Runbook Vs Playbook For IT And Cybersecurity
In the world of IT and cybersecurity, you’ll often hear the terms runbook and playbook thrown around, sometimes interchangeably. But make no mistake, they are not the same thing. Getting the difference is critical, especially when the pressure is on.
So, what’s the real story in the runbook vs playbook debate? A runbook is a tactical, step-by-step guide for a known, repeatable task. A playbook is a strategic plan for navigating a complex, often unpredictable event.
Think of it this way: a runbook shows you precisely how to change a flat tire, with every single step laid out. A playbook tells your team what to do and who does it when the whole car breaks down in the middle of a hurricane.
Runbook Vs Playbook What Florida Businesses Must Know
For businesses across Central Florida—from professional services firms in Orlando to healthcare providers in Winter Springs and legal practices in Lake Mary—this isn't just semantics. It’s the key to operational stability and resilience against ever-present cyber threats. These documents work together, but they serve very different masters. A runbook ensures routine work is done right every time, while a playbook guides your team through a full-blown crisis like a ransomware attack or data breach.
Before we get into the nitty-gritty, it helps to understand the core meaning of a playbook and its role in guiding high-level strategy. In cybersecurity, this clarity can be the difference between quick containment and a breach that spirals out of control, crippling your operations.
Consider that 74% of breaches involve a human element. When teams follow a precise runbook for a specific task, they can cut response times by up to 40% by eliminating decision paralysis. That’s a massive advantage when you’re trying to stop a business-crippling attack. We build these principles into how we deliver IT for Florida businesses, which you can learn more about in our business IT support Florida guide.
Runbook Vs Playbook At A Glance
To put it all into perspective, this table breaks down the core differences between a runbook and a playbook.
| Attribute | Runbook | Playbook |
|---|---|---|
| Purpose | To execute a specific, repeatable IT task with detailed steps. | To orchestrate a high-level response to a complex incident. |
| Focus | Tactical ("How to do it") | Strategic ("What to do and who does it") |
| Predictability | High; follows a known, linear process. | Low; adapts to a dynamic, unpredictable event. |
| Use Case | New user onboarding, server patching, data backup. | Ransomware attack, data breach, major service outage. |
| Content | Checklists, command sequences, step-by-step instructions. | Roles, communication plans, decision trees, escalation paths. |
As you can see, a runbook's power is in its precision. It removes any guesswork from routine but critical processes like managing user access or applying security patches. By standardizing these actions, you crush the potential for human error and keep your operations consistent—a vital cybersecurity concern for any business.
A playbook, on the other hand, is your strategic blueprint for survival during a security event. It provides the high-level coordination needed to manage chaos, protect assets, and maintain business continuity when things go sideways.
Ultimately, you don't choose between a runbook or a playbook; a mature organization needs both. The runbook is the "doing" part, and the playbook is the "coordinating" part. Together, they create a complete system for managing both your day-to-day IT operations and the unexpected threats that keep business owners in cities like Orlando and Sanford up at night.
The Role Of Runbooks In Proactive IT Operations
If playbooks are for the five-alarm fires, then runbooks are the meticulous daily checklists that prevent those fires from ever starting. They’re the unsung heroes of day-to-day IT, the detailed, step-by-step instruction manuals that ensure routine tasks get done right—every single time. For businesses across Central Florida, from professional services firms in Orlando to busy medical practices in Winter Springs, this predictability is the bedrock of a stable and secure operation.
Think of a runbook as the pre-flight checklist for your IT team. Just like a pilot verifies every system before takeoff, a runbook guides your technicians through critical, repeatable procedures. It’s this methodical approach that keeps your systems online and your compliance obligations met, directly addressing cybersecurity concerns around consistency and reliability.
The real value of a runbook is simple: it kills inconsistency. By standardizing tasks, you dramatically cut down on the risk of human error—a factor in a whopping 74% of all data breaches.
Without a runbook, something as simple as onboarding a new hire can turn into a security liability. One tech might remember to set up multi-factor authentication; another forgets, leaving a gaping hole. A runbook makes sure every crucial step is followed without fail.
Turning Repetitive Tasks Into Reliable Processes
Every business has IT tasks that are absolutely non-negotiable. They have to be done, and they have to be done on a schedule. Runbooks take these obligations from being potential headaches and turn them into streamlined, documented processes with clear, prescriptive guidance that anyone on your team can follow.
Common tasks that are perfect for runbooks include:
- New User Onboarding: Detailing every step from creating an account and assigning permissions to configuring their endpoint device and providing security awareness training.
- System Health Checks: A daily or weekly procedure to verify server performance, check disk space, and ensure critical services are running properly.
- Secure Data Backups: Outlining the exact process for initiating, verifying, and testing data backups to guarantee recoverability when you need it most.
- Server Patching: A documented sequence for applying security patches, including pre-patch checks, the update itself, and post-patch verification to prevent unexpected downtime and close security vulnerabilities.
For businesses with strict compliance needs, like healthcare providers in Florida adhering to HIPAA or legal firms protecting client data, these documents are essential. A runbook for managing patient data access creates a clear, auditable trail that shows regulators you’re doing your due diligence. This documented consistency is a cornerstone of any serious security program.
Automation And The Future Of Runbooks
Here’s where runbooks go from being just useful to being a game-changer: automation. Many of the step-by-step instructions inside a runbook—like running a script, restarting a service, or applying a patch—are prime candidates for automation. This is where the concept of proactive IT management really comes alive.
When you start automating runbook execution, a few powerful things happen. First, you free up your skilled technicians from mind-numbing, repetitive work. Instead of spending hours patching servers or onboarding users, they can focus on strategic projects that actually grow the business. An expert in proactive IT management can help pinpoint which runbooks will give you the biggest bang for your automation buck. To dig deeper on this, you can learn more about what goes into a proactive IT management strategy.
Second, automation performs these tasks faster and with more accuracy than any human ever could. This means security patches get applied sooner, shrinking your window of vulnerability to near zero—a critical cybersecurity advantage.
This blend of detailed documentation and smart automation lets your Orlando or Winter Springs business scale its operations securely. As your company grows, your standardized, automated processes make sure your IT infrastructure stays stable, compliant, and ready for whatever comes next—without completely overwhelming your team.
The Strategic Power Of Playbooks In Incident Response
While runbooks are your go-to for handling routine, predictable tasks, playbooks are forged in the fires of a crisis. When a security incident like a phishing attack or ransomware infection blows up, a playbook is the high-level strategic guide that coordinates the entire response. It’s what turns sheer panic into a measured, effective defense.
For Central Florida businesses, especially those in regulated industries like healthcare in Winter Park or legal services in Lake Mary, having a playbook isn't just a good idea. It's a core component of business survival.
Imagine a phishing attack rips through an Orlando law firm, putting sensitive client data at risk. Without a playbook, the scene is pure chaos. Who's in charge? What's the very first thing we do? How do we talk to clients and regulators without making things worse? This confusion bleeds time—and time is an attacker's greatest ally.
A well-crafted playbook cuts through that paralysis. It provides a clear, strategic framework that answers the big-picture questions before the crisis hits. It’s less about specific technical commands and more about orchestrating the people, processes, and communications needed to navigate the storm.
Key Components Of A Cybersecurity Playbook
A truly robust playbook is much more than a simple checklist. It’s a comprehensive game plan that gets your organization ready for the messiness of a real-world security breach. The strategic value of playbooks really shines when you're building out a full security incident response planning document.
Your playbook absolutely must include:
- Defined Roles and Responsibilities: This clearly states who owns what. You need a designated Incident Commander, technical leads for containment, legal counsel for compliance issues, and a communications lead to manage stakeholder updates. No more pointing fingers.
- Clear Communication Plans: This outlines how, when, and what to communicate to internal teams, executives, clients, and regulatory bodies. For a healthcare provider in Winter Springs facing a data breach, this plan ensures HIPAA notification requirements are met to the letter.
- Escalation Protocols: This defines the specific triggers for escalating an incident. For example, if a breach is confirmed to involve protected health information (PHI) or client financial data, the playbook automatically loops in legal and compliance teams.
- Post-Incident Review Procedures: It mandates a formal "post-mortem" after every incident. The goal is to identify lessons learned and update the playbook, making the organization tougher and more resilient for the next time.
This structured approach is what separates a controlled response from a catastrophic failure. By getting these elements sorted out in advance, businesses can dramatically reduce the impact of an attack. Our guide on crafting your incident response plan for max efficiency dives deeper into building these critical documents.
Playbooks And Business Survival
The link between having a playbook and minimizing damage is direct and measurable. When a data breach hits, every second counts. A playbook delivers the pre-approved strategy that allows for rapid, confident decision-making, which directly slashes the financial and reputational cost of the incident.
A 2026 IBM Cost of a Data Breach report pegs average breach costs at $4.88 million globally, but firms with structured playbooks slash that by 28% through predefined scenarios.
Those savings come from pure efficiency. Real-world stats from CrowdStrike's 2026 Falcon OverWatch show playbooks enabled 65% of SOCs to triage alerts in under 10 minutes, compared to a sluggish 45 minutes without one. For a medical practice like a dentist or veterinarian, compliance playbooks ensure HIPAA is followed, with post-incident reviews cutting future risks by 52%, according to NIST frameworks.
These aren't just numbers on a page; they show how a strategic plan pays for itself many times over.
Ultimately, a playbook is your organization’s roadmap for navigating its worst day. It ensures that when a security incident occurs, your team isn't just reacting—they're executing a well-rehearsed strategy designed to protect your assets, preserve your brand, and keep the business running.
How Runbooks And Playbooks Work Together In A Crisis
The real magic in the runbook vs playbook debate isn’t about picking a winner. It’s about understanding how they snap together perfectly when things go wrong. A playbook sets the strategy, while runbooks provide the tactical, hands-on-keyboard execution. Together, they turn a high-stress, chaotic event into a calm, controlled process.
Let’s walk through a real-world scenario to see how this powerful duo works.
An Incident In Orlando
Picture a mid-sized engineering firm in Orlando on a typical Tuesday morning. Suddenly, their Security Operations Center (SOC) gets a high-priority alert: a critical server holding project data has triggered a malware warning. Without a plan, this is where panic starts. But this firm is prepared with both playbooks and runbooks.
The second that alert fires, the Cybersecurity Incident Response Playbook is activated. This isn't a technical manual; it's the strategic command document.
The first step in the playbook is all about preventing confusion by assigning clear roles:
- Security Analyst (Responder): The person on the keyboard responsible for the technical investigation and containment.
- IT Manager (Coordinator): The central point of contact who wrangles resources and keeps stakeholders in the loop.
- Leadership (Informed Party): Kept updated on a need-to-know basis to make any high-level business decisions.
This simple, immediate step eliminates the "who's doing what?" paralysis that can cripple an incident response before it even starts.
The Playbook Calls A Runbook
With roles assigned, the playbook lays out the immediate strategic goal: Contain the threat and assess the scope. It doesn't waste time listing the fifty technical commands required to do this. Instead, it directs the Security Analyst to a specific, pre-approved procedure.
Playbook Instruction: "Security Analyst, execute Runbook-MAL-01: Isolate and Analyze Compromised Host."
The analyst now opens the runbook. This document is the polar opposite of the high-level playbook. It’s a hyper-detailed, step-by-step checklist that ensures no critical containment step gets missed in the heat of the moment.
This runbook contains explicit, repeatable instructions:
- Disconnect Network Interface: A guide to surgically remove the server from the network and stop the malware from spreading.
- Block Malicious IP: The exact commands to add the attacker's IP address to the firewall blocklist.
- Collect Volatile Data: Steps for capturing live memory and running processes for forensic analysis later.
- Initiate Endpoint Scan: The procedure to kick off an in-depth antivirus scan on the now-isolated machine.
By following this runbook, the analyst performs the technical work with speed and precision. There’s no guesswork and no room for error. This clean separation—playbook for strategy, runbook for tactics—is the engine of an effective incident response.
This visual shows the high-level flow initiated by the playbook, moving from the initial alert to the strategic response and on to the containment actions.
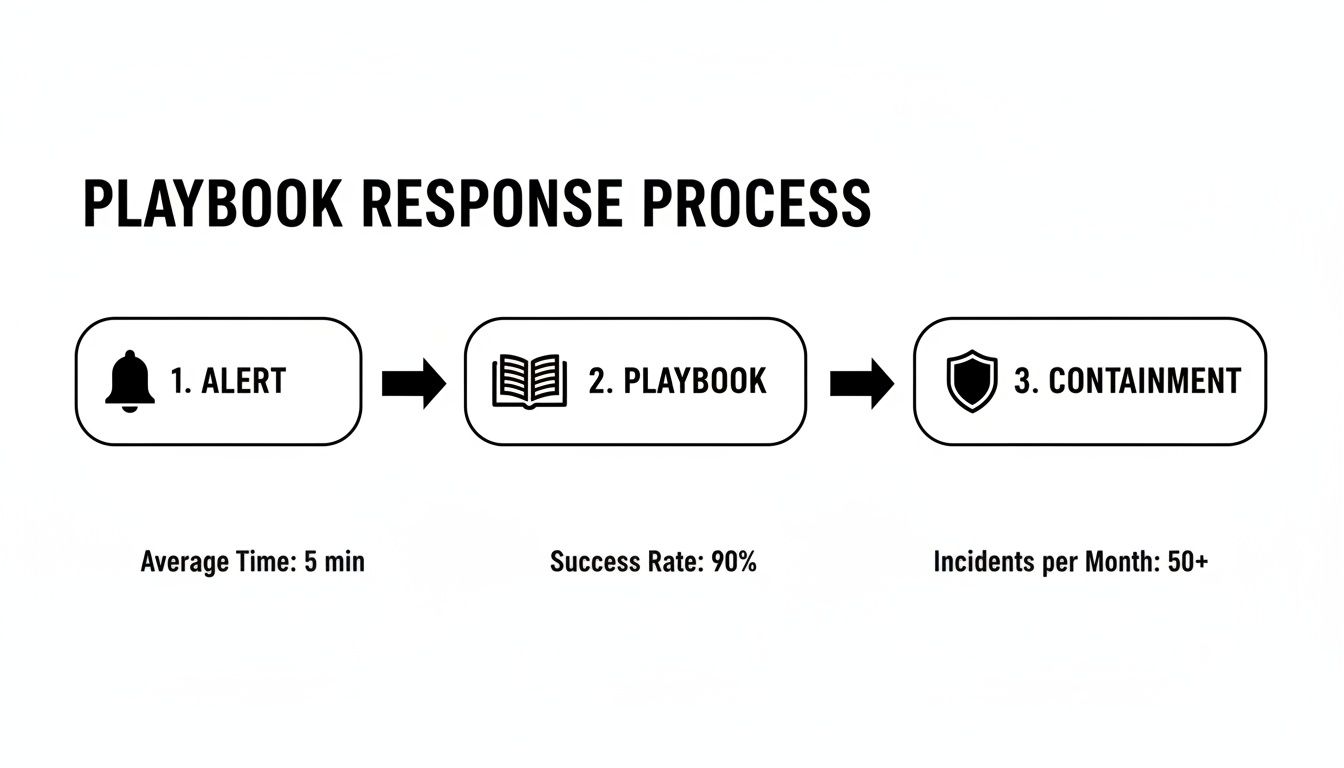
As you can see, a structured playbook response immediately channels a security alert toward decisive, well-organized containment actions.
Strategic Decision Points
Once the runbook tasks are done, control flows back to the playbook. The analyst reports their findings to the IT Manager: the malware was successfully contained to a single server and didn't spread.
Now, the playbook acts like a choose-your-own-adventure guide, presenting a strategic decision tree based on the runbook's outcome:
- If Threat is Contained: The playbook directs the team to the recovery phase. It instructs them to execute Runbook-REC-03: Restore Server from Clean Backup. This kicks off another set of detailed steps for wiping the compromised machine and restoring data from a trusted source.
- If Threat is NOT Contained: Had the malware spread, the playbook would have triggered a completely different path. It would dictate an immediate escalation to a senior security engineer, activate the Crisis Communication Plan to notify clients, and possibly engage a third-party incident response firm.
This is the critical difference in the runbook vs playbook relationship. The runbook executes a task. The playbook makes decisions based on the results of that task.
In our Orlando engineering firm’s case, the threat was contained. The team successfully follows the "Restore from Backup" runbook, bringing the server back online cleanly. Finally, the playbook mandates a post-incident review where the team discusses what went well and identifies any updates needed for the playbook or runbooks. This cycle of execution, decision-making, and improvement turns a potential disaster into a manageable, documented event, protecting the business from costly downtime and reputational damage.
Implementing The Right Solution For Your Florida Business

For business leaders in Orlando, Winter Springs, and across Central Florida, the whole runbook vs playbook conversation eventually boils down to one critical question: do you build these yourself, or do you partner with an expert? The DIY route might look tempting on the surface, but let's be honest about the immense resources it demands.
Creating effective runbooks and playbooks from scratch isn't a weekend project you can just knock out. It requires a serious internal investment of time, specialized talent, and ongoing upkeep. You need people who have a deep, technical understanding of every system for your runbooks and the strategic mind of a veteran security analyst for your playbooks.
The Real Cost of Building In-House
Trying to create and maintain a full library of IT and security documentation is a massive undertaking. For most small to mid-sized businesses, the internal commitment is frankly overwhelming. It pulls your best people away from their actual jobs—the ones that generate revenue.
Here's what you're really signing up for:
- Expertise: You need senior-level IT and cybersecurity pros who get your specific industry—whether that's a law firm in Sanford, a healthcare clinic in Kissimmee, or an engineering firm in Orlando—and also understand the wider threat landscape.
- Time: Just the initial creation process can eat up hundreds of hours. This means mapping out every process, writing painfully detailed procedures, and then testing every single step to make sure it's accurate.
- Ongoing Maintenance: Technology and threats never stand still. Runbooks need updating with every patch or configuration change, and playbooks need constant review and testing to have any real-world value.
For many Florida businesses, this adds up to a huge, unpredictable capital expense. The risk of creating documents that are outdated or just plain wrong is high, and that can leave you even more vulnerable than when you started.
A Smarter Path Forward for Florida Businesses
There’s a much more practical and financially sound alternative to the "build" approach. When you partner with a managed cybersecurity and IT provider, you get immediate access to a mature, battle-tested library of runbooks and playbooks. Even better, you get the 24/7 Security Operations Center (SOC) team needed to execute them flawlessly.
This partnership flips a massive capital expenditure into a predictable, flat-rate operational cost. Instead of guessing how much it will cost to build and maintain your own documentation, you get a clear, manageable monthly expense that delivers real results.
For industrial firms and public sector organizations where uptime is everything, the choice between a runbook and a playbook comes down to operations versus strategy. Just look at the disastrous 2022 Optus breach in Australia. It exposed 10 million records and dragged on for three weeks because their documentation was a mess. The post-mortem pointed to a lack of effective runbooks, which blew recovery costs up to AUD 1.5 billion.
In sharp contrast, businesses that partner with a managed provider often see uptimes exceeding 99.7%. SANS data also shows these hybrid approaches can slash compliance audit failures from a staggering 40% to just 12%. You can dig into more data on how structured documentation impacts recovery in this in-depth analysis from Cortex.
This model lets you and your team focus on your core mission instead of trying to become experts in cybersecurity documentation on the side.
By working with a dedicated partner, your Orlando-based engineering firm or Winter Springs medical practice can lock down its operations with confidence. You get the benefit of proven best practices and a team of experts whose only job is to protect your business, making sure you’re ready for both routine IT needs and unexpected security crises. This frees you up to do what you do best: running and growing your business.
Frequently Asked Questions About Runbooks And Playbooks
For business owners and IT managers across Central Florida, moving from the theoretical runbook vs. playbook concept to actually implementing them raises a lot of practical questions. We hear them all the time. Here are the answers to the most common concerns we field from companies in Orlando, Winter Springs, and beyond.
Can Our Small Business Create Its Own Runbooks And Playbooks?
The short answer is yes, you can. The real question is whether you should. Building these documents from scratch is a massive project that often pulls your most valuable people away from the work that actually generates revenue.
An effective runbook demands deep, system-level knowledge of every piece of tech you rely on, from servers to software. A strong playbook, on the other hand, requires high-level cybersecurity expertise to think like a threat actor and map out a coordinated defense. For most small and mid-sized businesses, the time, effort, and specialized skills needed make the DIY route a serious operational drag.
Partnering with a managed cybersecurity provider is a much more efficient path. You get immediate access to a library of battle-tested documents and the expert team needed to execute them, turning a large, unpredictable capital project into a predictable operational cost.
How Much Of A Runbook Or Playbook Can Be Automated?
A surprising amount, especially when it comes to runbooks. Their step-by-step, tactical nature makes them perfect candidates for automation using Security Orchestration, Automation, and Response (SOAR) platforms.
Many critical actions can be fully automated, including:
- Isolating a compromised device from the network to stop a threat in its tracks.
- Blocking a malicious IP address at the firewall level across your entire infrastructure.
- Enriching a security alert with threat intelligence from multiple sources.
This kind of automation collapses response times from minutes down to seconds. Playbooks also rely on automation for the initial legwork, like gathering data and triaging alerts, but human strategy remains essential. A machine can't decide when to escalate an incident to the leadership team or when to trigger the crisis communication plan. The winning approach always combines machine-speed execution with human-led strategy.
How Do Runbooks And Playbooks Help With HIPAA Compliance?
For medical practices in Florida operating under the strict gaze of HIPAA, runbooks and playbooks aren't just a good idea—they're fundamental to demonstrating due diligence. They provide the auditable proof that regulators will demand during an investigation.
Runbooks act as your documented logbook, proving you perform required security tasks consistently. This covers procedures for access control, system patching, and data backups. When an auditor asks how you ensure only authorized staff can access protected health information (PHI), you can hand them the runbook.
A playbook, meanwhile, is your documented incident response plan—a specific requirement of the HIPAA Security Rule. If a data breach occurs, producing your playbook and the execution logs from your runbooks is critical for minimizing liability and dodging those steep financial penalties. It proves you were prepared, not just reacting to a disaster.
How Often Should These Documents Be Updated?
Think of these as living documents, not dusty binders on a shelf. The update schedule depends entirely on what they're used for.
- Runbooks are tactical and tied directly to your technology. They need constant attention—at least quarterly, and more importantly, every single time a system configuration changes. An outdated runbook is worse than having none at all; it's a liability waiting to cause errors during a real crisis.
- Playbooks are strategic, making them more stable. They should be reviewed at least once a year to make sure they still align with your business goals and the current threat landscape. The absolute most important time to update a playbook is right after a major security incident.
A post-incident review is the perfect opportunity to find the gaps in your strategy and refine the playbook based on its real-world performance. You should also be running regular tabletop exercises—simulated crisis scenarios—to pressure-test your playbooks and make sure your team is ready to execute when it counts.
At Cyber Command, LLC, we help Central Florida businesses move beyond theory and implement practical, battle-tested runbooks and playbooks that protect their operations. Our 24/7 SOC and expert IT team don't just write documents; we execute them, giving you the peace of mind that comes with a proactive, managed cybersecurity partnership. To learn how we can secure your business with a predictable, all-inclusive model, visit us at cybercommand.com.