting software to individual employee laptops and email accounts.Pinpoint Threats and Vulnerabilities
Next, you have to identify potential threats to all those assets you just inventoried. A threat could be anything from a ransomware attack or a power outage to a disgruntled employee. Vulnerabilities are the weaknesses that let those threats cause harm, like unpatched software, a lack of multi-factor authentication, or flimsy employee training.Evaluate Likelihood and Impact
With a list of threats and vulnerabilities in hand, it’s time to weigh the risk they pose. For each one, you need to figure out the likelihood of it actually happening and the potential impact if it does. For example, a data breach from a lost, unencrypted laptop might be highly likely and have a catastrophic impact on your business.Document Your Findings Comprehensively
Finally, you must document every single step of your analysis in a formal report. This documentation is your proof of compliance for auditors and serves as the blueprint for your risk management plan.
This whole process has to be repeated regularly—at least once a year or anytime you make significant changes to your IT environment. For a closer look at how to structure your assessment, a good HIPAA Risk Assessment Template can provide some practical examples and guidance.
Why This Process Is Non-Negotiable
Let's be blunt: failing to conduct a proper risk analysis is one of the most frequently cited violations in HIPAA enforcement actions. Regulators see it as a fundamental neglect of your duties as a Business Associate.
The numbers are pretty alarming.
In 2025, a staggering 34% of all healthcare data breaches originated from business associates, the highest percentage ever recorded. These breaches were 2.4 times larger on average than those at covered entities. The OCR's record 22 major enforcement actions in 2025, totaling $148 million in penalties, often stemmed from gaps like inadequate risk analysis, highlighting the critical need for proactive vendor oversight.
These statistics show that regulators are zeroing in on Business Associates and their security practices. A documented Risk Analysis is your first and best line of defense if an auditor comes knocking.
The flowchart below shows how a risk analysis fits into the bigger picture, guiding how you implement Administrative, Physical, and Technical controls.
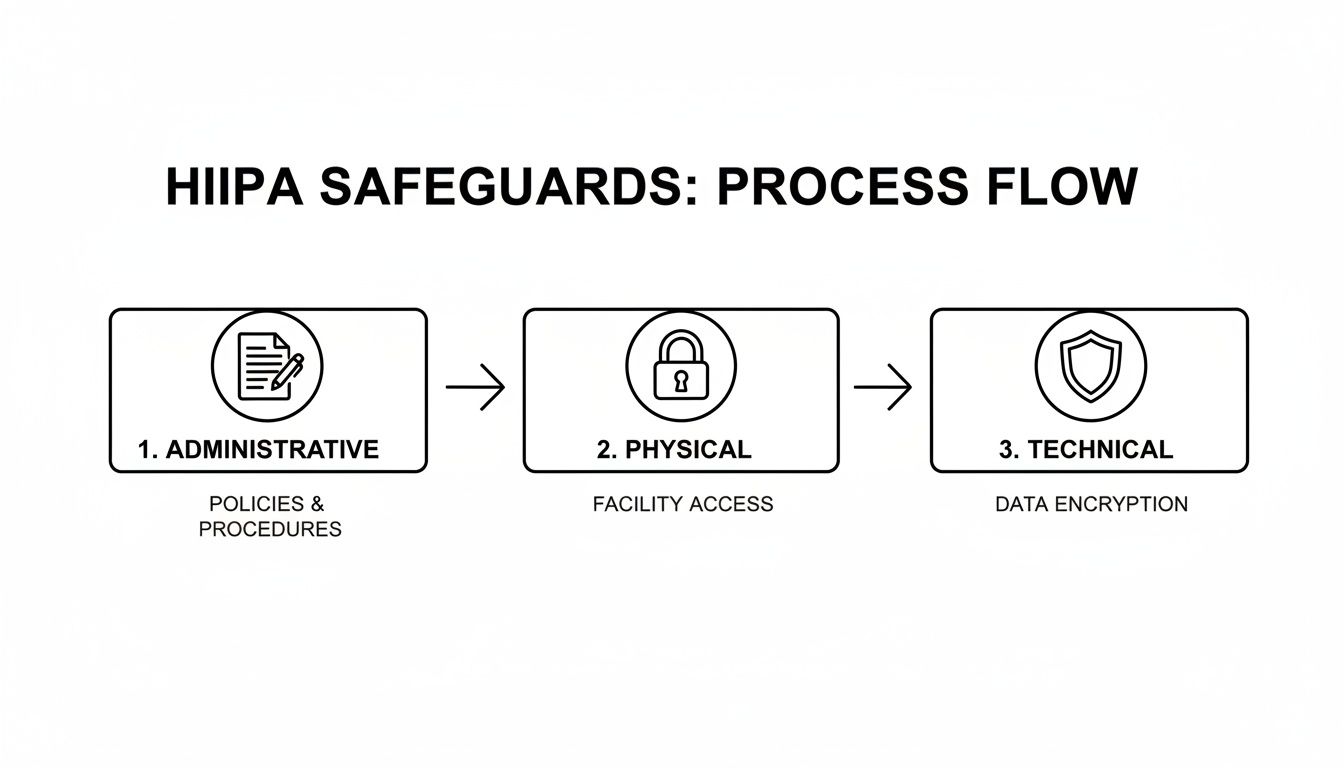
As you can see, the risk analysis isn't an isolated task. It’s the foundation that informs the policies, physical security measures, and technology you need to effectively protect sensitive data.
From Chore to Continuous Strategy
For many small and mid-sized businesses, the idea of conducting such a detailed analysis feels completely overwhelming. It requires specialized knowledge of both the intricate HIPAA rules and the constantly changing world of cybersecurity threats.
This is where partnering with a managed cybersecurity firm changes the entire game.
Instead of being a painful annual project that everyone dreads, a dedicated IT partner transforms risk analysis into a continuous, manageable process. They use advanced tools to actively monitor your systems for new vulnerabilities, bring the expertise to evaluate risks accurately, and generate the detailed documentation you need to prove you’re compliant.
This kind of partnership turns a feared compliance chore into an ongoing security strategy that truly protects your business and your clients' trust.
Your Data Breach Response Plan
It’s the one call every Business Associate dreads, but you have to be ready for it: a data breach involving Protected Health Information (PHI). What you do in the first few hours is absolutely critical. Under HIPAA’s Breach Notification Rule, you have specific, time-sensitive duties that can make or break your company's future.

Think of this as your fire drill for data. When the alarm goes off, panic isn't an option. A calm, methodical response is your only path to minimizing the financial and reputational fallout.
What Legally Constitutes a Breach
First, let’s get clear on what the law actually considers a "breach." Under HIPAA, it's generally any unauthorized acquisition, access, use, or disclosure of unsecured PHI that compromises its security or privacy. The key word here is "unsecured," which almost always means unencrypted.
Not every security hiccup is a legally reportable breach. After you discover an incident, you have to conduct a swift risk assessment to figure out if notification is truly necessary. This is not a step you can skip.
The burden of proof is on you. If you decide an incident doesn't require notification, you must document your risk assessment process meticulously. HIPAA presumes all unauthorized uses of PHI are breaches unless you can prove otherwise.
The Clock Is Ticking: Your First Steps
The moment you even suspect a breach has occurred, your immediate priorities are to contain the threat and kick off your investigation. Your Business Associate Agreement (BAA) legally binds you to notify your Covered Entity client "without unreasonable delay" and in no case later than 60 calendar days from discovery.
Let’s be real, though. Your BAA will almost certainly demand much faster reporting than that.
A well-structured incident response plan ensures you don't miss a beat during this high-pressure chaos. For more details on building a solid framework, check out our guide on crafting your incident response plan for max efficiency. This framework is an essential piece of any HIPAA for business associates compliance program.
Your initial response should follow these key stages:
- Containment: The first move is to stop the bleeding. This might mean isolating affected systems from the network, revoking compromised user credentials, or shutting down specific services to prevent any more data from walking out the door.
- Assessment: At the same time, your team has to start figuring out the scope of the incident. Identify what systems were hit, what data was exposed, and who might have been affected.
- Eradication: Once you've contained the incident, you must get the threat out of your environment. This means eliminating malware, patching the vulnerabilities that let the attacker in, and triple-checking they have no way back.
- Recovery: Finally, it's time to restore affected systems to normal operation from clean, verified backups. This step also includes aggressive post-incident monitoring to watch for any signs of reinfection or lingering malicious activity.
The Central Florida Advantage: A Local Partner
For businesses in Orlando, Winter Park, and the surrounding areas, having a local cybersecurity partner with a 24/7 incident response team is a game-changer. Cyber threats don’t keep 9-to-5 hours. An attack that kicks off on a Friday night can cause catastrophic damage by Monday morning if no one is watching the shop.
A local partner brings a few key benefits to a crisis:
- Rapid On-Site Response: When remote fixes aren't enough, a local team can be on-site in a flash to physically handle servers and network gear.
- Regional Knowledge: A partner who knows the Central Florida business community—from professional services firms in Downtown Orlando to healthcare tech startups in Lake Nona—understands the specific threats and compliance pressures you're up against.
- Direct Communication: In a crisis, you want to talk directly to the experts handling the incident, not a faceless call center on the other side of the world.
By having a dedicated incident response team on standby, you ensure that when a breach happens, you can contain the threat, properly assess the damage, and meet your legal obligations correctly—protecting both your business and your clients.
Choosing the Right IT Partner for Compliance
For many Orlando-area businesses—from law firms and accounting practices to software developers—trying to handle the maze of HIPAA compliance on your own is a recipe for disaster. The combination of relentless cyber threats and dense legal rules makes going it alone a massive risk. The obvious answer is to team up with a Managed IT and Cybersecurity provider, but picking the right one is a business decision you can't afford to get wrong.
Remember, your IT partner isn't just another vendor. The moment they touch PHI, they legally become your Business Associate, and they’re on the hook for the same responsibilities you are. This means your vetting process needs to be far more intense than just comparing prices. You need a partner who gets the unique pressures facing Central Florida businesses and can prove they have the chops to protect your clients’ data and your good name.
Vetting Their Business Associate Agreement
The first real test of any potential IT partner is their own Business Associate Agreement (BAA). A partner who truly understands their role will hand you a BAA that’s clear, detailed, and doesn't try to sidestep their obligations. If you get a vague, one-page template they clearly downloaded, that’s a huge red flag.
When you’re looking at their BAA, keep an eye out for these non-negotiables:
- Explicit Acceptance of Responsibility: The agreement has to state, in no uncertain terms, that they accept their role as a Business Associate under HIPAA and are responsible for putting the required safeguards in place.
- Specific Breach Notification Terms: The contract must spell out how and when they will tell you about a security incident. Don’t settle for "without unreasonable delay"—look for specific timelines.
- Commitment to Audits: The BAA has to obligate them to cooperate with federal auditors from the Department of Health and Human Services (HHS) if they come knocking.
A solid BAA is a sign of a mature, compliance-first organization. It means they’ve done their homework and invested the legal resources to get it right.
Non-Negotiable Cybersecurity Services
Paperwork is one thing, but your partner has to deliver the actual cybersecurity services that back up those contractual promises. The threat landscape for businesses in Central Florida is no joke, and your partner’s toolset has to be ready for today’s challenges.
A predictable, flat-rate pricing model is often a strong indicator of a proactive partner. When a provider is paid a fixed fee, their incentive is to prevent problems, not profit from fixing them after they occur. This aligns their business model with your goal of maintaining security and uptime.
At a bare minimum, your partner must provide:
- A 24/7/365 Security Operations Center (SOC): Hackers don’t stick to a 9-to-5 schedule. A dedicated SOC gives you around-the-clock monitoring, active threat hunting, and immediate incident response to shut down attacks before they become devastating breaches.
- Proactive Vendor Risk Management: Your IT partner should be helping you manage the risk that comes from your other vendors. They need a process for checking the security of other software and service providers that plug into your network.
- Documented Risk Analysis: As your partner, they should play a key role in performing and documenting your annual HIPAA Risk Analysis, giving you the proof you need to satisfy auditors.
Choosing the right firm is a major step. To help you with your decision, we've laid out more expert advice in our guide on how to choose the right managed service partner. This partner should become a true extension of your team, making sure their technology strategy lines up perfectly with your compliance duties and business goals.
Frequently Asked Questions About HIPAA
When it comes to HIPAA, a lot of questions pop up, especially for Business Associates. For business owners in Orlando and right across Central Florida, getting straight, no-nonsense answers is what really matters. Here are some of the most common questions we hear.
My Orlando Business Only Has a Few Healthcare Clients. Do We Really Need to Worry About HIPAA?
Yes, absolutely. The number of healthcare clients you have is irrelevant. If you handle, store, or simply have access to Protected Health Information (PHI) for even one client, you are a Business Associate in the eyes of the law.
That means you're on the hook for full compliance with the HIPAA Security and Privacy Rules. A single breach, no matter how small your company is, can trigger devastating fines and burn the reputation you've worked so hard to build.
What Is the Biggest Cybersecurity Mistake a New Business Associate Can Make?
The most dangerous mistake we see is treating a signed Business Associate Agreement (BAA) like a finish line. In reality, the BAA is just the starting gun. It’s the contract that legally binds you to do the work—the real work is implementing and maintaining the required administrative, physical, and technical safeguards.
Thinking the agreement itself is the protection is a classic, and costly, error. The BAA is your promise to act, not a substitute for action. Forgetting that is the fastest way to a compliance failure.
How Does a Managed IT Partner Help During a HIPAA Audit?
A compliance-savvy managed IT partner is your single most important ally during a HIPAA audit. They're the ones who produce the mountain of documentation you'll need, from risk analysis reports and security incident logs to proof of employee training.
A partner with a 24/7 Security Operations Center (SOC) is even better. They can show an auditor hard evidence of continuous network monitoring and active threat detection. They become your technical expert, confidently answering the auditor's questions about your cybersecurity posture and proving that your safeguards aren't just policies on paper—they're active and working. It turns a nightmare audit into a calm, evidence-based review.
Navigating your HIPAA obligations as a business associate demands a dedicated cybersecurity partner. Cyber Command, LLC arms Central Florida businesses with 24/7 SOC protection and compliance-focused IT management so you can meet your duties with confidence. See our proactive approach for yourself at https://cybercommand.com.