Expert IT Support in Orlando, FL: Your 2026 Guide
If you're running a law firm in Winter Park, a dental practice near Lake Nona, or a growing services company anywhere in Central Florida, you already know the pattern. Someone can't access Microsoft 365. The line-of-business app slows down. A printer goes offline before a client meeting. An employee clicks something they shouldn't. Suddenly you're acting as the IT manager instead of the business owner.
That's why businesses search for IT support in Orlando, FL. They don't need another vendor who shows up after something breaks. They need a partner who keeps operations stable, protects sensitive data, and gives leadership back its time.
Why Smart IT Support Is Mission-Critical in Orlando's Economy

Orlando isn't a one-industry town anymore, and your IT strategy shouldn't behave like it is. The Orlando Economic Partnership reports that 81% of workers are employed outside leisure and hospitality and cites Orlando as No. 1 in the country for job growth. It also notes that Florida ranks No. 4 in the U.S. for high-tech employment with more than 335,000 IT professionals. That combination changes the IT conversation for every small and mid-sized business in the region.
A more diversified economy means more offices, more regulated data, more cloud applications, more remote staff, and more endpoints to secure. It also means more competition for technical talent. If you're trying to hire one internal IT generalist and expecting that person to cover support, security, cloud, compliance, and strategic planning, you're setting them up to fail.
Orlando businesses are operating in a more complex environment
A CPA firm in Maitland doesn't have the same risk profile as a retail storefront. A medical spa has patient data, imaging systems, and uptime concerns. An engineering firm has large files, specialized applications, and field collaboration needs. Even if your company isn't large, your technology stack probably is.
That matters because complexity compounds. One unmanaged laptop, one weak MFA setup, one aging firewall, one backup that hasn't been tested. That's how routine inconvenience turns into lost billable time, missed appointments, or a security event.
Practical rule: If your team depends on cloud apps, mobile devices, and client data every day, IT isn't overhead. It's part of revenue delivery.
Why outsourcing makes business sense here
In Orlando, speed and continuity matter more than ownership of the IT org chart. You don't get points for handling everything in-house if response times are slow, documentation is weak, and nobody is watching security after hours.
Smart outsourced support gives SMBs what they usually can't build efficiently on their own:
- Continuous coverage: Your staff needs help when issues happen, not when one internal person is available.
- Standardized operations: Patch management, endpoint protection, user onboarding, and vendor coordination should follow a system.
- Predictable delivery: You should know who owns escalations, reporting, backups, and security reviews.
- Business focus: Leadership should spend time on hiring, sales, patient experience, and operations. Not router reboots and license disputes.
The strongest Orlando businesses treat IT as a managed function, not a side task. That's the shift. Once you make it, technology stops dragging the business down and starts supporting growth.
The Modern IT Support Stack What Orlando Businesses Get
Monday at 8:12 a.m., your front desk cannot print intake forms, a partner cannot access email on a phone, and a storm warning is already building off the coast. That is what IT support looks like in practice for an Orlando business. You do not need a vendor who waits for tickets. You need a managed system that keeps staff working, protects client data, and holds up when weather and security problems hit at the same time.
Orlando companies should expect IT support to cover five connected functions. If a provider is weak in one, the rest of the stack gets shaky fast.
The five layers that matter
Help desk and user support come first. Staff need fast answers, clear ownership, and real escalation paths. For a law office, that means document access problems get fixed before billable work stalls. For a medical practice, it means front-office staff can keep scheduling and checking in patients without chaos.
Monitoring and infrastructure management is next. Firewalls, Wi-Fi, switches, servers, line-of-business devices, and internet circuits need active oversight. Good providers catch failing hardware, overloaded networks, and recurring errors before your team starts reporting them.
Security operations sits in the middle of the stack because every other layer depends on it. Endpoint protection, patching, MFA enforcement, identity controls, email security, log review, and incident response should be built into support. In Central Florida, that matters even more for firms handling patient records, financial data, or sensitive client files.
Cloud and identity administration is where many Orlando businesses either gain efficiency or create constant friction. Microsoft 365 setup, SharePoint permissions, Teams support, user provisioning, device policies, and SaaS access all need consistent management. If your provider treats cloud work like occasional project labor, expect permission sprawl and support churn.
Backup, disaster recovery, and continuity closes the gap between an outage and a business shutdown. In Florida, hurricane planning is part of IT support, not a separate conversation. Backups need verification, recovery steps need testing, and remote work options need to function when the office does not.
What strong support looks like day to day
A modern provider does more than answer tickets. They run the environment.
Here is what that looks like in practice:
- A new employee starts next week: the laptop is configured, Microsoft 365 is ready, MFA is enforced, email signatures are set, and access matches the role on day one.
- A workstation misses critical patches: monitoring catches it, remediation starts, and the issue does not sit unnoticed until malware finds it.
- A medical office loses access to a cloud app: support handles triage, vendor coordination, and user communication without leaving staff to chase three different companies.
- A storm threatens office access: remote access, call routing, file availability, and recovery priorities are already documented and tested.
- A hospitality group adds locations or seasonal staff: the provider can standardize devices, permissions, and onboarding using a process built for distributed operations. Businesses with that model can review this IT support guide for hospitality operations.
One more point matters here. Good support reduces repeat problems. If the same login issue, Wi-Fi complaint, printer failure, or licensing mess keeps coming back, your provider is doing ticket management, not IT management.
What to avoid
Do not hire a firm that only talks about remote troubleshooting and response times. Ask how they handle patching, identity security, backup testing, Microsoft 365 administration, vendor escalation, and hurricane readiness.
Avoid providers that separate cybersecurity from everyday support unless you have a strong internal IT lead managing both sides. That split creates gaps, and gaps are where Orlando businesses lose time, money, and trust.
Business IT support should keep your company available, secure, and productive. That is the standard.
Matching IT Services to Your Industry Needs in Central Florida
A Winter Park law firm, a Lake Nona medical practice, and an Orlando field service company can all buy "managed IT." Only one problem. The same support model will fail at least two of them.
Central Florida businesses operate under different pressures. Professional services firms need tight control over client files and staff access. Medical practices need stable systems at the front desk, in exam rooms, and across billing workflows. Companies with mobile teams and multiple locations need dependable connectivity, secure remote access, and device standards that hold up outside a single office. Add hurricane risk, seasonal staffing swings, and a steady stream of phishing and account takeover attempts, and industry fit stops being a nice extra. It becomes a buying requirement.
Professional services firms
Law firms, accounting offices, consultants, architects, and engineering groups usually depend on a small internal admin team, not a mature IT department. That creates predictable risk. Files live in too many places, permissions drift over time, and former employees keep access longer than they should.
The right support plan for these firms starts with control.
Prioritize these areas:
- Access management: Enforce MFA, conditional access, and fast offboarding for every user with client or financial data.
- Document security: Lock down SharePoint, OneDrive, and email permissions so confidential files do not spread across personal devices and unmanaged folders.
- Standardized devices: Give partners, project managers, and support staff the same baseline security settings, encryption, and update policies.
- Audit readiness: Keep user access, device inventory, and policy changes documented so leadership is not guessing during a client review or insurance questionnaire.
If a provider talks mainly about ticket response and password resets, keep looking. Professional services firms need policy discipline as much as they need help desk coverage.
Privately owned healthcare practices
Medical, dental, ortho, med spa, veterinary, and specialty practices lose money fast when systems slow down. The front desk feels it first. Scheduling stalls, intake backs up, billing gets delayed, and staff start creating workarounds that create security problems later.
Support for healthcare practices should be built around workflow, not generic uptime promises. Your IT partner needs to understand how your EHR or practice management platform, phones, imaging, printers, and cloud apps affect the patient experience hour by hour. They also need to work directly with software vendors instead of leaving your office manager stuck in the middle.
Focus on these requirements:
- Fast issue triage for patient-facing systems: Front-desk and clinical tools get priority over low-impact office annoyances.
- Security built into daily operations: User access, email protection, endpoint security, and backup checks need to be routine, not occasional projects.
- Vendor coordination: Your provider should own communication with practice software, VoIP, imaging, and internet vendors.
- Storm-ready continuity: If your office closes for weather, staff still need a secure way to handle scheduling, communication, and core business functions.
For businesses with visitor-driven operations or guest-facing technology needs, this IT support guide for hospitality operations in Central Florida gives a useful comparison point on uptime and continuity planning.
If your front desk depends on the system being up, slow support is an operations problem, not an IT inconvenience.
Industrial and field service companies
This group gets underestimated. It should not.
Many Central Florida service businesses run across warehouses, job sites, vehicles, and branch locations. They depend on aging printers, scanners, tablets, mobile phones, dispatch software, and line-of-business equipment that cannot be replaced on a neat three-year cycle. Support has to fit that reality.
Their IT priorities are usually different from an office-based firm:
- Reliable site-to-site connectivity: Dispatch, accounting, and field teams need stable access to shared systems.
- Secure mobile access: Technicians need phones, tablets, and laptops that are protected without making logins so painful that people work around them.
- Network segmentation: Guest Wi-Fi, office traffic, cameras, and operational devices should not all sit on the same network.
- Hardware lifecycle planning: Older equipment needs a support plan, a replacement timeline, and clear ownership before it fails during busy season.
A provider that only knows office IT will struggle here. You want a partner that can talk to operations managers, understand site constraints, and keep business moving during storms, outages, and hardware failures.
Buy alignment, not a generic bundle
A smart IT partner maps support to your actual workflow, risk, compliance pressure, and continuity requirements in Central Florida. If they pitch the same stack the same way to a veterinary clinic, a CPA firm, and a multi-site service contractor, they are selling a package.
You need a plan that fits how your business makes money and how it stays running when Florida weather and everyday security threats test it.
Decoding Pricing Models Flat-Rate Partnership vs Break-Fix
Most SMBs don't choose the wrong IT support because they're careless. They choose it because reactive support looks cheaper at first glance. It isn't.
Break-fix pricing feels simple. Something breaks, you call someone, they bill time and materials. The problem is that this model rewards activity, not stability. If your environment is messy, the invoices keep coming.

The real difference is incentive alignment
Flat-rate managed services work differently. You pay for ongoing support, maintenance, monitoring, and standardized service delivery. That changes the provider's incentive. They benefit when your systems are healthy, documented, and secure.
Break-fix providers benefit when your systems stay reactive.
That's why I almost always recommend flat-rate support for established Orlando businesses. If you rely on technology every day, variable emergency billing is the wrong operating model.
IT Support Pricing Models Compared
| Feature | Flat-Rate Managed Services | Break-Fix Support |
|---|---|---|
| Cost structure | Predictable recurring fee | Variable charges when issues occur |
| Provider mindset | Prevent problems through maintenance and monitoring | Respond after failure |
| Security posture | Usually integrated into ongoing management | Often separate or inconsistent |
| Planning | Supports budgeting and operational standards | Little long-term alignment |
| Documentation | More likely to be maintained as part of service delivery | Often incomplete or ticket-specific |
| Business outcome | Greater consistency and accountability | Repeated disruption and cost surprises |
When break-fix still shows up
Break-fix can make sense for very small firms that barely depend on technology, have minimal data exposure, and can tolerate downtime. That's a narrow slice of the market. It doesn't describe most professional firms, healthcare practices, or multi-site operations in Central Florida.
For everyone else, break-fix usually creates four predictable problems:
- Budget instability: You can't plan accurately when support costs spike during failures.
- Delayed maintenance: Preventive work gets postponed because it isn't built into the relationship.
- Weak accountability: Nobody owns standards, roadmaps, or recurring problem patterns.
- Security drift: Patches, device hygiene, and access controls slip over time.
What to ask before you sign
Don't just ask, "What's your monthly rate?" Ask what the agreement includes.
- Covered systems: Which devices, users, cloud services, and locations are in scope?
- After-hours support: Is support available when your team needs it?
- Security services: Are endpoint protection, patching, and response processes included?
- Project work: What happens when you need onboarding changes, office moves, or vendor coordination?
A flat-rate agreement isn't valuable because it's flat-rate. It's valuable when it bundles the right responsibilities and removes surprises. That's the standard you should use.
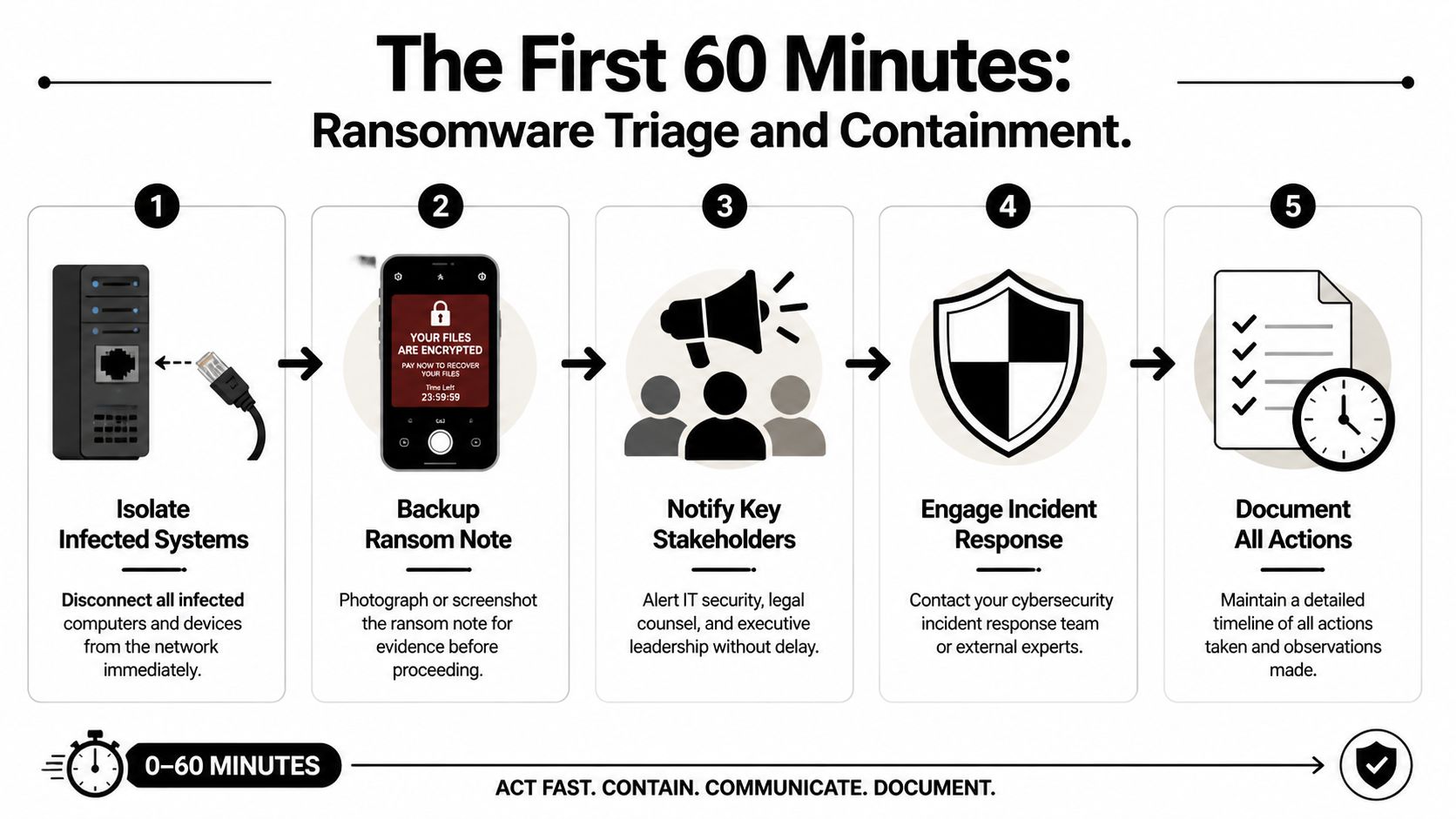
Cybersecurity and Disaster Recovery A Non-Negotiable for Florida Businesses
If you're evaluating IT support in Orlando, FL and cybersecurity isn't central to the conversation, you're talking to the wrong provider.
Most small businesses don't fail because of one dramatic technical event. They get worn down by preventable incidents. A spoofed invoice email. A compromised mailbox. A workstation with poor patch hygiene. A user with too much access. These aren't edge cases. They're the daily reality of business IT.

What modern protection should include
A serious provider should be able to explain, in plain language, how they handle:
- Endpoint security: Laptops and desktops need protection, visibility, and consistent policy enforcement.
- Identity protection: MFA, account controls, and privileged-access discipline matter as much as antivirus.
- Threat monitoring: Someone needs to watch for suspicious behavior and act on it.
- Patch and vulnerability discipline: Known weaknesses shouldn't sit unattended.
- Incident response: Your provider should know what happens next if something goes wrong.
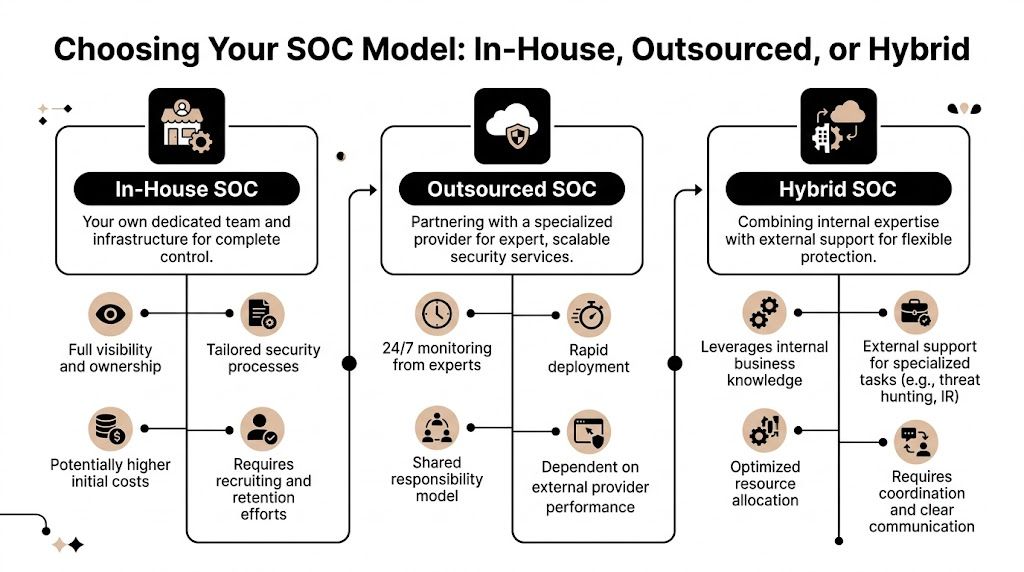
A SOC, or Security Operations Center, becomes important. You don't need the acronym. You need the function. A SOC provides ongoing threat monitoring, investigation, and response coverage so suspicious activity isn't discovered long after the damage is done.
One Orlando option in this category is Cyber Command, LLC's disaster recovery planning and managed security approach, which reflects the broader model businesses should expect from a security-aware MSP: documented recovery planning, active monitoring, and operational ownership rather than simple ticket handling.
Your IT provider doesn't need to promise perfection. They do need to prove they can detect, contain, and recover.
Hurricane-ready continuity is not optional in Florida
Local context matters. A lot of providers sell backup as if that's the same thing as continuity. It isn't. Backups are one piece. Continuity is the full operating plan.
In Orlando, a provider's hurricane posture deserves direct scrutiny. Local analysis highlights "hurricane-ready disaster recovery" as a key buying criterion for Orlando businesses. That's exactly right.
A real continuity plan should answer practical questions:
- If the office is inaccessible, can staff work remotely without chaos?
- If internet service is disrupted, what systems remain available in the cloud?
- If a core file set or business app is corrupted, who restores it and in what order?
- If a key vendor goes down, who coordinates the workaround?
For a useful outside perspective on the relationship between operational continuity and technical restoration, that AuditReady piece is worth reading. It makes an important distinction many SMBs miss. Business continuity keeps operations moving. Disaster recovery restores systems and data. You need both.
What Orlando owners should demand
Don't let a provider hide behind jargon. Ask for specifics.
Request their backup scope. Ask how recovery is tested. Ask whether remote operations are part of the continuity plan or just an assumption. Ask who owns communication during an incident. Ask how they prioritize systems for recovery.
Then listen carefully. If the answers are vague, the plan is vague.
A Florida business without a continuity plan isn't prepared. It's exposed.
How to Choose the Right IT Partner in the Orlando Area
Choosing IT support shouldn't feel like buying office supplies. You're choosing the team that will influence uptime, security, onboarding, vendor sprawl, and the speed of your day-to-day business. That decision deserves a tougher standard than "they seemed nice on the sales call."
The first filter is simple. Can this firm support your business the way it operates, not the way they wish it operated?

Ask about service design, not just support
A lot of providers blur the line between basic ticket handling and broader IT operations. If you want a quick primer on that difference, this explanation of helpdesk vs service desk is useful. The short version is that you want more than a reactive queue. You want a provider that can support users and manage service delivery.
Use these questions in every evaluation:
- Response commitments: What are the actual response targets for urgent, normal, and low-priority issues?
- Escalation ownership: When the issue involves Microsoft 365, internet, phones, or a line-of-business vendor, who coordinates the fix?
- Reporting: Will you receive useful reporting on tickets, assets, security issues, and recurring risks?
- Industry familiarity: Have they worked with firms like yours, with your workflow and compliance pressure?
- Standardization: Do they have a clear approach to device setup, patching, documentation, and access management?
Don't ignore on-site support
Remote support handles a lot. It doesn't handle everything. For multi-location companies or businesses with physical infrastructure, on-demand on-site support, often called "smart hands," is a crucial differentiator for resolving hardware, cabling, and peripheral issues that can't be fixed remotely.
That matters more than many owners realize. A dead firewall, failed switch, bad cabling run, broken docking setup, or printer issue tied to local hardware needs hands-on work. If your provider can only remote in, you're still exposed.
A practical shortlist test
Before you sign anything, ask each provider for these specifics:
- Show me your onboarding process. If they can't explain how they take over support cleanly, expect confusion later.
- Explain your security stack in plain English. Jargon-heavy answers usually hide thin delivery.
- Tell me how you handle after-hours incidents. You need clarity, not assumptions.
- Describe your local support capability. Can they show up when hardware is the problem?
- Walk me through your documentation and review cadence. Good partners maintain visibility.
- Clarify contract boundaries. What's included, what's excluded, and what triggers extra charges?
For a deeper buyer checklist, this managed service partner selection guide is a practical reference.
Choose the provider who thinks like an operator. Avoid the one who only thinks like a ticket queue.
A good Orlando IT partner should reduce noise, tighten security, and make your business easier to run. If they can't do those three things, keep looking.
If your business needs a more disciplined approach to IT support in Orlando, FL, Cyber Command, LLC is one local option to evaluate. They provide managed IT, co-managed IT, cybersecurity, cloud services, and live helpdesk coverage for Central Florida organizations that want predictable service, stronger security, and a partner who can support day-to-day operations as well as continuity planning.