Why Mean Time to Resolution Is Your Most Critical Business Metric
When a critical server crashes at your Orlando medical practice or a ransomware attack paralyzes your Tampa law firm, every second of downtime is a direct financial drain. This is where Mean Time to Resolution (MTTR) comes in.
It’s the total time from the moment a digital problem is first detected until your business is completely back to normal. A low MTTR means you recover faster, protecting your revenue and reputation.
To help you get a quick handle on this metric, here's a simple breakdown.
MTTR at a Glance
| Component | Description | Business Impact |
|---|---|---|
| Detection | The moment an alert is triggered or a problem is reported. | Starts the clock on downtime costs. |
| Response | The time it takes for your team to begin actively working on the issue. | A slow response prolongs the problem and its financial impact. |
| Diagnosis | The process of identifying the root cause of the incident. | Inaccurate diagnosis leads to wasted effort and extended outages. |
| Repair & Recovery | The actions taken to fix the issue and restore full functionality. | This is the hands-on work that gets your business back online. |
| Verification | Confirming that the fix works and the system is stable and secure again. | Prevents recurring issues and ensures the problem is truly solved. |
Essentially, MTTR measures the entire lifecycle of an incident, from the first warning sign to the final "all clear." It's one of the most honest indicators of your IT team's effectiveness and your business's overall resilience against cyber security threats.
Your Business Is Leaking Money Until an Incident Is Resolved
Imagine a pipe bursts in your office. You wouldn't just turn off the water main and call it a day. You'd have to repair the pipe, dry the carpets, and make sure the space is safe and operational again.
A cybersecurity incident or IT failure works the same way. The clock is ticking, and a slow response means more damage, higher costs, and greater disruption. The longer it takes to resolve, the more it hurts your bottom line.
For businesses across Central Florida, from legal offices in Orlando to industrial firms in Tampa, this "damage" takes many forms:
- Lost Revenue: Every minute your systems are down is a minute you can't serve clients, process payments, or conduct business.
- Wasted Productivity: Your team is left unable to work, grinding operations to a halt while the payroll clock keeps ticking.
- Damaged Reputation: Unresolved cyber security issues quickly erode client trust, especially in industries like healthcare and finance where data security is everything.
The True Cost of Slow Resolutions
A slow incident response creates a domino effect. What starts as a minor network hiccup can quickly escalate into a full-blown operational crisis if you don't jump on it fast. A common concern for businesses is a phishing attack leading to a ransomware event, which can shut down operations for days or weeks if not handled swiftly.
That's why mean time to resolution isn’t just some IT statistic to track on a dashboard; it’s a direct measure of your business's ability to absorb a hit and get back on its feet.
To truly grasp the financial impact, think about the importance of digital analytics efficiency. Just like in analytics, every moment of inefficiency in your IT response translates directly into real, tangible costs.
A high MTTR is a symptom of a reactive, break-fix IT strategy. It’s a red flag that your business is vulnerable to long periods of disruption, creating unpredictable costs and operational chaos that can kill growth and hand your competitors an advantage.
This is why getting a handle on your MTTR is a competitive necessity. It forces you to shift from just fixing problems to building a resilient operational framework. For a deeper look at building this kind of resilience, our guide on business continuity and disaster recovery services offers some valuable insights.
Ultimately, a lower MTTR means less money leaked, more client trust retained, and a stronger, more resilient business.
Deconstructing the Incident Response Timeline
To really get a handle on Mean Time to Resolution, you have to look at the entire incident lifecycle, not just one piece of it. Think of it like a fire department responding to an emergency. Their clock doesn't start when they begin spraying water. It starts the second the alarm rings and only stops when the fire is completely out, the smoke has cleared, and the building is safe to re-enter.
That same all-encompassing view applies to your business's IT and cybersecurity incidents. MTTR isn't just about the time spent on the "fix." It’s the full story, tracking every single step from the moment an alert pops up until your business is 100% back to normal.
The Four Stages of Incident Resolution
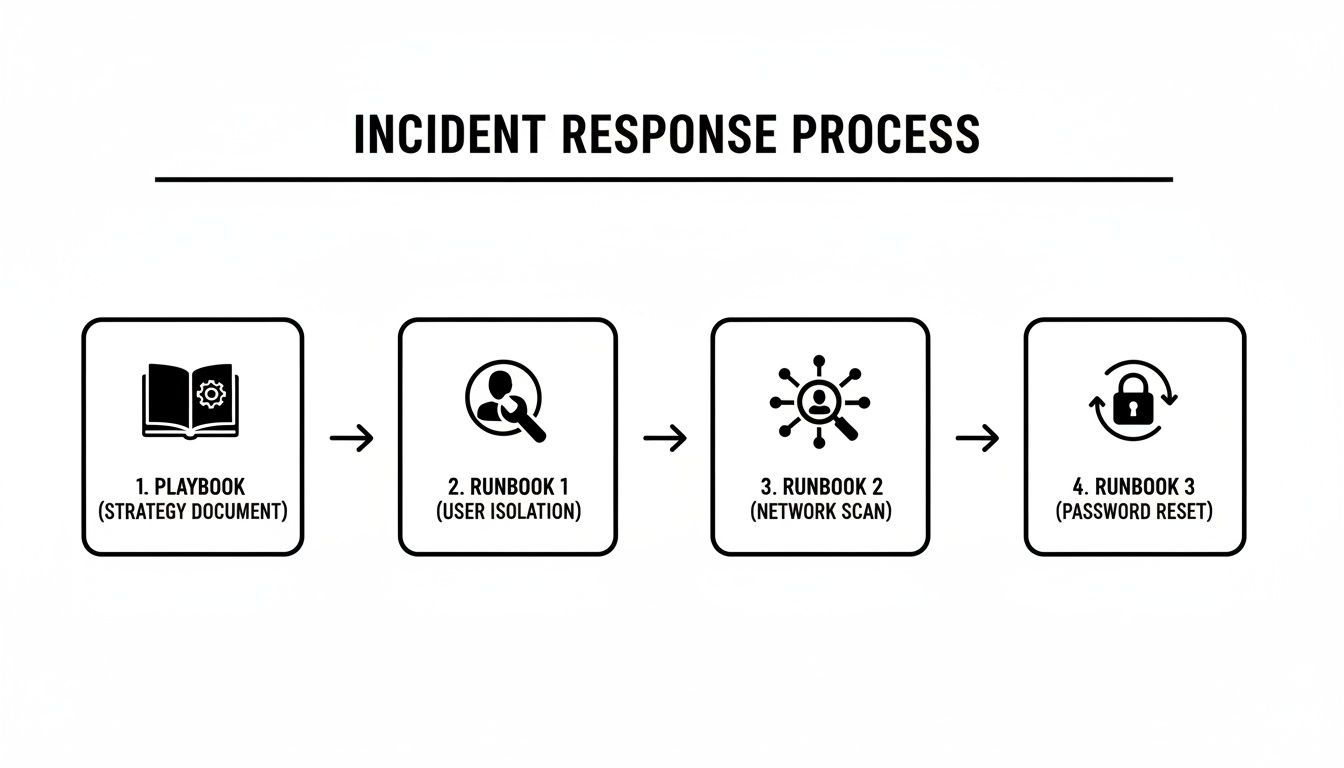
The journey from initial alert to full recovery can be broken down into four distinct stages. Delays in any one of these will drag down your overall MTTR, costing you time and money.
Detection: This is the starting gun. It’s the moment an issue is first spotted, whether it’s an automated alert from a security tool, an error message flashing on a screen, or an employee reporting they can’t get into a critical system.
Diagnosis: Once the alert is acknowledged, the real investigation begins. Your IT team or managed services provider digs in to figure out what’s happening, how bad it is, and what caused it. Is this a minor network hiccup or the start of a full-blown ransomware attack? Getting this diagnosis right is crucial for an effective response.
Remediation: This is the hands-on "fix" phase where the plan of action is executed. It could involve anything from restoring data from a backup and patching a vulnerability to isolating an infected device to prevent a cyber threat from spreading. This is what most people think of as the entire resolution process, but it's only one part of the timeline.
Resolution and Verification: This is the final, and arguably most important, stage. After a fix is in place, the team has to confirm that everything is stable, secure, and working as expected. This isn't just about making sure the problem is gone; it’s about making sure it won't pop right back up and that business can truly resume without a hitch.
Every second that ticks by during these stages has a financial impact. This flow shows how costs mount from the initial problem until your operations are fully recovered.
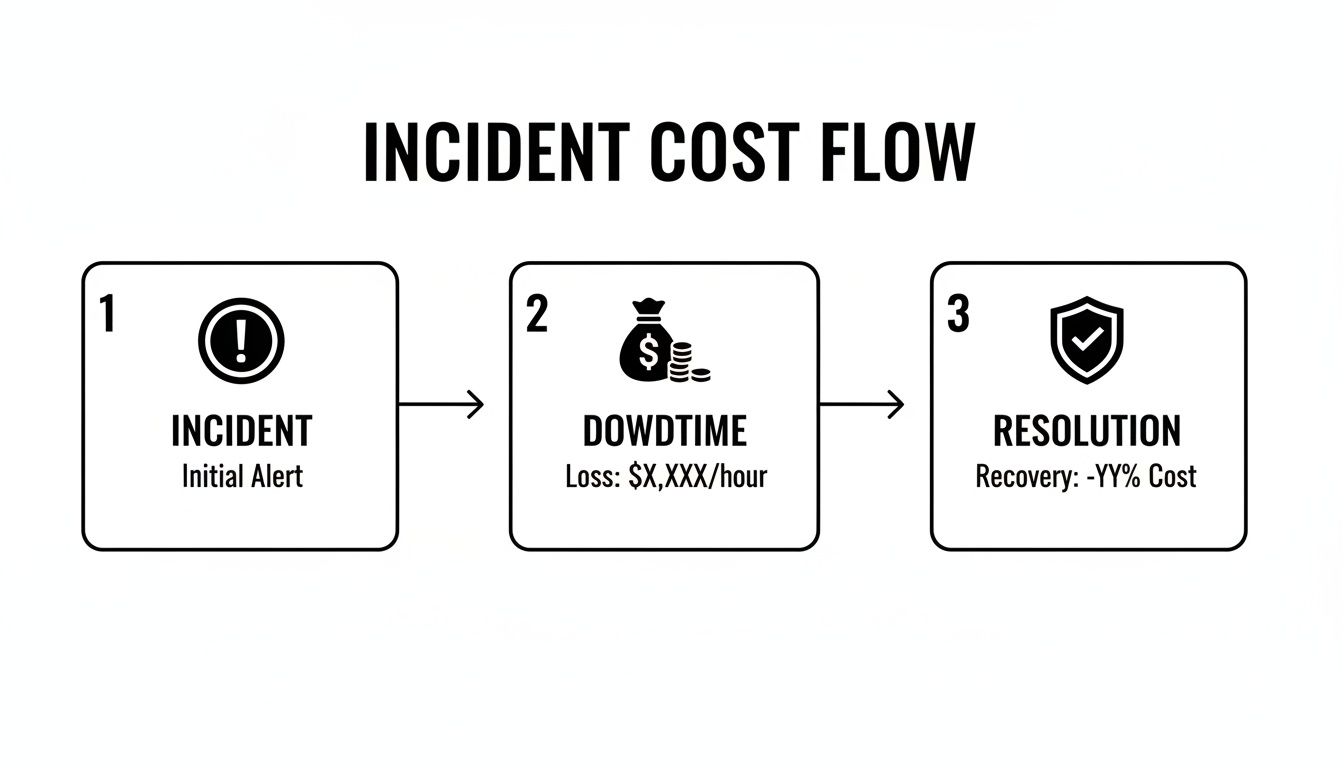
As you can see, downtime is the painful, expensive gap between the incident and its final resolution. Every minute you can shave off that time is money saved.
More Than Just a Technical Fix
It's easy to get MTTR confused with other metrics, but the difference is critical. For example, Mean Time to Detect (MTTD) only measures that first stage—how long it takes to know a problem exists. A low MTTD is great, but it’s just one piece of the puzzle. Similarly, Mean Time to Acknowledge (MTTA) only tracks how quickly your team starts working on a ticket.
True resolution isn't just about a technical repair; it's about complete business recovery. The MTTR clock only stops when your operations are 100% back to normal, ensuring genuine business continuity.
This is what makes Mean Time to Resolution the gold standard. It measures the complete timeline from alert to full incident closure. That’s why it’s a lifeline for any organization that depends on uptime and accountability. The math is straightforward: if you had 4 incidents that resulted in a total of 20 hours of downtime, your MTTR is 5 hours (20 hours / 4 incidents).
A well-defined timeline helps you spot bottlenecks in your process. If your diagnosis phase is always dragging on, it’s a red flag that you might need better monitoring tools or more experienced technicians on deck. By understanding each step, you can start building a much more effective response. For more information, check out our guide on crafting your incident response plan for max efficiency.
Alright, let’s move from theory to practice. Knowing what Mean Time to Resolution is conceptually is one thing, but actually calculating it for your business is where the rubber meets the road. This simple calculation gives you a brutally honest, data-driven look at how well your business weathers a storm.
It’s the first step in moving from a reactive, fire-fighting IT process to a proactive operational advantage.
The formula itself is refreshingly simple. You just take the total time spent resolving all incidents over a set period and divide it by the number of incidents you had in that same timeframe.
MTTR = Total Time of All Incidents ÷ Number of Incidents
This gives you a single, powerful number—the average time it takes your business to get back on its feet after something breaks. It’s the baseline you’ll use to measure improvement and hold your IT team or provider accountable.
Putting the MTTR Formula into Practice
Let's walk through a real-world scenario. Imagine an industrial firm here in Orlando has a rough month and gets hit with three separate IT incidents that grind their operations to a halt.
- Incident 1: Ransomware Attack: A nasty cyberattack encrypts their main server, making files inaccessible. From the moment it was detected to the point where the system was fully restored from backups and verified secure, the total downtime was 48 hours.
- Incident 2: Network Outage: A hardware failure took down the network across their entire office. The team managed to get it resolved in 6 hours.
- Incident 3: Critical Software Bug: A bug in their core operational software stopped all order processing. It took 10 hours to get the fix deployed and working correctly.
To figure out their MTTR for the month, we just add up the resolution times and divide by the number of incidents.
Total Time = 48 hours + 6 hours + 10 hours = 64 hours
Number of Incidents = 3
MTTR = 64 hours ÷ 3 incidents = 21.33 hours
For this company, it took an average of over 21 hours to fix each problem. As a business owner, that number should be a massive red flag. It shows a serious vulnerability; when things go wrong, the pain is long and expensive. For another business, five incidents taking 4, 12, 6, 9, and 9 hours respectively would result in an 8-hour MTTR—a much healthier baseline that many SMBs can use to gauge their helpdesk's performance.
Why You Must Segment MTTR by Severity
While an overall MTTR is a great starting point, it doesn't paint the whole picture. Lumping a minor printer jam in with a catastrophic data breach will seriously skew your data and can mask major cyber security risks hiding in plain sight.
A truly effective analysis means you have to segment your incidents by their severity.
Think about a law firm in Tampa. They should have drastically different expectations for fixing different types of problems.
- Critical (Severity 1): A system-wide outage, a data breach, or a ransomware attack. The business is at a complete standstill.
- High (Severity 2): A key application is down, or a whole department can't work.
- Medium (Severity 3): A single user is impacted, or a non-critical feature isn't working right.
- Low (Severity 4): A minor inconvenience with an easy workaround, like a quirky printer.
You can't afford to wait 24 hours to address a data breach, but you also wouldn't expect a printer jam to be fixed in 15 minutes. By calculating a separate MTTR for each severity level, you get a much clearer, more realistic view of your team's response capabilities. This practice is a core function of effective IT service management software, which helps automate all this tracking and reporting for you.
This segmented approach lets you set realistic targets. Your goal for a critical incident might be an MTTR of under 4 hours, while an MTTR of 48 hours for low-priority issues could be perfectly fine. It empowers you to stop treating every problem with the same five-alarm-fire urgency and start focusing your resources where they truly matter—on the threats that pose the biggest risk to your business.
What Is a Good MTTR in Your Industry
Once you start calculating your Mean Time to Resolution, the next question is always the same: "So, what's a good number?"
The honest answer? There’s no magic number that works for every business. A "good" MTTR is all about context—specifically, the severity of the problem and the industry you’re in.
Think of it this way: a total system outage at a busy Orlando law firm is a five-alarm fire. Every minute of downtime costs real money and client trust. But a slow printer at an industrial facility in Winter Springs? That's an annoyance, not a full-blown crisis. A one-size-fits-all MTTR target is just not practical.
A much smarter approach is to set different MTTR goals based on an incident's severity. This lets you focus your energy where it matters most: on the critical cyber security threats that can stop your business cold.
Benchmarks for Cybersecurity Incidents
In the high-stakes world of cybersecurity, MTTR isn't just a metric; it’s a direct measure of your defense. Speed is everything. For Central Florida businesses, especially those in finance, legal, or healthcare that handle sensitive data, knowing the industry benchmarks is the first step in figuring out if you're prepared.
Here's what the security world expects:
- Critical Vulnerabilities: Elite security teams aim to crush critical threats—like a zero-day exploit or active ransomware attack—within 24 to 72 hours. This is the gold standard for mature, proactive security.
- High-Risk Compliance Issues: For regulatory findings, frameworks like NIST SP 800-53 might give you a window of 30 to 90 days for remediation.
It's critical to see these numbers as the absolute maximum time you have, not a goal to aim for. As you'll find in expert cybersecurity guides, while a framework might allow 30 days, the real industry leaders resolve these issues in a fraction of that time. That’s how they demonstrate a truly superior security posture.
The gap between an acceptable MTTR and an excellent one is often the difference between just surviving an attack and stopping it before it does real damage. Elite security teams don't just meet compliance deadlines; they race against the clock to neutralize threats in hours, not days.
Getting those urgent threats resolved in under an hour—that's what separates a reactive IT department from a strategic security partner.
Why Your Industry Matters
What counts as a "good" MTTR changes dramatically depending on what your business does. A delay that’s a minor headache for one company can be a catastrophe for another.
Let's look at a few local examples here in Central Florida:
- A Medical Practice in Lakeland: If their patient record system goes down due to a cyberattack, it hits their revenue and patient trust instantly. For them, a critical MTTR of under 2-4 hours is a must.
- An Orlando Law Firm: Their case management software is their lifeline. If a data breach occurs, projects grind to a halt and client confidentiality is at risk. They must set an MTTR of 4-8 hours for high-severity issues.
- A Local Industrial Distributor in Tampa: A server outage that takes down their inventory system could throw their entire supply chain into chaos. Their target MTTR for a critical failure has to be as close to zero as possible to avoid a logistical nightmare.
At the end of the day, defining a "good" mean time to resolution means looking at your own operations, risks, and what you can't afford to lose. The goal is to set benchmarks that protect your revenue, your reputation, and your relationships. This is how you turn response time into a real business advantage—and it’s a key benefit of working with a 24/7 managed security provider.
Proven Strategies to Lower Your MTTR

Knowing your Mean Time to Resolution is the first step, but actually lowering it is how you build a more resilient—and profitable—business. A high MTTR is more than just a bad score; it’s a flashing red light signaling inefficiencies that are costing you money, client trust, and productive hours.
The good news? This isn't some abstract goal. Bringing that number down is entirely achievable with the right game plan. Each of the following strategies is designed to shrink the incident lifecycle, slash downtime, and protect your bottom line, whether you're a medical practice in Lakeland or a law firm in Orlando.
Implement a 24/7 Security Operations Center
Cyberattacks don’t punch a clock. A threat that pops up at 2 a.m. can cause catastrophic damage long before your team even sips their morning coffee. A 24/7 Security Operations Center (SOC) is your answer to this, eliminating that dangerous after-hours blind spot with around-the-clock monitoring and response.
Think of a SOC as your company’s dedicated security watchdog, staffed by experts who are actively hunting for threats. When an incident occurs, they respond in moments, not hours. This immediate action drastically shortens the detection and remediation stages of an incident.
For Central Florida businesses, this means:
- No More After-Hours Delays: An alert at midnight gets handled right then and there, stopping a minor issue from snowballing into a full-blown crisis by morning.
- Active Threat Hunting: A good SOC doesn’t just sit and wait for alarms. They proactively search for signs of compromise, stopping attackers in their tracks.
- Expert Response on Tap: You get immediate access to cybersecurity pros who know exactly how to contain and neutralize threats, putting a serious dent in your mean time to resolution.
Develop a Clear and Practiced Incident Response Plan
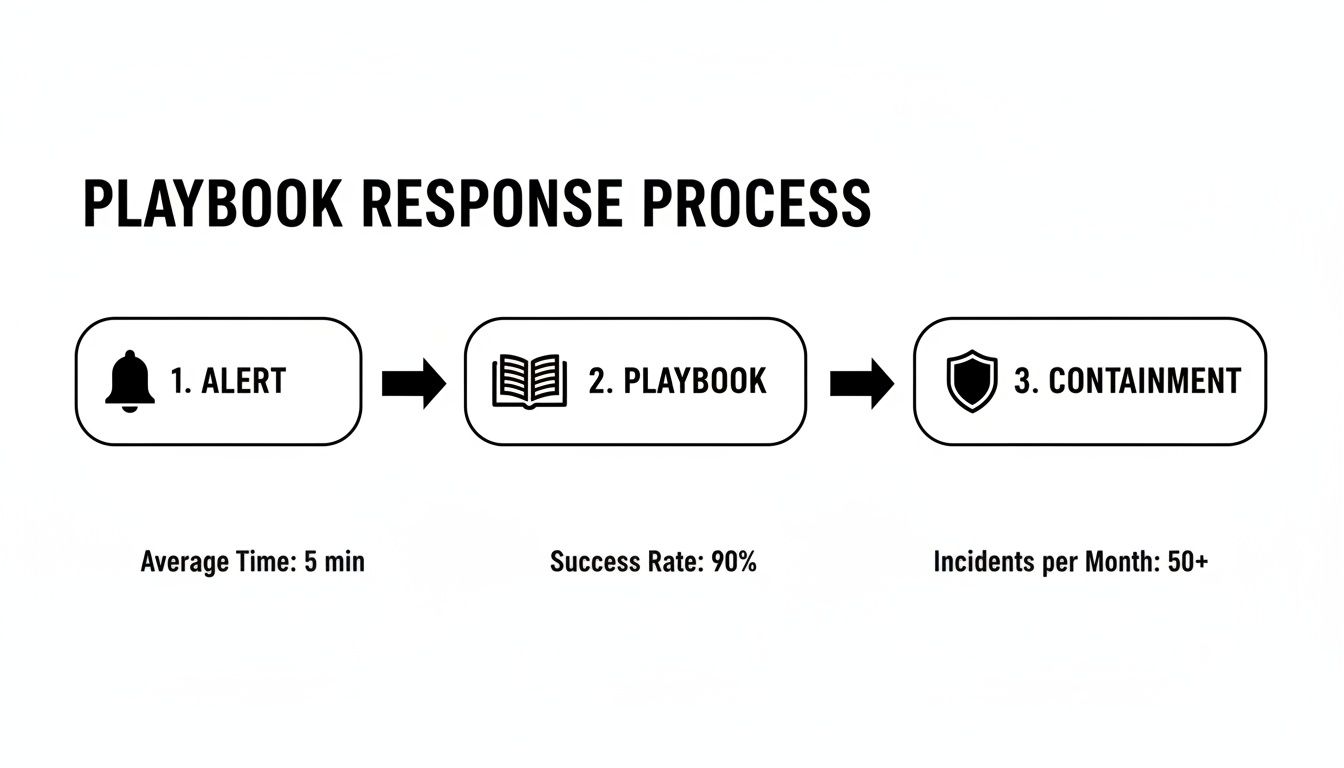
When a crisis hits, chaos is your worst enemy. Without a clear plan, teams panic, people make mistakes, and precious time is vaporized. An Incident Response Plan (IRP) is your playbook, telling your team exactly what to do, who to call, and which steps to take during a security incident or IT failure.
It’s like a fire drill for your digital assets. A well-practiced IRP transforms a frantic, disorganized reaction into a swift, coordinated response because everyone knows their role.
An IRP is more than a document—it's muscle memory for your entire organization. By defining roles and standardizing procedures, you remove the guesswork and hesitation that inflates your MTTR.
This plan can't just collect dust on a shelf. It needs to be a living document that you test and update regularly. The goal is to make the response process so familiar that it becomes second nature.
Leverage Automation for Detection and Containment
Humans can only move so fast, but in cybersecurity, speed is everything. Automation gives you a critical edge. Modern security tools can automatically detect and contain many threats far faster than any human ever could.
This is an absolute game-changer for reducing mean time to resolution. For instance, Security Orchestration, Automation, and Response (SOAR) platforms can automate routine tasks like quarantining an infected laptop or blocking a malicious IP address the second it's detected.
This automation frees up your technical team to focus on the more complex parts of the puzzle, like root cause analysis and recovery. To effectively lower your MTTR, you have to find ways to speed up every part of your response. For example, reducing system latency is a critical piece of the puzzle, and there are plenty of proven tips for faster systems that can make a real difference.
Adopt Proactive IT Maintenance
Honestly, the fastest way to resolve an incident is to prevent it from ever happening. A reactive, break-fix approach to IT is a surefire recipe for a high MTTR. Proactive maintenance flips the script—it involves regularly updating systems, patching vulnerabilities, and monitoring performance to catch problems before they cause downtime.
For example, consistent patch management closes the very security gaps attackers love to exploit. At the same time, performance monitoring can spot the tell-tale signs of hardware failure long before a server actually crashes. This preventative mindset is a core principle of effective managed IT services.
It shifts your IT from a cost center that’s always fighting fires to a strategic asset that maintains stability and uptime. This is especially vital for industries like professional services and healthcare, where any disruption can have serious financial and reputational consequences.
Provide Continuous Security Awareness Training
Your employees can be either your weakest security link or your first line of defense. The choice often comes down to training. Phishing attacks, which are behind a massive number of security breaches, succeed by tricking a single, unsuspecting employee.
Ongoing security awareness training teaches your team how to spot and report suspicious activity. When an employee in your Tampa office flags a phishing email instead of clicking on it, they’ve stopped an incident before it even began. This drastically reduces the number of incidents your team needs to resolve in the first place, directly improving your security posture and keeping that MTTR nice and low.
Turn Your MTTR into a Competitive Advantage

For business owners in Orlando and across Central Florida, Mean Time to Resolution shouldn’t be just another IT metric gathering dust in a report. Think of it as your company’s pulse. It tells you exactly how resilient and efficient you are when things go wrong, directly impacting your bottom line.
A high MTTR is a hidden vulnerability, a constant drain on your team’s time and your company’s resources. But a low MTTR? That’s a serious competitive advantage.
The secret is ditching the reactive, break-fix mindset for good. Instead of just fixing problems as they pop up, a proactive partnership builds a technology strategy designed for prevention and lightning-fast resolution. This move turns IT from an unpredictable expense into an asset that drives stability and growth.
All the strategies we've covered—from having a 24/7 SOC to a clear incident response plan—aren’t just standalone tactics. They all work together, forming a mature operational strategy that keeps your business running smoothly.
From Hidden Risk to Powerful Asset
This is exactly where Cyber Command’s services make a real, measurable impact on your business. Our entire approach is built to systematically drive your mean time to resolution down by tackling the root causes of delays and inefficiency.
Here’s how our services directly deliver on the strategies that matter:
- 24/7/365 SOC: Our Security Operations Center provides the constant watchfulness needed to slash detection and response times. We neutralize cyber threats before they can cause costly disruptions.
- Proactive Managed IT: We don't wait around for things to break. Through proactive maintenance, patching, and monitoring, we prevent many incidents from ever happening in the first place—the best way to keep your MTTR as low as possible.
- Transparent Reporting: We believe in results you can see. Our business-focused reports show you exactly how your MTTR is improving, giving you predictable costs and a clear return on your investment.
For professional service firms and medical practices across Central Florida, this isn't just about managing tickets; it's about managing risk. A low MTTR means protected client data, uninterrupted service delivery, and solid business continuity—the very foundation of trust and profitability.
The goal is to stop firefighting and start building. When you partner with Cyber Command, you get a technology roadmap that’s fully aligned with your business goals. We handle the uptime, security, and accountability so you can focus on growth.
Ready to turn your MTTR from a vulnerability into your next competitive advantage? Contact Cyber Command today to schedule a consultation. Let’s build a technology strategy that delivers predictable costs, clear communication, and measurable results for your Orlando or North Texas business.
Your MTTR Questions, Answered
Here are a few of the most common questions we get from business owners across Central Florida about Mean Time to Resolution.
Does a Low MTTR Really Impact My Small Business Bottom Line?
You better believe it. For any small business in cities like Orlando or Tampa, every single minute of downtime is a direct hit to your wallet. It's lost revenue, stalled productivity, and a potential black eye on your reputation. A low mean time to resolution isn't just a tech metric; it's about getting your business back on its feet faster to stop the bleeding.
Think about a professional services firm—like a law or accounting practice. Faster resolution isn't just about convenience; it’s about maintaining client service, protecting incredibly sensitive data from cyber security threats, and upholding the trust you've worked so hard to build. That’s how you protect your competitive edge.
Can I Improve MTTR Without a Dedicated IT Department?
Yes, and honestly, this is where partnering with a managed IT services provider becomes a game-changer. Many small and mid-sized businesses, especially privately owned medical practices or law firms in Florida, simply don't have the resources for a deep in-house IT bench. That's okay. Partnering with a provider gives you instant access to a 24/7 Security Operations Center (SOC) and an expert helpdesk.
This co-managed or fully managed model delivers the tools, processes, and people you need to dramatically reduce your MTTR—all without the massive overhead and expense of building a full internal team from scratch.
How Often Should My Business Report On MTTR?
While you should be tracking MTTR constantly behind the scenes, formal reporting on a monthly or quarterly basis is usually the sweet spot. This rhythm is frequent enough to let you spot trends, see the real-world impact of new strategies like cybersecurity awareness training, and catch recurring issues that might point to a bigger, underlying problem.
This approach keeps everyone in the loop and provides a consistent, data-driven look at how your IT and security posture is improving. It's about making sure your technology is actively supporting your business goals, not holding them back.
Ready to transform your mean time to resolution from a hidden risk into a powerful business asset? The team at Cyber Command, LLC provides the proactive partnership and 24/7 support needed to keep your Central Florida business secure and resilient. Schedule your consultation today.