Protecting Your Digital Realm: Understanding Network Security

Why Understanding Network Security Is Essential for Every Business
Information about network security is critical for any organization that relies on digital systems to operate. At its core, network security encompasses the tools, policies, and practices designed to protect your computer networks and the sensitive data they carry from unauthorized access, cyberattacks, and disruption.
What you need to know about network security:
- Definition: Network security is the practice of protecting computer networks and their data from threats, misuse, and unauthorized access
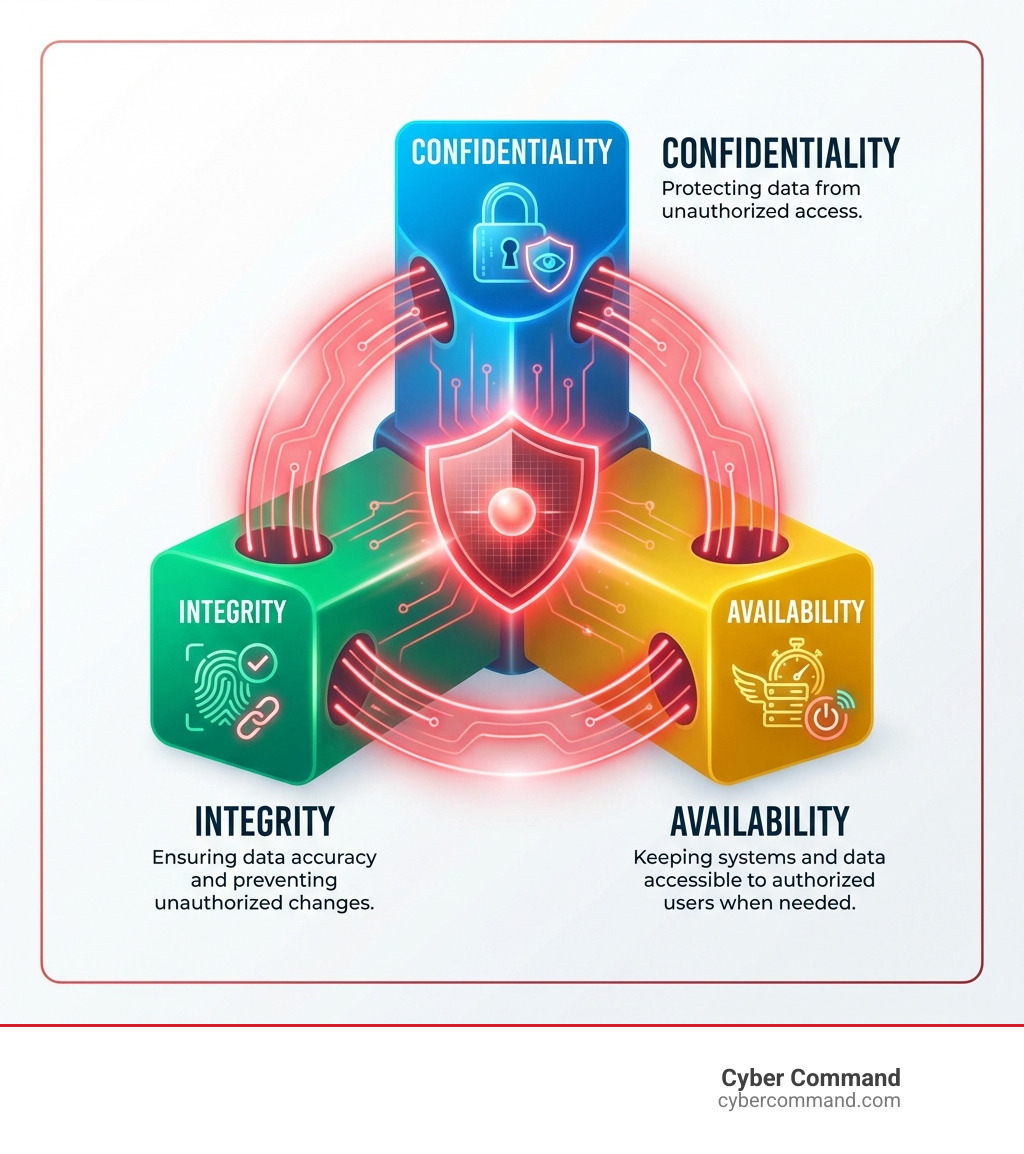
- Core Principles: Built on three pillars—Confidentiality (keeping data private), Integrity (ensuring data remains accurate), and Availability (keeping systems accessible when needed)
- Why It Matters: The global average cost of a data breach reached USD 4.44 million in 2024, making protection essential for business survival
- Who Needs It: Every organization—from small businesses to large enterprises—faces increasing cyber threats and must implement security measures
- Key Components: Includes firewalls, encryption, access controls, intrusion detection systems, and security policies working together in layers
The reality is stark. Cyber attacks against organizations have greatly increased over the past few years and show no signs of slowing down. Whether you’re protecting customer information, intellectual property, or simply keeping your operations running smoothly, network security is no longer optional—it’s fundamental to business continuity.
I’m Reade Taylor, Founder and CEO of Cyber Command, and I’ve spent my career helping businesses steer the complexities of enterprise-grade cybersecurity and infrastructure, starting with my work as an engineer at IBM Internet Security Systems. My mission is to make information about network security accessible and actionable, changing it from a source of stress into a competitive advantage for growing businesses.
What is Network Security and Why Is It Crucial?
In today’s interconnected world, computer networks underpin everything from mobile workforces to global financial systems. These systems continuously share data, but this constant flow of information about network security also presents a vast attack surface for malicious actors.
At Cyber Command, we define network security as the set of solutions, tools, and best practices that protect the integrity, confidentiality, and availability of computer networks and the data they store. It safeguards these vital connections from unauthorized access and cyberattacks. As the National Institute of Standards and Technology (NIST) highlights, securing IT products is vital for an organization’s success. You can learn more from An Introduction to Information Security.
Why is this so crucial? The impact of poor network security can be devastating. The global average cost of a data breach was USD 4.44 million last year, a figure representing lost revenue, reputational damage, and legal fees. For businesses in Florida and Texas, where digital economies are booming, robust network security is a survival strategy.

The Core Benefits of Robust Network Security
Implementing robust network security brings benefits that extend far beyond simply avoiding a breach. It’s about creating a resilient, trustworthy, and efficient digital environment for our clients.
- Protecting Sensitive Data: Network security safeguards all forms of data, from customer records and financial information to intellectual property. Protecting what is pii in cybersecurity (Personally Identifiable Information) is not just good practice; it’s often a legal requirement.
- Preventing Financial Loss: A data breach can lead to massive financial consequences, like the USD 4.44 million average cost. Robust security prevents these losses by averting ransomware payments, fines, and business disruption.
- Preserving Brand Reputation: A security incident can severely damage a company’s reputation and lead to lost customers. Strong security demonstrates a commitment to protecting client and customer data.
- Ensuring Operational Stability: Cyberattacks can bring operations to a halt, causing costly downtime. Network security ensures business continuity and keeps client systems running smoothly.
- Achieving Regulatory Compliance: Many industries are subject to strict regulations (e.g., HIPAA, PCI DSS). Robust network security helps organizations meet these requirements and avoid hefty fines. For more on this, check out our guide to master cybersecurity compliance for it managed services.
The Main Types of Cyber Threats Targeting Networks
To effectively protect networks, we must understand the adversaries. Cyber criminals use increasingly sophisticated methods, including AI-powered tools, to infiltrate secure networks. Here are some of the main types of cyber threats:
- Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks: These attacks flood a network or server with traffic, making it unavailable to legitimate users. Imagine a thousand people trying to enter a single door at once – nothing gets in or out.
- Man-in-the-Middle (MITM) Attacks: Attackers secretly intercept communications between two parties. This allows them to eavesdrop, steal data, or alter the communication. It’s like someone secretly listening in on your phone call.
- Malware (Malicious Software): This broad category includes viruses, worms, and Trojans. Malware can damage systems, steal data, or create backdoors for further attacks. A particularly nasty form is ransomware attack, which encrypts data and demands payment.
- Phishing and Social Engineering: These attacks trick users into revealing sensitive information (like passwords) or downloading malware. Email gateways are the number one threat vector for a security breach. Spear phishing targets specific individuals with highly customized attacks.
- Insider Threats: These come from within an organization, either intentionally (malicious employees) or unintentionally (negligent employees). Accidental actions can compromise network security. Learn more about proactive insider threat detection top tools practices.
- Advanced Persistent Threats (APTs): These are stealthy, prolonged cyber-attacks where an unauthorized user gains network access and remains undetected for an extended period to steal sensitive data.
- Zero-Day Exploits: These target previously unknown network vulnerabilities for which no patch exists. They are incredibly dangerous because there’s no immediate defense.
- Brute Force Attacks: Attackers use trial and error to guess passwords or other login credentials, attempting many combinations until they find the correct one.
Comprehensive Information About Network Security Layers and Controls
Effective network security is a layered defense strategy, often called “defense-in-depth.” Instead of a single barrier, a series of controls work together to protect digital assets. Each layer adds an obstacle for attackers, making it harder to reach valuable data. This multi-layered approach is fundamental to securing any network, as highlighted in network security fundamentals.
The Fundamental Layers of Security
Network security encompasses three fundamental layers, each addressing different aspects of protection:
-
Physical Network Security: This layer protects the physical infrastructure of your network, like the locks on your doors.
- Controls: Access cards, biometrics, CCTV surveillance, locked server rooms, and secure cabling.
- Purpose: To prevent unauthorized individuals from gaining physical access to network devices (routers, servers, switches). We strictly enforce these measures at our data centers and client sites in Florida and Texas.
-
Technical Network Security: This layer involves software and hardware controls that protect data in motion and at rest. These are the digital guardians of your network.
- Controls: Firewalls, encryption, antivirus/anti-malware software, intrusion detection and prevention systems (IDS/IPS), network access control (NAC), and secure configurations.
- Purpose: To block unauthorized access, prevent malicious activities, and protect sensitive data. For instance, effective data encryption best practices for data protection are crucial here.
-
Administrative Network Security: This layer focuses on the policies, procedures, and human elements that govern network usage and security.
- Controls: Security awareness training, access management policies, incident response plans, and regular security audits.
- Purpose: To define and manage authentication (verifying identity), authorization (granting permissions), and user roles, ensuring proper configuration and monitoring. We emphasize this through initiatives like boost human security with cybersecurity awareness training.
Essential Network Security Technologies
Within these layers, several essential technologies create a formidable defense:
- Firewalls: A firewall is a network security device that monitors incoming and outgoing traffic, allowing or blocking it based on a defined set of security rules. They act as a barrier between trusted internal networks and untrusted external networks. Next-Generation Firewalls (NGFWs) add intrusion prevention, antivirus, and web filtering for more robust protection. We are always working on strengthening security with next gen firewalls.
- Intrusion Prevention Systems (IPS): An IPS detects and blocks known and suspected threats before they impact the network. Unlike an Intrusion Detection System (IDS) which only alerts, an IPS actively prevents attacks by dropping malicious packets or blocking IP addresses. They offer deep packet inspection and can provide virtual patching for vulnerabilities.
- Antivirus and Anti-Malware Software: These tools protect endpoints (computers, servers) by scanning for, detecting, and removing malicious software. They use signature-based and behavioral analysis to identify threats. Sandboxing is often used to safely isolate and analyze suspicious files before they can harm the network.
- Virtual Private Networks (VPNs): VPNs create a secure, encrypted connection over a less secure network, like the internet. They are essential for data privacy and secure remote access, especially in today’s hybrid work environments. We often recommend and implement strategies for securing remote workforces with vpn mfa for our clients.
The Role of Access Control and Network Segmentation
Access control and network segmentation are two critical concepts that limit the potential impact of a breach.
-
Access Control: This ensures that only authorized users, devices, and applications can access specific network resources. The core principle is “least privilege,” meaning users are granted only the minimum access necessary to perform their jobs.
- Network Access Control (NAC): NAC solutions identify and authenticate devices and users attempting to connect, then enforce security policies. Non-compliant devices (e.g., outdated antivirus) can be quarantined or denied access.
- Role-Based Access Control (RBAC): This assigns permissions based on a user’s role within the organization, simplifying management.
- Multi-Factor Authentication (MFA): This adds an extra layer of security by requiring two or more verification factors to gain access, making it much harder for unauthorized individuals to log in.
-
Network Segmentation: This involves dividing a network into smaller, isolated segments. This creates barriers, preventing a breach in one area from spreading everywhere.
- Purpose: To limit the lateral movement of threats. If an attacker breaches one segment (e.g., guest Wi-Fi), they cannot easily move to a more sensitive one (e.g., the financial server network).
- Benefits: Isolates critical assets, improves performance, and makes it easier to contain security incidents. This is particularly important for protecting iot and network security devices.
Building Your Fortress: Strategic Network Security Management
Managing network security effectively is an ongoing journey, not a destination. It requires a strategic mindset that shifts from merely reactive responses to proactive defense. We help our clients build fortresses, not just patch holes.
One of the first steps is understanding your current posture, which involves conducting a thorough how to conduct a cyber security risk assessment. This helps identify vulnerabilities and prioritize protective measures. Equally important is having a robust crafting your incident response plan for max efficiency. Even with the best defenses, incidents can happen, and a clear plan minimizes damage and accelerates recovery.
However, organizations face significant challenges in managing network security effectively. The evolving threat landscape means cybercriminals are constantly finding new ways to attack. The increasing sophistication of methods, often powered by AI, makes detection and prevention harder. Furthermore, a persistent skills gap in cybersecurity means many businesses struggle to find and retain the talent needed to manage complex security infrastructures. This is where partnering with a managed security service provider like Cyber Command, with our U.S.-based 24/7/365 support teams in Florida and Texas, becomes invaluable.
The Zero Trust Revolution
One of the most transformative trends in network security is the adoption of Zero Trust architecture. This concept fundamentally changes how we approach security, moving away from the traditional “trust but verify” model to a “never trust, always verify” approach.
Zero Trust assumes that no user or device, whether inside or outside the network, should be implicitly trusted. Every access request must be rigorously authenticated, authorized, and continuously validated. This is a significant departure from older perimeter-based security models, where everything inside the network was considered safe. Our guide on the importance of zero trust architecture for modern security dives deeper into this.
Key tenets of Zero Trust include:
- Verify Explicitly: Authenticate and authorize every access request based on all available data points, including user identity, device health, location, and risk.
- Least Privilege Access: Grant users and devices only the minimum access required for their task, and for the shortest possible duration.
- Assume Breach: Design security with the assumption that a breach is inevitable, focusing on minimizing its blast radius and enabling rapid detection and response.
- Micro-segmentation: Isolate workloads and resources into small, secure zones, applying granular security policies to each. This prevents attackers from moving freely across the network even if they gain initial access.
Here’s a quick comparison:
| Feature | Traditional Perimeter Security | Zero Trust Architecture |
|---|---|---|
| Default Assumption | Trust inside, distrust outside | Never trust, always verify |
| Access Control | Once inside, broad access often granted | Strict, explicit verification for every access request |
| Focus | Protecting the network perimeter | Protecting data and resources, regardless of location |
| Lateral Movement | Easier for attackers once inside | Restricted via micro-segmentation and continuous verification |
| User/Device Trust | Implicit trust for internal users/devices | Explicit, continuous trust assessment for all users/devices |
The Importance of Proper Network Configuration
Network configuration is the bedrock of network security. It’s about establishing policies, assigning network settings, and controlling traffic flows to support operations, improve security, and increase stability. Without proper configuration, even the most advanced security tools can leave glaring vulnerabilities.
We’ve seen countless times how seemingly small configuration oversights can lead to major security incidents. One common pitfall is relying on default settings, especially default passwords. Many countries are even instituting bans on easy-to-guess default passwords due to the frequency with which devices can be exploited. Failing to properly configure devices can lead to many holes in your network’s security. The Benefits of Proper Network Configuration are clear: it limits which computers and devices can connect, sets connection requirements, and controls how devices communicate.
Key aspects of secure network configuration include:
- Avoiding Default Passwords: Always change default credentials on all network devices (routers, switches, firewalls, IoT devices).
- Patch Management: Regularly updating and patching all operating systems, applications, and network device firmware is crucial. Unpatched vulnerabilities are a prime target for attackers.
- Vulnerability Scanning: Regularly scanning your network for known vulnerabilities helps identify weaknesses before attackers can exploit them. This proactive approach is detailed in our guide on proactive vulnerability assessment for threat management.
- Principle of Least Functionality: Disable unnecessary services, ports, and protocols on network devices to reduce the attack surface.
- Secure Baseline Configurations: Establish and maintain standardized, secure configurations for all network devices and systems.
How to Choose the Right Network Security Solutions
Choosing the right network security solutions can feel like navigating a maze. With countless vendors and technologies available, it’s easy to get overwhelmed. Here’s our approach to helping clients make informed decisions:
- Assessing Your Needs and Risks: Every business is unique. We start by understanding your specific business objectives, the sensitive data you handle, your regulatory obligations, and your existing infrastructure. This helps us identify your biggest risks and where security investments will have the most impact.
- Evaluating Vendors: We look beyond flashy marketing. We assess vendors based on their track record, product features, integration capabilities, and customer support. The usability and manageability of a solution are just as important as its technical prowess.
- Scalability and Integration: Your business will grow, and your security solutions should grow with you. We prioritize solutions that are scalable and can seamlessly integrate with your existing (and future) IT environment, avoiding fragmented security tools that create management headaches.
- Considering Cloud vs. On-Premise: The shift to cloud computing is undeniable. Organizations face additional challenges in maintaining tight security controls as cloud-based networks become increasingly mainstream. Whether you need on-premise hardware, cloud-native security, or a hybrid model, we help you weigh the pros and cons. Cloud networking offers significant benefits in flexibility and scalability, which we explore in what are the benefits of cloud networking.
- Managed Security Services: For many businesses, especially small to medium-sized enterprises, managing complex network security in-house is a significant challenge. This is where managed security services providers (MSSPs) like Cyber Command come in. We offer expert 24/7 monitoring, threat detection, incident response, and compliance management, acting as an extension of your team. You can explore benefits of cybersecurity in managed services to see how we can help.
The Future of Network Security: Trends and Best Practices
The landscape of network security is constantly evolving, driven by new technologies and increasingly sophisticated cyber threats. Staying ahead requires understanding emerging trends and adopting best practices.
AI and Machine Learning in Threat Detection
Cyber criminals are adopting increasingly sophisticated methods, including AI-powered tools, to infiltrate secure networks. Thankfully, AI and Machine Learning (ML) are also powerful allies in defense. These technologies are revolutionizing threat detection by:
- Identifying Anomalies: AI/ML algorithms can analyze vast amounts of network traffic and user behavior data to detect patterns that deviate from the norm, indicating a potential threat that human analysts might miss.
- Automating Response: AI can automate initial responses to threats, such as isolating compromised devices or blocking malicious traffic, reducing response times from hours to minutes or even seconds.
- Predictive Analytics: By learning from past attacks, AI can predict potential future threats and proactively strengthen defenses. Our insights on understanding the role of ai and ml in threat detection dig deeper into this.
Cloud Security Challenges and Solutions
Cloud computing offers immense flexibility and scalability, but it also introduces new security challenges. Organizations face additional complexities in maintaining tight security controls as cloud-based networks become increasingly mainstream. Challenges include reduced visibility and control, misconfigurations in cloud settings, the use of Shadow IT (unauthorized applications), insecure APIs, and risks associated with external data sharing.
To address these, solutions like:
- Cloud Access Security Brokers (CASBs): Act as gatekeepers, enforcing security policies for cloud-based resources.
- Cloud Workload Protection Platforms (CWPPs): Secure workloads across hybrid and multi-cloud environments.
- Secure Access Service Edge (SASE): This is a modern, cloud-native approach that converges networking and security functions into a single, unified cloud service. It combines Wide Area Network (WAN) capabilities with comprehensive security services like secure web gateways, CASBs, and Zero Trust Network Access (ZTNA). SASE is particularly well-suited for securing distributed workforces and cloud-centric operations.
- Extended Detection and Response (XDR): XDR is an emerging approach that unifies and correlates security data across multiple layers—endpoints, networks, cloud workloads, and email—to provide a more comprehensive view of threats and enable faster, more effective detection and response. This is a step beyond traditional Endpoint Detection and Response (EDR). Learn more in understanding edr xdr for enhanced smb cyber defense.
We also guide clients on secure cloud migrations, as outlined in how to successfully migrate applications from on premises to cloud.
Frequently Asked Questions about Network Security
We often encounter similar questions from businesses looking to bolster their defenses. Here are some of the most common inquiries about information about network security.
What is the difference between network security and cybersecurity?
While often used interchangeably, there’s a key distinction. Cybersecurity is the broader practice of protecting all digital assets, including systems, networks, programs, and data, from digital attacks. It encompasses everything from application security to cloud security to data privacy. Network security, on the other hand, is a specific subset of cybersecurity. It focuses explicitly on protecting the integrity, confidentiality, and availability of computer networks and the data traversing them. So, all network security is cybersecurity, but not all cybersecurity is network security. Think of cybersecurity as the entire castle, and network security as the defenses around the castle’s perimeter and internal pathways.
Can network security stop 100% of attacks?
In an ideal world, yes, but in reality, no security measure can guarantee 100% protection against all possible attacks. The threat landscape is constantly evolving, and determined attackers will always look for new vulnerabilities. A layered, defense-in-depth strategy, combined with a Zero Trust approach, aims not to promise absolute prevention but to make attacks incredibly difficult, detect them quickly when they occur, and minimize their impact. Our goal at Cyber Command is to build resilient systems that can withstand and rapidly recover from incidents, rather than chasing an impossible promise of complete invulnerability.
What is the most common entry point for network attacks?
Sadly, the most common entry point for network attacks is often the easiest to exploit: human error, typically through email. Email gateways are the number one threat vector for a security breach. Phishing attacks, which are scams delivered via email (or other messaging platforms) designed to trick users into revealing sensitive information or clicking malicious links, are incredibly prevalent and effective. Even with advanced technical controls, a single click on a malicious link can bypass defenses and grant attackers initial access to a network. This underscores the critical importance of continuous security awareness training for all employees.
Conclusion
Understanding information about network security is no longer a niche concern; it’s a fundamental requirement for any organization operating in today’s digital world. We’ve explored its definition, the critical reasons for its importance, the types of threats we face, and the layered defenses—from physical to administrative—that protect our digital assets. We’ve also digd into strategic approaches like Zero Trust and the crucial role of proper network configuration.
The digital field is dynamic, and so too must be our approach to security. The rise of cloud computing and emerging technologies like AI presents both challenges and opportunities, pushing us toward innovative solutions like SASE and XDR. For businesses in Florida, Texas, and beyond, a proactive, layered, and strategic approach to network security is not just a defense mechanism; it’s a competitive advantage that protects your data, preserves your reputation, and ensures your operational continuity.
At Cyber Command, we are committed to providing the expert guidance and comprehensive managed security services needed to steer this complex landscape. We act as an extension of your business, offering proactive, 24/7/365 U.S.-based support with transparent, all-inclusive pricing. Don’t leave your digital field vulnerable. Take the next step in securing your digital field with our comprehensive cybersecurity services.

