What Is a Security Operations Center? A Guide for FL SMBs
TL;DR: A Security Operations Center (SOC) is the centralized hub that watches your business for threats, responds to incidents, and helps prevent repeats. Two of the most important ways to judge whether it’s working are Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR), and a 2019 SANS Institute SOC survey found that 58% of SOCs saw a lack of skilled staff as the top barrier to excellence while 50% cited insufficient automation (SANS Institute SOC survey).
A SOC is your business’s digital fire department, alarm center, and night watch rolled into one.
- Detect: Watch systems continuously for suspicious activity before small issues become outages or breaches.
- Respond: Investigate alerts, contain threats, and guide recovery fast enough to protect uptime.
- Improve: Tune tools, close gaps, and use what happened this month to strengthen next month.
Your Business Is a Target What Happens Next
Monday starts badly. Staff at an Orlando professional services firm log in and can’t open shared files. A few systems are slow. One employee mentions a strange sign-in prompt from the weekend. Another says clients are already calling because documents didn’t go out on time.
At that moment, the business owner usually asks a simple question. Who’s watching this when we’re not? Not just during office hours. Not just when someone remembers to check alerts. All the time.
That’s the practical reason businesses start looking into what a Security Operations Center (SOC) is. A SOC exists because modern attacks rarely announce themselves clearly. They show up first as odd logins, unusual device behavior, failed backups, suspicious email activity, or access from places and times that don’t fit your normal business pattern.
What failure looks like for an SMB
For a Central Florida firm, the damage usually isn’t abstract. It looks like:
- Lost billable time: Attorneys, accountants, architects, and consultants can’t access the files they need.
- Interrupted patient or client service: Medical offices and specialty practices may lose scheduling, chart access, or communications.
- Operational delays: Industrial and field teams may lose visibility into systems, tickets, or inventory workflows.
- Reputational stress: Clients remember the day you went dark.
A cyber incident doesn’t have to become a headline to hurt the business. It only has to stop work.
Small and mid-sized businesses are attractive targets because they often have valuable data, lean internal IT, and little room for downtime. That’s why a SOC matters. It answers the question behind every security concern: if something starts going wrong at 2 a.m., who detects it, who decides what it means, and who acts before your Monday is ruined?
The Core Functions of a Security Operations Center
A Security Operations Center does three jobs that matter to a business owner. It spots trouble early, responds before the issue spreads, and helps prevent the same failure from happening again.

For a law firm in downtown Orlando, that might mean catching unusual Microsoft 365 login activity before client files are exposed. For a medical practice, it can mean containing a compromised workstation before scheduling, billing, or patient records are disrupted. For a manufacturer or field service company, it may mean stopping an account takeover before production systems, inventory tools, or dispatch workflows are affected.
A SOC works like a digital fire department. The goal is not to admire alarms. The goal is to confirm what is happening, send the right response, and keep the incident from turning into downtime, data loss, or a compliance problem.
Detect threats before they spread
The first function is continuous monitoring. Analysts review activity from endpoints, firewalls, identity platforms, cloud apps, servers, and email systems, then decide whether the behavior fits your normal business pattern.
That sounds simple. It is not.
A small business can generate a constant stream of events, and plenty of them look suspicious at first glance. A SOC filters out noise so your team is not chasing harmless login prompts, routine software behavior, or expected admin activity while a real attack slips past.
A typical workflow includes:
- Tier 1 analysis: Review alerts, remove false positives, and identify what needs immediate attention.
- Tier 2 investigation: Add business context, such as who the user is, what device is involved, what data may be at risk, and whether similar activity appears elsewhere.
- Tier 3 hunting: Look for attacker behavior that may not have triggered a clean alert, such as persistence, lateral movement, or unusual command activity.
For SMBs in Central Florida, good detection is partly a tooling question and partly a context question. An after-hours login to a legal case system may be normal for one firm during trial prep and a major concern for another. A SOC that understands your operating hours, remote access habits, vendors, and compliance requirements makes better decisions faster. If you are comparing endpoint telemetry tools, this guide on understanding EDR and XDR for enhanced SMB cyber defense explains how that visibility supports SOC detection.
Respond fast enough to protect uptime
Detection has no business value unless it leads to action.
A SOC response can include isolating a laptop, disabling a user account, blocking malicious traffic, forcing a password reset, preserving evidence, or contacting leadership with a clear recommendation. The right move depends on the threat and the cost of disruption. Shutting down a device at 10 a.m. in a busy medical office has real operational impact, so response decisions need both security judgment and business awareness.
That trade-off matters. A weak response lets an attacker keep moving. An overly aggressive response can interrupt staff, delay appointments, or stop billing work that should have continued.
The best SOCs use playbooks so common incidents are handled consistently. Phishing, suspicious sign-ins, ransomware behavior, impossible travel, and unauthorized admin changes should not trigger a debate from scratch every time. They should trigger a practiced process.
Practical rule: A useful SOC reduces business interruption. Alert volume is secondary.
Improve the environment after the incident
A mature SOC does not close a ticket and move on. It uses what happened to tighten the environment.
That often includes tuning noisy detections, removing stale accounts, improving patching, expanding log coverage, updating response playbooks, and showing leadership where recurring risk keeps appearing. For regulated businesses in Orlando, this also supports audit readiness. Medical groups need clearer visibility into access and incident handling. Law firms need stronger protection around confidential client data. Industrial companies often need better oversight of remote access, third-party connections, and mixed IT and operational systems.
Fewer false alarms means less wasted labor, faster containment means less downtime, and better visibility means fewer expensive surprises. These factors demonstrate how the ROI of a SOC becomes evident. Over time, the SOC should lower the cost of chaos, not just produce security reports.
The Technology Powering a Modern SOC
The people in a SOC need the right tools or they’ll drown in data. Modern environments generate activity from laptops, servers, Microsoft 365, cloud platforms, firewalls, identity systems, and line-of-business apps. Without a way to collect and interpret that activity, important signals get buried.

SIEM is the central nervous system
A SIEM (Security Information and Event Management) platform pulls in security data from across the business and makes it searchable, correlated, and actionable. It’s the place where separate clues become a story.
A SIEM is foundational in a SOC because it can process millions of events to detect threats, and Tier 1 analysts typically triage 80 to 90% of thousands of daily alerts before escalating what needs deeper work (Rapid7 overview of SOC operations and automation).
For a business owner, the plain-English version is simple. Your firewall may know one thing. A laptop may know another. Microsoft 365 may show a strange sign-in. The SIEM helps analysts connect those dots.
If you want a deeper look at that layer, this guide on understanding security information and event management is a solid companion read.
EDR and XDR are the eyes and hands on endpoints
If SIEM is the nerve center, EDR and XDR are the sensors and response tools closest to the action. They watch what’s happening on devices and across security layers.
An endpoint tool can catch behavior that looks wrong even when a user hasn’t noticed anything yet. That matters because business interruptions often begin subtly. A machine starts running an unusual process. A script launches where it shouldn’t. Credentials get used in a pattern that doesn’t fit normal work.
Here’s what these tools usually contribute:
- Endpoint visibility: They show what happened on laptops, servers, and workstations.
- Behavior-based detection: They flag suspicious activity, not just known malware signatures.
- Containment options: They can help isolate a device or stop harmful activity while investigation continues.
- Cross-source context: In broader XDR workflows, they connect endpoint signals with identity, network, and cloud activity.
For an architecture firm, law office, or specialty practice, that means a suspicious event on one employee device doesn’t stay invisible until shared folders, email, or cloud apps are already affected.
SOAR turns repeatable response into machine-speed action
SOAR (Security Orchestration, Automation, and Response) handles the repeatable parts of incident response through playbooks. When a known type of event appears, SOAR can kick off the right sequence of actions without waiting for someone to do each step manually.
That matters because SOAR can reduce manual tasks by 60 to 80% and cut MTTR by up to 90% for common incidents, based on the Rapid7 reference already cited earlier in this section. In practice, that can mean an alert automatically triggers enrichment, ticketing, containment steps, and notification.
The best SOC technology stack doesn’t replace human judgment. It protects human judgment from getting wasted on repetitive work.
What works and what doesn’t
A lot of SMBs assume buying one security product means they “have a SOC now.” That’s not how it works. Tools are necessary, but tools without process create blind spots and confusion.
What tends to work:
- Integrated telemetry: Logs and alerts from identity, endpoints, cloud, and network controls feeding a common workflow
- Well-tuned detections: Rules refined over time so analysts see fewer meaningless alerts
- Clear response playbooks: Specific actions for common incidents like phishing, account compromise, and suspicious access
- Human review around the clock: Technology catches patterns. Analysts decide business impact.
What usually fails:
- Tool sprawl: Separate products that don’t share context
- Untuned alerting: Too much noise, too little confidence
- No ownership after hours: Alerts fire, but no one is accountable for triage and escalation
- Reporting that’s too technical: Owners hear about indicators and events, but not whether the business is safer
The point of modern SOC technology isn’t to impress you with dashboards. It’s to help security teams detect faster, respond with discipline, and keep your business operating.
Choosing Your SOC Model In-House Outsourced or Hybrid
Picking a SOC model is a business decision before it’s a technical one. The right answer depends on the size of your internal team, how much control you want to keep, how quickly you need mature coverage, and whether leadership wants to own staffing and tooling directly.
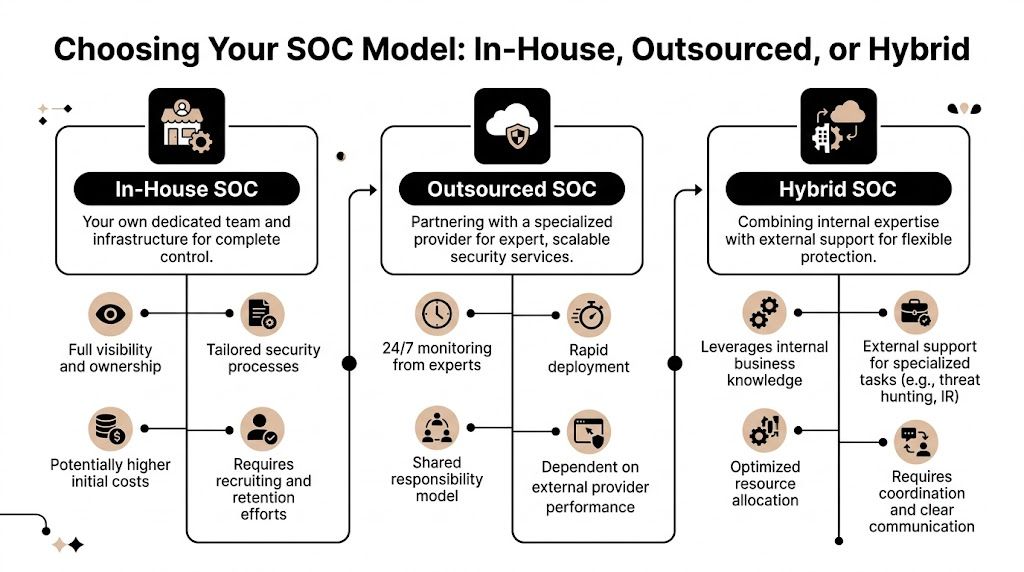
What each model really means
An in-house SOC means your company hires the analysts, owns the processes, operates the tools, and carries the burden of coverage. That can work for organizations with strong internal security leadership and enough scale to support it.
An outsourced SOC means a specialized provider handles monitoring, detection, investigation, and often response as a managed service. For many SMBs, this is the fastest path to mature coverage because the provider already has the people, workflows, and technology stack in place.
A hybrid or co-managed SOC splits responsibility. Your internal IT or security team keeps visibility and strategic control, while an outside partner provides continuous monitoring, specialized investigation, or after-hours coverage.
Most SMB owners don’t need to own every security function directly. They need confidence that someone competent is accountable when something happens.
SOC model comparison for SMBs
| Factor | In-House SOC | Outsourced SOC (MSSP) | Co-Managed/Hybrid SOC |
|---|---|---|---|
| Control | Highest direct control over people, tools, and process | Less day-to-day control, more dependence on provider workflows | Shared control with internal oversight |
| Staffing burden | High. Recruiting, retention, scheduling, and training stay on you | Lower. Provider supplies the operational team | Moderate. Internal team still needs ownership in key areas |
| Speed to maturity | Slower for most SMBs | Faster because the provider starts with an existing operation | Faster than fully in-house, slower than fully outsourced in some cases |
| After-hours coverage | Hard to maintain without a larger team | Usually built into the service | Often covered by the provider |
| Customization | Deep customization possible | Varies by provider | Strong if roles are clearly defined |
| Best fit | Larger organizations with internal security depth | SMBs that need mature security operations without building from scratch | Firms with capable IT leadership that want support, not full handoff |
The real trade-offs
For most Central Florida SMBs, the biggest challenge with in-house isn’t desire. It’s practicality. Security operations depend on people who can triage alerts, investigate suspicious activity, and make response decisions under pressure. That’s hard to build and hard to sustain.
Outsourcing solves many of those problems, but it creates a different risk. A provider may be technically strong yet operationally weak for your business if they don’t understand your workflows, compliance demands, and escalation expectations.
Hybrid models often work well for law firms, medical groups, and industrial organizations with internal IT staff who know the business but don’t want to run a full SOC alone. Internal teams keep context. External specialists provide scale and round-the-clock discipline.
A simple way to decide
Use these questions:
- Do you have internal security leadership? If not, fully in-house usually creates more exposure than confidence.
- Do you need coverage outside business hours? If yes, outsourcing or hybrid tends to make more sense.
- Do your systems support revenue every hour of the day? If uptime matters constantly, your monitoring model should too.
- Do you want strategic partnership or just alert handling? The answer helps separate commodity monitoring from true co-management.
The wrong model creates one of two problems. You either pay for complexity you can’t maintain, or you buy a service that never really fits your business. The right model gives you clear accountability, reliable coverage, and a realistic path to resilience.
The Business Case for Central Florida SMBs
A SOC isn’t just a security purchase. For many SMBs, it’s a business continuity decision. Orlando-area firms in legal, medical, financial, and industrial sectors rely on systems that have to be available, trusted, and compliant enough to support client and patient relationships.
When owners ask whether a SOC is worth it, the better question is usually this: what does it cost the business when no one is actively monitoring, investigating, and containing threats?
Why the ROI conversation matters
One of the biggest gaps in the market is that plenty of SOC content explains the technology, but not the business case. IBM notes that evaluating a SOC provider is difficult and that online content often misses the question SMBs care about most: how to justify the investment and measure ROI for firms with limited IT budgets (IBM on the ROI gap in SOC evaluation).
That’s exactly where many Central Florida businesses get stuck. They understand risk in theory. They don’t always have a clean way to connect a security service to uptime, compliance, and financial stability.
What ROI looks like in practice
The clearest operational metric is Security Incident Volume, which helps a SOC understand what’s reaching the level of a confirmed threat and whether the environment is becoming more or less stable over time. Mature teams also focus on strong containment, with incident containment rates commonly targeted at over 90%, and the same source notes that unpatched systems can drive 20 to 30% of incidents (CyberDefenders on SOC performance metrics and incident drivers).
For a business owner, that translates into several concrete outcomes:
- Less downtime: Faster containment means fewer hours of disrupted work.
- Lower cleanup burden: Smaller incidents are cheaper and easier to remediate than broad compromises.
- Better compliance posture: Security operations support the evidence, follow-through, and consistency many regulated firms need.
- Clearer budget decisions: Trends in incident volume tell leadership where controls are working and where spending should shift.
Security ROI often shows up as the problems that never reached your staff, your clients, or your patients.
Why this hits different in Orlando
Central Florida SMBs often have a mix of cloud services, legacy systems, mobile staff, third-party vendors, and lean internal IT. That combination increases the chance that small warning signs get missed until they become operational problems.
For a few common local business profiles, the value is easy to map:
- Law firms and accountants: Sensitive client records, email-heavy workflows, and high trust expectations make account compromise and data exposure especially painful.
- Medical and dental practices: Scheduling, patient communications, and regulated information create both uptime pressure and compliance pressure.
- Architects, engineers, and consultants: Shared documents, project deadlines, and outside collaboration mean any interruption quickly affects revenue and reputation.
- Industrial and field-service firms: Distributed devices and remote operations create more places where a threat can start unnoticed.
What doesn’t justify itself
A SOC doesn’t make financial sense if it’s treated like a dashboard subscription with vague monthly noise. Owners should be wary of any service that reports lots of alerts but can’t explain business impact, recurring causes, or whether the environment is improving.
The business case becomes stronger when the service ties operational data back to decisions. Which systems create the most risk? Which recurring alerts point to weak controls? Which business units need tighter identity protections or faster patching? That’s where cybersecurity becomes management information, not just technical reporting.
For Central Florida SMBs, the smartest reason to invest in a SOC is simple. You’re buying the ability to keep working when something goes wrong, and to reduce how often it goes wrong in the first place.
How to Choose the Right SOC Provider
A lot of providers can say they monitor alerts. Far fewer can explain how they reduce business risk, communicate during incidents, and prove value over time. If you’re evaluating options, you’re not buying software. You’re hiring an operational partner that will have a role in some of your worst business days.
If your team is also sorting through audit requirements and vendor questionnaires, it helps to understand adjacent compliance language too. This primer on What Is SOC Compliance is useful because many owners confuse security operations with attestation and reporting frameworks.
Questions that separate real providers from noisy ones
Start with these:
- How do you measure value beyond alert volume? A strong provider should talk about containment, recurring risk reduction, reporting quality, and business outcomes.
- What happens during a real incident? Ask who contacts whom, how escalations work, and whether they give clear decision support to leadership.
- How do you tailor playbooks to my environment? A legal office, specialty medical practice, and industrial firm don’t all need the same response priorities.
- What visibility will my internal team keep? You should know what data, dashboards, tickets, and reports remain accessible to you.
- How do you handle after-hours events? This reveals whether “24/7” is actual operations or just after-hours alert forwarding.
What good answers sound like
A provider doesn’t need to sound flashy. They need to sound operationally mature.
Look for signs like:
- Clear ownership: They can explain who triages, who investigates, and who approves disruptive actions.
- Business-aware communication: They can translate technical events into plain consequences for uptime, compliance, and decision-making.
- Structured reporting: They show patterns over time instead of sending disconnected alert summaries.
- Specific escalation logic: They know when to wake your team, when to isolate a device, and when to continue investigating discreetly.
If a provider can’t explain their reporting in business language, they probably can’t defend their value in budget season either.
Red flags worth noticing
Some warning signs appear early in the sales process:
- Generic promises: They claim broad protection but avoid explaining response steps.
- No discussion of ROI: They talk tools, not outcomes.
- Weak alignment with your industry: They haven’t thought through HIPAA-sensitive workflows, legal confidentiality, or operational technology realities.
- Alert-centric mindset: Everything is framed around notifications instead of resolution and prevention.
Use this shortlist before you sign
| What to ask | Why it matters |
|---|---|
| How do you report on value delivered? | You need more than raw activity counts. |
| What’s your incident communication process? | Good security fails if leadership gets confused during an event. |
| How much tuning and customization is included? | Untuned monitoring creates noise and frustration. |
| How do you support compliance needs? | Regulated firms need consistency, documentation, and follow-through. |
| How do you work with internal IT? | The relationship matters if you’re co-managed. |
The right provider should leave you with more clarity, not more jargon. If the conversation feels vague before the contract, it usually gets worse after signing.
Cyber Command's 24/7 SOC for Local Business Needs
For Central Florida SMBs, the ideal SOC partner isn’t just technically capable. The partner has to understand local business realities, limited internal headcount, and the fact that owners don’t want a pile of alerts. They want uptime, accountability, and a clear plan when something breaks.

Cyber Command, LLC has provided 24/7 SOC services since 2015, with a focus on proactive threat hunting and incident response for SMBs in Orlando and North Texas. The company also integrates threat intelligence and continuous compliance support through quarterly business reviews, with an operating model centered on uptime and measurable accountability instead of reactive, ticket-driven support (Cyber Command company background and SOC approach).
Why that model fits SMB reality
Many SMBs don’t need a giant enterprise security program. They need an operating rhythm that protects the business without forcing leadership to build and manage a full security department.
That means a practical SOC partner should bring:
- Continuous coverage: Threats don’t care whether your office is open.
- Threat hunting: Not just reacting to alerts, but looking for signs that something is wrong before it becomes disruptive.
- Incident response discipline: Knowing what to contain, when to escalate, and how to communicate clearly.
- Compliance support: Helping regulated organizations stay organized and prepared, not scrambling after the fact.
What local alignment changes
A provider serving Orlando and nearby markets sees the patterns SMBs deal with every day. Professional services firms often have high trust requirements and low tolerance for downtime. Medical organizations have patient flow and privacy concerns. Industrial firms care about reliability across locations and systems.
That business context matters because response priorities aren’t identical across industries. In one company, the critical issue is preserving client communications. In another, it’s restoring access to scheduling and records. In another, it’s making sure field or plant operations stay moving.
Security operations work better when the provider understands what your business cannot afford to lose for even one day.
What owners should take from this
The biggest difference between a generic monitoring service and a strong SOC partner is accountability. A mature partner should help leadership understand risk trends, not just incident tickets. It should also fit into broader IT planning, since security decisions affect vendor management, patching discipline, cloud use, and operational uptime.
For local businesses, that combination matters. It means security operations aren’t isolated from the rest of the business. They support it.
From Reactive Firefighting to Proactive Resilience
Once an Orlando business owner decides a SOC makes sense, the next question is usually operational, not technical. Who inside the company owns the relationship, what systems need to be visible on day one, and what gets escalated at 2 a.m. versus held for the morning?
That preparation work determines whether a SOC becomes a real operating function or just another vendor sending alerts.
For a Central Florida SMB, a good start is simple. Name one internal decision-maker. Confirm which assets matter most, such as Microsoft 365, line-of-business applications, cloud backups, remote access tools, and any system that keeps scheduling, billing, client files, patient records, or production moving. Then agree on response rules before the first incident, including who can approve containment, who must be notified, and what downtime the business can tolerate.
This matters a lot in local industries. A law firm may care most about preserving confidential client communications and document access. A medical practice may need fast action around account misuse without disrupting patient flow. A manufacturer or field service company may put plant systems, dispatch, or inventory platforms at the top of the list because even a short interruption can turn into missed jobs and lost revenue.
Co-managed security usually works best for SMBs here. The SOC handles monitoring, investigation, and after-hours response. Your internal team keeps control of business context, vendor relationships, and change management. That split is practical. It lowers staffing pressure, avoids building a night shift internally, and gives leadership a clear line between security work and business operations.
Teams also need a rhythm, not just tools. Monthly reviews should cover what was detected, which recurring issues point to weak processes, and where to spend next. Businesses that want to mature beyond alert review should also understand how ongoing hunting closes the gap between known detections and hidden attacker activity. This article on the business case for continuous threat hunting explained is a useful next read for that reason.
The companies that get the most value from a SOC treat it like part of daily operations, similar to alarm monitoring, insurance planning, or an on-call facilities process. Clear ownership, clear escalation paths, and clear priorities turn security from an occasional scramble into a managed business function.
If your organization needs a practical plan for 24/7 monitoring, threat hunting, incident response, and compliance support, talk with Cyber Command, LLC. Their team works with Central Florida SMBs to reduce downtime, improve accountability, and build a security operation that fits real business needs.