Incident Response Playbooks for Orlando, Tampa, and Central Florida Businesses
An incident response playbook is a detailed, step-by-step guide that dictates the specific actions to take during a security incident. Unlike a general plan, a playbook provides a precise, repeatable workflow for a particular threat, such as ransomware, ensuring your team can act quickly and decisively to minimize damage.
Beyond the Plan: Why Actionable Playbooks Are Your Real Defense
When a cyber incident strikes, having a generic response plan is like carrying a map of Florida to navigate a specific backstreet in downtown Orlando. It’s a good starting point, but it's utterly useless when you’re under pressure and need to make a fast, correct turn.
Central Florida businesses, from manufacturing companies in Tampa to legal and financial firms in Orlando, need more than a dusty, high-level document. You need dynamic, actionable incident response playbooks.
Imagine a ransomware attack hits your network on a busy Tuesday morning. Alarms are blaring, and chaos erupts. Without a clear playbook, your team scrambles. Decisions are delayed, critical mistakes are made, and every second costs you. For businesses in key Florida industries like hospitality, healthcare, or construction, this is where catastrophic financial and reputational damage happens.
From Vague Ideas to Concrete Actions
A well-crafted playbook transforms that chaos into a controlled, manageable process. It’s the bridge from theoretical ideas to a concrete sequence of operations. A generic plan might say, "Isolate affected systems." That’s not helpful in a crisis.
A ransomware playbook, on the other hand, tells you exactly who isolates them (by name and role), how they do it (with specific commands or tools), and what communication needs to happen immediately after.
This shift from a high-level plan to a detailed playbook is fundamental to business continuity. It’s not just an IT concern—it’s about protecting your revenue, client trust, and operational stability against pressing cybersecurity concerns.
To put it plainly, a generic plan and a playbook are two completely different tools. One is for the boardroom, the other is for the trenches.
A Generic Plan vs an Actionable Playbook
| Attribute | Generic Incident Plan | Actionable Incident Response Playbook |
|---|---|---|
| Scope | Broad, high-level strategy for all incidents | Narrow, step-by-step checklist for one specific threat |
| Audience | Leadership, auditors, and management | IT/security team, SOC analysts, on-call engineers |
| Example Action | "Contain the threat and notify stakeholders." | "1. Disconnect network cable from workstation WS-07. 2. Disable user account j.doe in Active Directory. 3. Use the 'Data Breach – Tier 2' email template to notify the Legal team." |
| Goal | To meet compliance and outline general goals | To stop an active attack, minimize damage, and recover quickly |
The difference is stark. One sets a direction, while the other gives you turn-by-turn instructions to get there safely and quickly.
The real value of an incident response playbook is its power to eliminate guesswork during a high-stress event. It provides absolute clarity and direction when time is your most critical asset, ensuring every action taken is deliberate, correct, and effective.
The New Reality of Cyber Threats in Florida
Modern cyberattacks are meticulously designed for maximum disruption. Attackers don't just steal data anymore; they aim to cripple your entire operation and hold your business hostage. For Florida's diverse industries—from tourism in Orlando to shipping and logistics in Tampa—this trend makes having a pre-defined response strategy non-negotiable for any small or mid-sized business in the region.
The latest data paints a grim picture. In incidents analyzed by Palo Alto Networks' Unit 42, a staggering 86% involved significant business disruption, such as operational downtime and lasting reputational harm.
The report also found that attackers often hit businesses on multiple fronts, with 84% of cases involving multi-faceted attacks. This is why having specific playbooks—one for ransomware, one for a business email compromise, another for a data breach—is essential for industries like professional services or healthcare in Central Florida.
You can explore the complete incident response report to understand the evolving threat landscape. By preparing for these complex scenarios, you can turn a potential business-ending event into a survivable, manageable incident.
Crafting Your Core Incident Response Playbooks
When an attack hits, a three-ring binder full of high-level theory is the last thing you need. For small and mid-sized businesses, especially those in co-managed environments, the line between surviving a cyberattack and becoming a statistic is drawn by having specific, actionable incident response playbooks.
This isn't about generic advice. It’s about building practical, step-by-step guides for the threats your business is most likely to face. The whole point is to have a script that answers the only question that matters in a crisis: who does what, and when?
Identifying Your Most Likely Threats
You can’t boil the ocean, and you can’t defend against every threat at once. The first step is to get real about the 3-4 most probable and impactful threats to your specific business. For the professional services firms, medical practices, and industrial companies we work with across Central Florida, the list usually narrows down to a few key cybersecurity concerns.
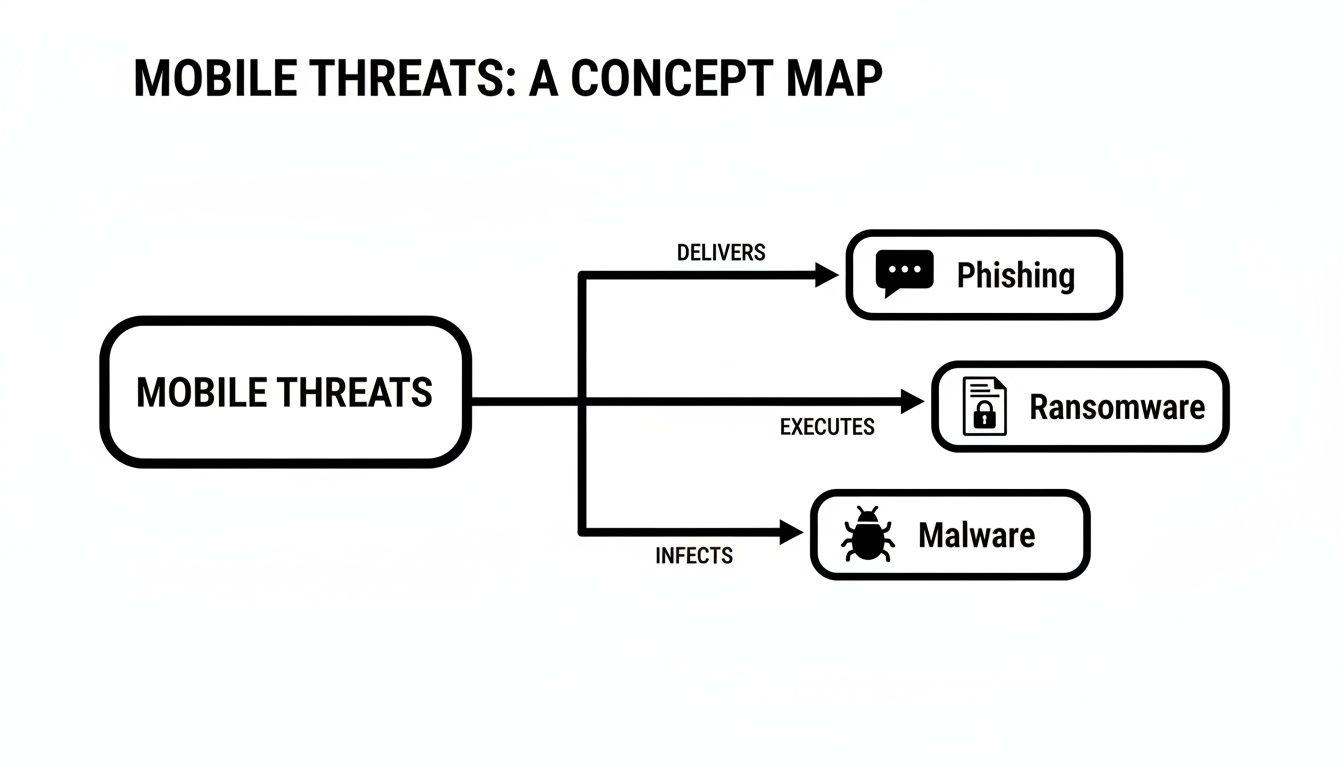
- Phishing & Business Email Compromise (BEC): This is the gateway for many attacks. A single deceptive email can lead to stolen credentials, fraudulent wire transfers, or a full-blown network breach. For any business that relies on email for operations—from construction firms in Tampa to law firms in Orlando—this is a persistent, high-risk threat.
- Ransomware Attack: This is the nightmare scenario for many businesses. Malicious software encrypts your critical files, grinding operations to a halt and putting sensitive data at risk. For industries like healthcare, finance, or legal services, a ransomware attack is not just an IT problem; it's a business-ending event that can trigger regulatory fines and destroy client trust.
- Lost or Stolen Device: A single company laptop or phone goes missing from a job site in Lakeland or an office in Orlando. If it contains sensitive client data, intellectual property, or financial records, you're not just dealing with a lost asset—you're facing a potential data breach and a compliance nightmare.
Once you’ve identified your core threats, you build a dedicated playbook for each one. This focused approach means your team has clear, relevant instructions when they need them most, instead of fumbling through a 100-page "one-size-fits-all" document.
The Anatomy of an Effective Playbook
Each playbook needs to be a concise, no-fluff checklist. Think of it as a recipe that anyone on your team—or your co-managed IT partner—can follow under extreme pressure. It must contain four critical sections that guide the response from detection to recovery.
1. Triggers: What specific event kicks off this playbook?
* Example (Ransomware): An alert from endpoint protection software detects ransomware activity, or an employee reports seeing a ransom note on their screen.
2. Containment: How do we stop the bleeding and prevent this from spreading?
* Example (Ransomware): Immediately disconnect the infected device from the network. With a co-managed partner, a Security Operations Center (SOC) can execute this remotely within seconds of the trigger.
3. Eradication: How do we get the bad stuff out of our environment completely?
* Example (Ransomware): Wipe and re-image the affected machine from a known-good, clean backup. The next step is to find and patch the vulnerability that let the attacker in.
4. Recovery: How do we safely get back to business as usual?
* Example (Ransomware): Restore encrypted data from clean, verified backups. You have to monitor the network for any signs of lingering attacker activity before bringing all systems back online.
Getting the recovery stage right is critical. You can find more on that in our guide on ransomware recovery.
This process is what turns the utter chaos of an attack into a controlled, manageable process.
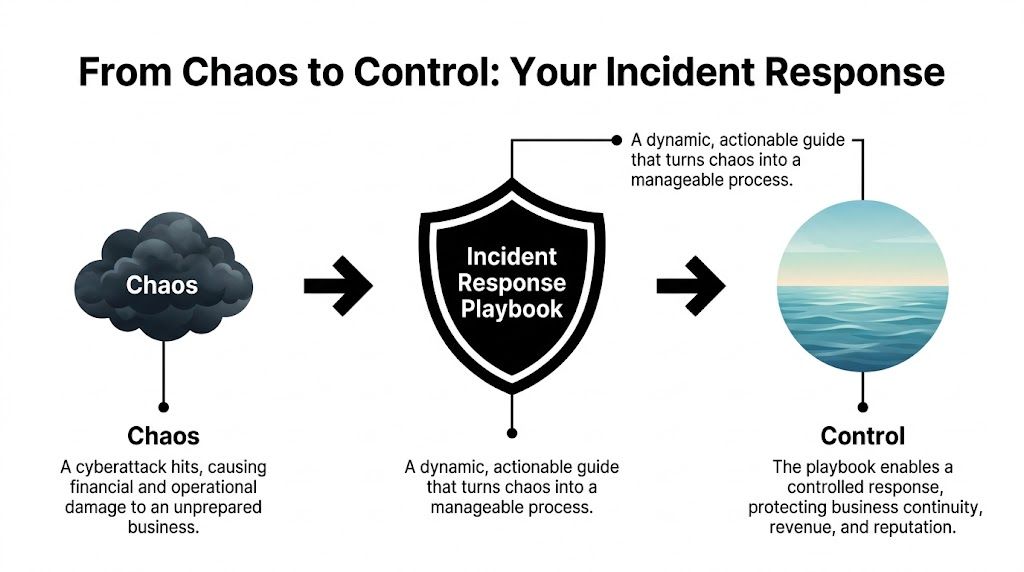
As you can see, the playbook is the tool that lets you move from a state of damaging chaos to one of control, protecting your revenue and reputation along the way.
A great incident response playbook is all about execution. It provides the “who, what, and when” with absolute clarity, ensuring that even in a high-stress situation, your team—and your IT partner—are working from the same script to protect the business.
Bridging the Gap Between Plan and Reality
Here’s a sobering statistic: even though 99% of organizations report having formal incident response plans, a shocking 73% of cybersecurity leaders admit they aren't truly prepared for the next big attack. Why the massive gap? It often comes down to coordination failures, executive disengagement, and other delays that cripple the response.
For SMBs with lean internal teams, this is where things can fall apart. Having a plan on paper is one thing; having the people, processes, and communication lines ready to execute it is something else entirely.
This is exactly where detailed playbooks combined with a strong communications strategy make all the difference. When you build your playbooks, you must integrate your communication steps. It's worth reviewing a modern guide to crisis communications management to ensure your reputation defense is as robust as your technical one. By pre-defining every step, both technical and communicative, you close that dangerous gap between good intentions and effective action.
Defining Roles and Escalation Paths for Your Team

Having a great incident response playbook is one thing. Knowing exactly who does what during an attack is another. The best-written plan will fail if your team descends into chaos because roles aren't crystal clear.
This is where the human element becomes your greatest asset—or your biggest liability.
For small and mid-sized businesses in Orlando, Tampa, and across Central Florida, this gets even trickier. Your people already wear multiple hats. In a crisis, that flexibility can turn into paralysis if they don't have pre-assigned duties. The goal is to make sure nobody ever has to ask, "What now?"
Building Your Response Team Matrix
Your first move should be to build a roles and responsibilities matrix. This isn’t some complicated spreadsheet; it's a simple, at-a-glance chart that maps people to specific actions for every type of incident. For any Central Florida business we work with, this matrix always includes internal staff, key executives, and us—your co-managed security partner.
Here are the core roles we see in every successful response team:
- Incident Commander: This is your field general, the single person directing the response. In a law firm or a construction company, this is often the managing partner or office administrator—someone who can make decisive operational calls, not necessarily your most technical person.
- Technical Lead: This role is almost always handled by your managed IT partner and their 24/7 Security Operations Center (SOC). They are the boots on the ground, handling the hands-on work of isolating systems and kicking the bad guys out.
- Communications Lead: This person manages all messaging, both internally to staff and externally if needed. In a medical practice, this might be the practice manager, who uses pre-approved templates to update the team or communicate with patients about an outage.
- Executive Sponsor: This is the business owner or CEO. They aren't in the technical weeds but are kept in the loop on major developments and are the ones who approve critical business decisions, like authorizing emergency funds for recovery.
This structure lets your technical experts focus on the tech, while business leaders focus on the business. No one steps on anyone else’s toes.
Designing Smart Escalation Paths
Not every blip on the radar needs a 2 AM phone call to the CEO. A smart, logical escalation path protects your leadership’s time and focus, while ensuring genuine emergencies get the executive attention they demand. Your playbooks must define these triggers with absolute precision.
An effective flow matches the incident's severity to the right level of response. It stops people from overreacting to minor issues and, more importantly, guarantees that a major threat doesn't get lost in the noise.
A well-designed escalation path ensures that the right people are notified at the right time, with the right information. It turns a chaotic "fire alarm" situation into a structured, tiered response, preserving leadership focus for when it truly matters.
Let’s look at a CPA firm in Tampa that has a co-managed IT environment. Here’s how a simple escalation flow for a malware alert should work:
- Severity 1 (Minor): A single workstation blocks a low-risk PUP (Potentially Unwanted Program). The SOC logs it, and a report goes to the office manager at the end of the day. No immediate action is needed.
- Severity 2 (Moderate): An employee clicks a phishing link, but our endpoint protection blocks the malicious site before any damage is done. The SOC gets an alert, the user is notified, and we automatically assign them a quick security awareness training module. The office manager gets an email notification.
- Severity 3 (Critical): Ransomware is detected on a file server. This is an all-hands-on-deck event. The SOC immediately isolates the server from the network, the Incident Commander (the office manager) gets an urgent phone call, and the Executive Sponsor (the managing partner) is notified via a priority alert. The full ransomware playbook is activated.
This tiered system ensures the response always matches the risk. It prevents alert fatigue and keeps your team laser-focused on what actually counts.
How a 24/7 SOC Amplifies Your Playbooks
Your incident response playbooks are a fantastic starting point, but they’re only half the battle. A playbook sitting in a shared drive is just a document; it’s a great plan, but it can’t act on its own. The real magic happens when you connect that plan to a 24/7/365 Security Operations Center (SOC).
This is where your strategy gets a pulse. When a SOC integrates your playbooks, they aren’t just reading a set of instructions—they’re codifying them into their security platforms. This turns your carefully planned response steps into a living, automated defense system that works for you around the clock.
From Hours to Minutes with Machine-Speed Containment
When an attack hits, every second counts. A human-only response, even one guided by a well-written playbook, has built-in delays. An employee has to see the alert, find the right playbook, get the necessary approvals, and then manually execute the containment steps. That can easily take hours.
A SOC-driven response crushes that timeline from hours down to minutes, or even seconds.
Let’s walk through a real-world scenario. Imagine an employee at your Orlando office clicks on a malicious link at 10 PM on a Friday. Here’s how a SOC uses your playbook to shut down the threat before you even get a notification:
- Automated Trigger: The endpoint detection and response (EDR) tool on the employee’s laptop spots the suspicious activity and flags a high-priority alert.
- Playbook Execution: The SOC’s security platform instantly recognizes the alert type and triggers your pre-approved "Malware Infection" playbook.
- Machine-Speed Action: Without any human intervention, the platform executes the first containment step in your playbook—isolating the infected laptop from the network to stop the malware from spreading.
- Simultaneous Alerting: At the exact same time, the system sends an automated notification to your designated Incident Commander and logs every action for later review.
All of this happens before an analyst even has to touch a keyboard. Your playbook provided the "what," and the SOC provided the "how," executing it instantly to stop an attacker’s lateral movement in its tracks. Our guide on setting up a security operations center for your small business takes a deeper dive into how this integrated defense works.
A U.S.-Based SOC Guided by Your Business Priorities
For business owners in Central Florida, from Tampa to Orlando, the value of a 24/7/365 U.S.-based SOC is immense. Cyber threats don't stick to a 9-to-5 schedule. An attack is just as likely to unfold on a holiday weekend as it is in the middle of your busiest workday.
While a dedicated SOC provides that constant vigilance, it’s the guidance from your playbooks that makes it truly effective. Your playbooks are what tell the SOC what actually matters to your business.
By integrating your playbooks, the SOC isn’t just reacting to generic alerts; it’s executing a response strategy tailored to your specific operational needs and risk tolerance. It becomes an extension of your team, enforcing your rules even when you’re not there.
This partnership is what ensures security actions align with business goals. For example, if a non-critical server shows odd behavior, your playbook might instruct the SOC to simply monitor and report back. But if that same behavior appears on the server holding your client financial data, the playbook will demand immediate isolation and escalation.
That's a critical distinction the SOC can only make with your predefined instructions. This intelligent, customized response is the key to protecting what matters most without bringing your entire operation to a halt over a minor issue. It's the ultimate peace of mind.
Testing Your Playbooks for Real-World Resilience
Let’s be honest: an incident response playbook that hasn't been tested is just a theory. It’s a well-intentioned document sitting in a folder, but it’s guaranteed to have hidden flaws that will only show up under the pressure of a real attack. For a busy SMB, regular testing is what turns that paper plan into battle-tested muscle memory.
This isn't about running massive, time-consuming drills every week. It's about weaving practical, manageable tests into your routine to make sure your strategy actually works. These exercises are where you find the small but critical gaps—an outdated contact number, a technical process that fails, or a communication breakdown—before a real crisis does it for you.
Starting with Tabletop Exercises
The best place to start is with a tabletop exercise. Think of it as a structured "what if" conversation. You get your incident response team in a room—your Incident Commander, tech leads, and other key players—and talk through a specific scenario.
For example, your scenario for a construction company in Lakeland could be: "A phishing email was reported, and it looks like our project manager's credentials have been compromised."
From there, the exercise leader walks the team through the playbook, asking pointed questions:
- "According to the playbook, what's our very first move?"
- "Who owns the task of disabling the user account?"
- "How do we verify the account is locked and check for any unauthorized activity?"
- "What's the next communication that needs to go out, and who is responsible for sending it?"
This simple discussion quickly uncovers confusion, incorrect assumptions, and gaps in your process without touching a single live system. It's a low-stress, high-impact way to build team confidence and polish your playbooks.
Advancing to Breach and Attack Simulations
Once your team has a few tabletop exercises under their belt, it's time to level up. A breach and attack simulation (BAS) is where you use safe, controlled tools to mimic parts of a real attack and see what happens.
This could mean running a simulated ransomware agent on an isolated, non-critical machine. Did your endpoint protection software catch it and fire an alert? Did the SOC receive that alert and kick off the right playbook?
These simulations test both your technology stack and your team's response. They prove that your automated containment rules are working and that your people can interpret the alerts correctly and take the right next steps. To build truly robust playbooks, you have to include and regularly perform scheduled disaster recovery testing to ensure your recovery steps are just as solid as your initial response.
The goal of testing isn't to pass or fail. It's to find your weak points in a safe environment. Every gap you uncover during a drill is one less vulnerability an attacker can exploit during a real incident.
The financial incentive for this diligence is staggering. Organizations that lack documented and tested incident response plans face an average breach lifecycle of 258 days. For those who have them, it’s just 189 days. That 69-day difference can easily be a death sentence for a small business, like a veterinarian or an accounting firm in Central Florida. Despite proof that regular drills save an average of $1.49 million per breach, a shocking 30% of companies actually test their plans.
Turning Lessons Learned into Action
After every test—whether it’s a quick tabletop chat or a full-blown simulation—the most critical step is the post-mortem. This is where you sit down and document what worked, what didn't, and what needs to be fixed.
Was the playbook clear and easy to follow? Were there steps that were confusing or impossible to execute? Did a piece of technology fail?
The answers to these questions must be used to immediately update your incident response playbooks. This creates a powerful cycle of continuous improvement, making your plans stronger and more resilient with every test. Our article on disaster recovery testing offers more ideas on building this resilient mindset. This consistent refinement is what separates a static document from a living, breathing defense strategy that truly protects your business.
Your Questions About Incident Response Playbooks
Even with a clear plan, I find that many business owners in Central Florida have the same practical questions when it comes to incident response playbooks. It's smart to ask them. This is an investment in your company’s resilience, so let's get you some straightforward, no-nonsense answers.
How Many Playbooks Does My Small Business Really Need?
You don't need a library of playbooks to be protected. The trick is to start small and zero in on the 3-4 most probable and impactful scenarios that could hit your business. It's always quality over quantity.
For a professional services firm here in Orlando, for instance, we almost always start with playbooks for:
- Ransomware attacks
- Business Email Compromise (BEC)
- A lost or stolen company laptop with client data
A medical practice over in Tampa, on the other hand, has a different set of priorities. Their biggest cybersecurity concern is a data breach involving protected health information (PHI), so that playbook comes first due to strict HIPAA compliance rules. The goal is to cover your most significant risks first. A good security partner can run a quick risk assessment to pinpoint these, making sure your effort goes where it counts.
We Are a Small Team—How Can We Possibly Manage This?
This is probably the most common concern I hear, and it’s a valid one. It’s also exactly where a co-managed IT partnership proves its worth. Nobody expects you to become a team of cybersecurity experts overnight. In fact, a good incident response playbook makes it easier for a small team by laying out clear, manageable roles.
During an incident, your playbook will map out simple, non-technical tasks for your internal staff. Your Office Manager might be responsible for sending out pre-approved internal updates using a template. Meanwhile, your partner's 24/7 Security Operations Center (SOC) is handling the heavy lifting—the technical containment, threat removal, and system restoration.
The playbook is the bridge that makes this teamwork seamless, not chaotic. It lets your people focus on keeping the business running while expert engineers neutralize the threat. Everyone knows their role, and confusion is kept to a minimum.
Is Creating and Testing Playbooks Expensive?
The investment in creating and testing incident response playbooks is pocket change compared to the catastrophic cost of a real data breach. The price of an attack isn't just a ransom payment; it’s the regulatory fines, the crushing reputational damage, and the extended downtime that can easily put a small business under.
When you work with a managed service provider, playbook development and testing are typically woven directly into your security program. These become regular activities, like a Quarterly Business Review (QBR), not some massive, one-time project with a scary price tag. This approach makes proactive defense accessible and affordable, reframing it from an expense into a smart investment in your company's future.
How Often Should We Update Our Playbooks?
Your playbooks have to be living documents. A playbook that’s six months out of date can be just as dangerous as having no playbook at all. If it’s just collecting digital dust on a server, it’s useless.
We recommend a full review and update on a clear schedule:
- At least annually: This keeps the plans aligned with your current business goals and team structure.
- Whenever a major business change occurs: Think adopting new critical software, moving offices, or changes in key personnel.
And this is the most critical part: after any security incident or testing drill, your playbooks must be updated immediately with the lessons you learned. This cycle of continuous improvement is what keeps your response strategy sharp and effective against threats that are changing all the time.
Ready to move from theory to action? Cyber Command, LLC specializes in building practical, actionable incident response playbooks for businesses across Central Florida. We integrate them with our 24/7 SOC to provide a defense that works around the clock. Let's build your resilience together.