What Is a HIPAA Officer? A 2026 Guide for FL Businesses
TL;DR: A HIPAA Officer is the person your practice designates to own HIPAA compliance under federal law, and HIPAA requires covered entities and business associates to designate a Security Officer under 45 CFR 164.308. In practice, that role may be split into Privacy and Security functions, handled by one person, or outsourced in part to a qualified partner, especially when a small Florida practice needs technical protection for ePHI without building a full in-house compliance team.
You might be running a dental office in Orlando, a med spa in Winter Springs, or a specialty clinic somewhere in Central Florida and assuming your EHR vendor, copier lease company, and IT guy have compliance covered. They don't. Software helps. Vendors matter. But HIPAA still expects your practice to designate someone who owns the work.
That is the answer to what is a hipaa officer. It's not a ceremonial title and it's not just an IT assignment. It's the person responsible for making sure patient information is handled lawfully, securely, and consistently across the business.
Your Practice's First Line of Defense Against HIPAA Fines
Monday morning in a busy Orlando practice often starts the same way. The front desk wants to use a new texting app, a provider needs records sent to a specialist, and someone assumes the EHR vendor or IT company already approved the process. That is usually the moment a compliance gap shows up.
HIPAA problems start small. A form goes to the wrong inbox. A former employee still has access. A vendor gets connected to systems before anyone checks the contract or security controls. Without clear ownership, those gaps turn into patterns.
The role is mandatory, not optional
HIPAA requires covered entities to designate a Security Officer under 45 CFR 164.308. For a small practice, that requirement matters because responsibility has to sit with a named person, even if parts of the work are handled by outside specialists.
Owners often assign HIPAA to whoever handles computers. That creates blind spots. Technical safeguards matter, but HIPAA compliance also includes policies, training, vendor oversight, incident response, and daily decisions about how staff use and disclose patient information. If you want a practical view of how these duties connect across regulations and business operations, this HIPAA and GDPR compliance mapping guide for businesses is a useful reference.
A good HIPAA program has an owner.
That owner does not need to personally configure firewalls, review logs, or run endpoint detection tools. In many Florida practices, the better model is internal accountability paired with outsourced technical security. The practice keeps decision-making authority with a Privacy or HIPAA lead, and a managed IT or SOC partner handles the security operations the office cannot run in-house.
Why owners should care now
The financial risk gets attention, but day-to-day disruption is usually what hurts first. One privacy complaint, one lost laptop, or one bad vendor decision can force a scramble through policies, access records, training logs, and business associate agreements. If that documentation is scattered or outdated, the practice has a much harder time defending its decisions.
A designated HIPAA Officer helps prevent that mess by keeping a few things under control:
- Accountability: One person tracks policies, decisions, and follow-through.
- Operational discipline: Staff know who approves new tools, reviews workflows, and answers privacy questions.
- Documentation: Risk assessments, training records, vendor files, and incident notes stay current enough to use when you need them.
- Coordination with outside experts: Your managed IT or SOC partner can handle technical safeguards, but someone inside the practice still has to set priorities, approve access, and make sure the work matches HIPAA requirements.
Public-facing systems also create exposure. If your website collects appointment requests, intake details, or any health-related information, you need to understand what HIPAA compliant web design requires before a marketing tool turns into a privacy issue.
What works and what fails
What works is straightforward. Assign the role to someone with authority. Give that person time to do the job. Back them with outside security support if your practice does not have internal technical depth.
What usually fails is predictable:
- The title-only assignment: The office manager gets the role, but no training, no time, and no authority to enforce changes.
- The IT-only approach: Systems are patched and monitored, but patient complaints, disclosure rules, and staff behavior get little attention.
- The binder-on-a-shelf program: Policies exist, but access reviews, vendor checks, and incident preparation never happen in practice.
Ownership is the first line of defense.
The Two Faces of Compliance Privacy vs Security Officer
Most small practices use the term HIPAA Officer as if it means one job. In reality, it usually covers two different functions. That distinction matters because privacy problems and security problems don't start the same way, and they aren't fixed by the same person.
The Privacy Officer protects patient rights and controls how PHI is used and disclosed. The Security Officer protects electronic PHI and focuses on the systems, access, and safeguards that keep it secure.
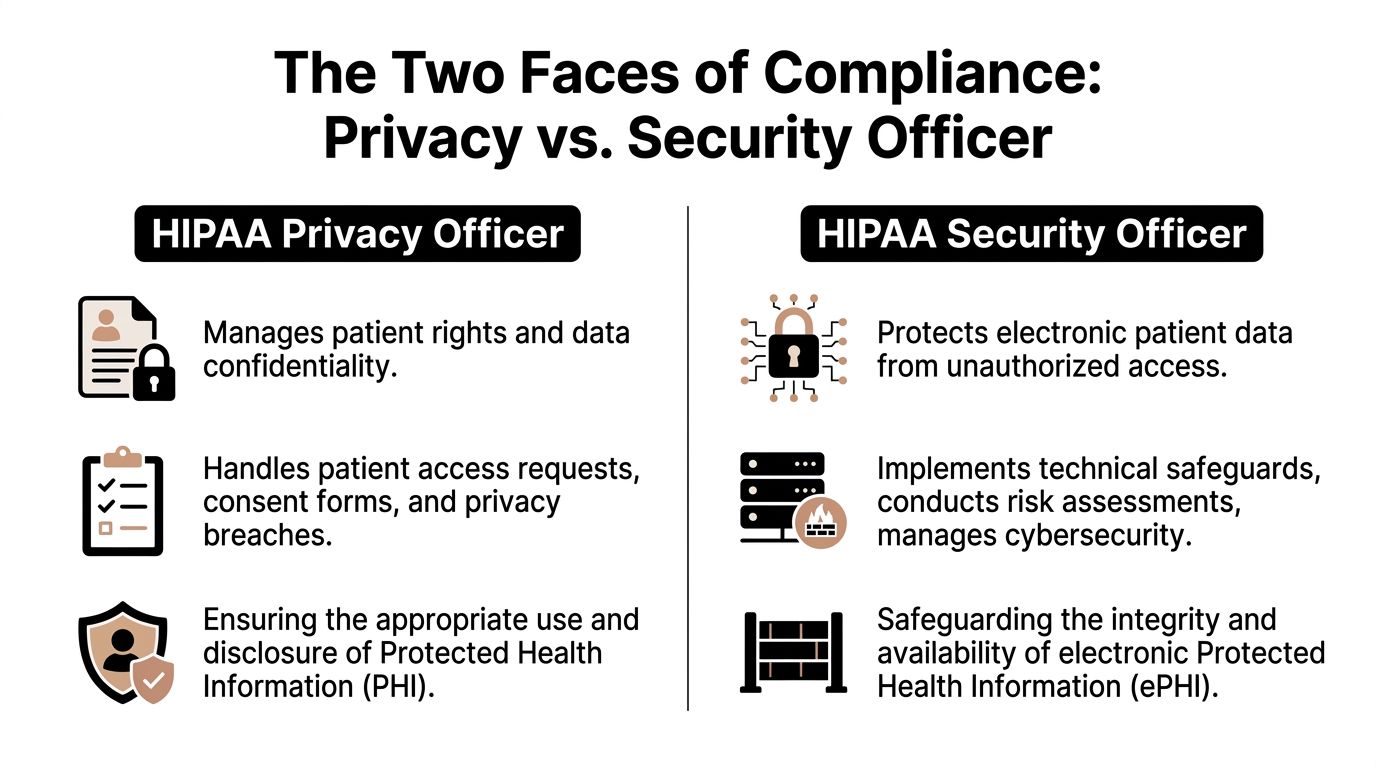
What each role is really doing
Think of the Privacy Officer as the person who governs who should see patient information and why. Think of the Security Officer as the person who makes sure unauthorized people can't get to electronic data in the first place.
The distinction isn't academic. The Privacy Officer deals with patient requests, disclosures, notices, and internal misuse. The Security Officer deals with access controls, monitoring, recovery planning, and technical risk.
According to Atlan's explanation of the HIPAA Privacy Officer role, the Privacy Officer focuses on patient rights and minimum necessary standards, which can reduce data exposure risk by 70%. The Security Officer handles technical safeguards for ePHI, including disaster recovery and vendor due diligence, and HHS data cited there shows a 25% drop in violations for audited entities with dedicated officers.
HIPAA Privacy Officer vs Security Officer Key Differences
| Responsibility Area | HIPAA Privacy Officer | HIPAA Security Officer |
|---|---|---|
| Primary focus | Patient rights and lawful PHI use | Protection of electronic PHI |
| Typical issues handled | Improper disclosures, access requests, privacy complaints | Unauthorized access, weak controls, system safeguards |
| Main workflows | Notices, consent handling, minimum necessary, staff privacy practices | Risk management, access control, recovery planning, security oversight |
| Daily mindset | Who should access this information, and under what rules | How do we prevent, detect, and respond to threats against ePHI |
| Common owner in a small practice | Practice administrator or office manager | IT leader, security lead, or outsourced security partner |
Can one person do both
Yes. HIPAA allows one person to serve both roles, and many smaller clinics do exactly that.
But legal permission isn't the same as practical effectiveness. One person can hold both titles if they have time, authority, and enough range to handle privacy operations and technical security oversight. In many small practices, that's where the model breaks.
A strong Privacy Officer can still struggle with patching, access reviews, logging, disaster recovery, and vendor-side security controls.
That's why many practices split the work. An internal leader owns the privacy side because they understand patient workflows and staff behavior. A technical partner supports or fills the security side because ePHI protection requires tools, monitoring, and operational discipline that most front-office teams don't have.
If your practice is also juggling multiple regulatory frameworks, it helps to think in terms of mapped controls rather than isolated checklists. This guide on compliance mapping for businesses is useful because it shows how overlapping obligations can be organized without duplicating effort.
Where practices get confused
The usual confusion points look like this:
- They assume privacy equals security: It doesn't. A clean notice of privacy practices won't stop unauthorized remote access.
- They assign the role by title, not capability: The most senior admin isn't always the right person for security oversight.
- They ignore overlap: These roles are distinct, but they still have to work together when a breach, complaint, or vendor issue crosses both domains.
A practice that treats both roles as one vague compliance bucket usually ends up weak in both.
Core Responsibilities and Daily Tasks of Your HIPAA Officer
Monday starts with a staff member asking to text a patient from a personal phone, a terminated employee still showing as active in a cloud app, and a vendor questionnaire sitting unanswered in someone’s inbox. That is what HIPAA oversight looks like in a real practice. It is not a yearly policy exercise. It is daily operational control over how PHI is handled, where the practice is exposed, and who is responsible for fixing it.

A good HIPAA Officer keeps the practice out of avoidable trouble by turning broad regulatory requirements into repeatable habits. In a small Florida practice, that usually means one internal owner handles policy, workforce behavior, and patient-facing privacy issues, while a managed IT or SOC partner carries much of the technical security workload. That split works well if ownership is clear.
Administrative safeguards in real life
The administrative side is where many problems start. Staff take shortcuts. Old procedures linger. Vendors get access without much scrutiny. The HIPAA Officer has to stop that drift before it becomes normal.
Typical responsibilities include:
- Policy ownership: Maintain and update policies for access, sanctions, remote work, mobile devices, records retention, and incident response.
- Workforce training: Make sure new hires get trained, annual refreshers are completed, and problem areas are addressed after mistakes or close calls.
- Vendor oversight: Track Business Associate Agreements, review vendor access, and challenge whether a vendor needs PHI at all.
- Incident intake: Give staff a simple reporting path for suspicious emails, misdirected records, unauthorized access, and verbal or written disclosures.
- Workflow review: Approve, deny, or redesign office processes that create unnecessary exposure.
This work requires judgment. If the front desk wants to use a consumer messaging app because patients respond faster, the answer cannot be based on convenience alone. Someone has to weigh speed against disclosure risk, documentation requirements, and whether there is an approved alternative.
Security tasks usually sit with a technical lead or outside partner
Security oversight is more than buying antivirus and checking a box on a risk assessment. It requires follow-through. Systems have to be configured correctly, monitored, updated, and reviewed on a schedule the practice can maintain.
For many small practices, the Security Officer function is shared. An internal leader remains accountable, but the technical work is often handled by a managed IT provider or SOC partner that can execute it. That arrangement is practical because the tasks are specialized and recurring:
- Access reviews: Verify who can access the EHR, billing platform, email, cloud storage, imaging systems, and remote support tools.
- MFA enforcement: Require multi-factor authentication for email, remote access, cloud applications, and privileged accounts.
- Patch and vulnerability management: Apply updates on schedule, track exceptions, and document systems that cannot be patched immediately.
- Audit log review: Look for unusual login activity, after-hours access, repeated failures, privilege changes, and excessive chart access.
- Encryption and secure transmission: Confirm protections for endpoints, backups, email, file transfers, and any workflow that moves ePHI outside the core system.
- Remediation tracking: Assign fixes, set deadlines, and verify that open security issues do not sit unresolved for months.
The trade-off is simple. Outsourcing the technical side gives a small practice access to tools, monitoring, and security staff it would not hire in-house. It does not transfer responsibility away from the practice owner. Someone internal still has to review reports, approve priorities, and make sure the vendor is doing the work promised.
The risk assessment matters because it sets the remediation agenda. If it identifies weak remote access, unmanaged devices, or broad user permissions, those issues need owners, deadlines, and follow-up.
Physical safeguards still create real exposure
Cybersecurity gets more attention, but physical controls still cause privacy failures in medical offices.
A HIPAA Officer should routinely check:
- Workstation placement: Front-desk screens, exam room laptops, and shared work areas should not expose PHI to patients or visitors.
- Device handling: Laptops, tablets, phones, and removable media need inventory control, secure storage, and clear rules for transport.
- Office access: Server closets, records storage, and back-office areas should not be open to anyone who wanders past reception.
- Paper disposal: Printed schedules, labels, intake forms, and old media need secure destruction procedures.
- Fax workflows: Staff need a standard process for confirming numbers, handling misdirected transmissions, and using a proper HIPAA compliant fax cover sheet.
Paper still creates incidents. So do unsecured screens and unattended devices.
What this role looks like on a real schedule
The work has a cadence. If no one owns that cadence, small issues pile up until they become findings, complaints, or reportable incidents.
| Cadence | Typical HIPAA Officer tasks |
|---|---|
| Daily | Answer staff questions, triage incidents, approve or reject risky workflow requests, coordinate with IT on urgent security issues |
| Weekly | Review onboarding and offboarding access changes, check open remediation items, follow up on vendor questions, confirm reported issues were closed |
| Monthly | Review logs and access reports, confirm backup and patch status with the technical partner, update the risk register, review policy exceptions |
| Quarterly | Test selected controls, review workforce training gaps, assess vendor risk items, and confirm business associate documentation is current |
| Annually | Run formal training, perform or coordinate the risk assessment, refresh policies, test response procedures, and report status to practice leadership |
A practice does not need a full-time executive to do all of this. It does need clear authority, scheduled time, documented decisions, and technical support that is competent enough to handle the security side properly.
Building Your HIPAA Officer Profile A Job Description Template
Most small practices don't need a polished corporate posting. They need a usable internal document that defines who owns the work and what success looks like. If you skip that step, the role becomes vague fast.
The hiring market also explains why many practices hesitate to build this in-house. According to Accountable's 2026 salary overview for HIPAA Compliance Officers, projected pay averages $41–$70 per hour, with mid-career professionals earning $105,000–$130,000 annually.

What to look for in the right person
A strong HIPAA Officer for a medical practice usually has a mixed skill set. Pure compliance knowledge isn't enough. Pure IT knowledge isn't enough either.
Look for someone who can handle:
- Healthcare workflow judgment: They understand front desk, billing, referrals, records handling, and vendor coordination.
- Policy discipline: They can write, update, and enforce procedures without turning every task into bureaucracy.
- Incident judgment: They can separate a minor operational mistake from a reportable event that needs escalation.
- Communication under pressure: They can train staff, challenge bad habits, and document decisions clearly.
For many practices, the best internal candidate is an operations-minded administrator with enough authority to enforce policy. If the same person lacks technical depth, that's not disqualifying. It just means the security function may need outside support.
Sample HIPAA Officer job description
Use this as a starting point and tailor it to your practice.
Position title: HIPAA Officer
Reports to: Practice Owner, Managing Partner, or Executive Administrator
Role summary: Own the practice's HIPAA privacy and security program, including policy management, workforce training, incident coordination, vendor oversight, and compliance documentation.
Key responsibilities
- Policy management: Maintain and update HIPAA-related policies, procedures, notices, and documentation.
- Training oversight: Coordinate onboarding and annual HIPAA training for all workforce members.
- Risk coordination: Lead or coordinate periodic risk assessments and track remediation items.
- Incident response: Receive reports of suspected privacy or security incidents, document findings, and escalate as needed.
- Vendor management: Review Business Associate relationships and maintain agreement records.
- Audit readiness: Organize evidence, logs, training records, and policy acknowledgments for internal review or regulatory inquiry.
Required capabilities
- Experience in medical practice operations, healthcare administration, compliance, or information security.
- Working knowledge of the HIPAA Privacy Rule, Security Rule, and breach response obligations.
- Ability to manage confidential information with discretion.
- Strong writing, training, and documentation skills.
Preferred setup for small practices
- Internal ownership of privacy workflows and staff accountability.
- External technical support for ePHI safeguards, monitoring, and remediation.
What to avoid in the job description
A weak posting usually fails in one of three ways:
- It's too broad: It says "ensure HIPAA compliance" but doesn't define duties.
- It's too technical: It reads like a security engineer role and ignores patient-facing privacy responsibilities.
- It's too junior: It assigns major accountability to someone with no authority to enforce anything.
The better approach is clarity. Define the role, the reporting line, and the boundary between internal duties and outside technical support.
The HIPAA Officer's Critical Role During a Data Breach
A breach rarely starts with certainty. It starts with confusion.
A staff member notices unusual email activity. A billing user can't access files. A laptop goes missing. A vendor reports suspicious access. In those first hours, the practice doesn't need panic. It needs a person who knows what to do next.
The first moves after discovery
The HIPAA Officer acts like the incident coordinator. Not because they perform every technical step personally, but because they make sure the practice responds in a controlled order.
That usually means:
- Confirming the event: Is this an actual incident, a suspected breach, or a false alarm?
- Containing exposure: Disable accounts, isolate devices, revoke access, and preserve evidence.
- Starting documentation immediately: Who found it, when, what systems were involved, and what actions were taken.
The biggest mistake small practices make is informal response. Someone reboots a machine, deletes an email, or calls a vendor before basic facts are documented. That makes investigation harder and can damage the record you may later need.
In a breach, undocumented action is almost as dangerous as delayed action.
The notification clock matters
Once a breach is confirmed, the HIPAA Officer has to drive the legal and operational response together. That includes deciding who needs to be informed internally, what outside specialists need to be engaged, and whether patient notification obligations are triggered.
Under the verified guidance on HIPAA officer duties, breach investigations include notification requirements that must be met within 60 days when applicable. That deadline sounds generous until you realize the work involved. The practice has to identify affected data, determine scope, gather facts, prepare notices, and keep a defensible record of how conclusions were reached.
A prepared office can move through that process. An unprepared office loses time arguing about basic ownership.
What a competent response looks like
A capable HIPAA Officer should already have these pieces lined up before a breach happens:
| Response element | Why it matters |
|---|---|
| Incident response plan | Staff know who to call and what not to do |
| Contact list | Legal, IT, vendors, and leadership can be activated fast |
| Evidence process | Logs, screenshots, and device details are preserved |
| Decision record | The practice can explain why it classified the event the way it did |
| Patient communication workflow | Notices can be drafted and approved without chaos |
If your practice doesn't already have those basics written down, this guide to crafting your incident response plan for max efficiency is a practical place to start.
The officer's job after the immediate crisis
The work doesn't end when systems are restored.
The HIPAA Officer should also lead the post-incident review. That means identifying the root cause, updating policies, retraining staff if needed, and making sure the same weakness doesn't stay in place. If a stolen device exposed a gap in encryption policy, the answer isn't just replacing the laptop. It's fixing the control failure behind it.
In a strong practice, the breach response creates better discipline afterward. In a weak one, everyone moves on as soon as operations resume.
Smart Compliance for Small Practices in Orlando and Winter Springs
Small practices in Central Florida usually don't have the budget or workload to justify a full-time privacy professional plus a full-time security leader. But they still face the same HIPAA obligations and many of the same attack paths as larger organizations.
That's why the smartest setup for many local practices is a hybrid model. Keep policy and patient-facing accountability inside the practice. Push technical security execution to a qualified outside partner.

Why internal-only often breaks down
A small office manager can absolutely own privacy operations. They usually understand intake, scheduling, records requests, disclosures, and staff behavior better than anyone external ever will.
What they usually can't do alone is sustain technical enforcement across every endpoint, cloud app, backup process, login path, and vendor connection.
The practical problem is maintenance. Systems need patching, logs need review, remote access needs control, and incident activity needs fast response. Those are ongoing operational duties, not occasional checklists.
According to the verified data from Indeed's HIPAA Privacy Officer job description resource, 70% of breaches at small entities are due to unpatched systems. That is exactly the kind of issue a policy-minded internal officer can't reliably solve without technical support.
The hybrid model that works
For many practices, the cleanest division of labor looks like this:
Internal Privacy Officer
- Manages policies, notices, staff accountability, and patient-facing privacy issues
- Owns training coordination and workflow discipline
- Approves vendors from an operational standpoint
External Security support
- Handles technical safeguards for ePHI
- Manages patching, monitoring, access security, endpoint protection, and response support
- Documents technical controls and remediation work
This model lines up with HIPAA's allowance for business associates to support security functions. It also reflects how small practices operate. The people closest to patients handle privacy decisions. The people with tools and technical depth handle security operations.
The right outsourced security partner doesn't replace your internal owner. They make that owner effective.
What to expect from a capable outside partner
An outside technical partner should do more than fix printers and reset passwords. For HIPAA support, you want a partner that can support disciplined security operations.
Ask practical questions:
- Do they manage patching on a defined schedule
- Can they support logging, endpoint protection, and incident response
- Will they document assets, systems, and remediation steps
- Do they understand Business Associate obligations
- Can they support a small practice without forcing enterprise complexity
If you're comparing local options, this roundup of cyber security companies in Orlando is a useful starting point because it frames the market through service depth, not just generic MSP language.
A workable structure for a Central Florida practice
A dentist in Winter Springs, a veterinary group in Orlando, and a plastic surgery office in Central Florida may all land on slightly different staffing models. But the structure that tends to work is consistent:
| Function | Best owner for many small practices |
|---|---|
| Patient privacy questions | Internal administrator or compliance lead |
| Policy enforcement | Internal leadership |
| Risk assessment coordination | Shared between internal lead and external technical support |
| Patch management and monitoring | External security partner |
| Incident escalation | Shared, with technical response support outside the practice |
What doesn't work is pretending one overwhelmed employee can do both jobs at a high level without help. Small practices stay compliant when they divide responsibility realistically.
Turn HIPAA Compliance into a Competitive Advantage
A HIPAA Officer is a control point for the whole practice. The role keeps privacy decisions from becoming guesswork and keeps security obligations from getting ignored until something breaks.
For small medical businesses in Orlando and Winter Springs, the practical answer usually isn't building a large internal compliance department. It's choosing clear ownership. One person inside the practice should own the privacy program and day-to-day accountability. Technical security should be handled with the depth and consistency that ePHI protection demands.
Patients may never ask who your HIPAA Officer is. They will notice the outcome. They notice when records are handled professionally, when communication feels controlled, and when your office runs like patient data matters.
That trust has business value. A practice that protects information well looks organized, credible, and safe to work with. In a competitive local market, that's not just compliance. It's reputation.
If your practice in Orlando, Winter Springs, or North Texas needs help building a realistic HIPAA security program around your existing operations, Cyber Command, LLC can support the technical side with managed IT, 24/7 SOC coverage, incident response, patching, and compliance-focused security operations that fit small and midsize organizations.