HIPAA Compliance Experts: Your 2026 Hiring Guide
You own a small practice. You already wear too many hats. In a single week, you might review payroll, approve a software invoice, answer a patient complaint, and decide whether an old laptop should stay in service one more year.
Then someone asks a simple question: “Are we HIPAA compliant?”
For many owners in Orlando, Winter Springs, Plano, and the rest of North Texas, that question lands hard because the actual issue isn’t paperwork. It’s whether your practice can keep operating after a security incident, an audit request, or a vendor mistake. That’s why hiring hipaa compliance experts matters. Not as a box to check, but as a way to reduce chaos, assign responsibility, and turn compliance into a managed process instead of a recurring fire drill.
Why Hiring HIPAA Compliance Experts is a Survival Skill
A dentist in Orlando doesn’t usually wake up thinking about OCR investigations. They think about schedule gaps, insurance reimbursements, and whether the practice management system will stay up all day. Then an employee clicks the wrong email, a shared login gets abused, or a patient asks for records and the office realizes nobody is sure what the response process is.
That’s when HIPAA stops feeling theoretical.

The risk is real, and it isn’t limited to large hospital systems. HIPAA violation trends show escalating enforcement. In 2020, the OCR imposed a record $13.5 million in fines amid thousands of investigations. By August 2025, nearly 400 breaches had already impacted 30 million individuals, and cumulative penalties since 2003 exceeded $161 million. For small practices, fines can range from $141 to $2.1 million annually depending on severity, according to HIPAA enforcement and breach statistics compiled by Compliancy Group.
Small practices feel this differently than enterprise organizations do. A large system may absorb disruption with internal counsel, an IT department, and a compliance office. A private dental office, med spa, veterinary clinic, or specialty physician group usually can’t. If the owner is also the final decision-maker for software, vendors, staffing, and finance, a breach becomes a business continuity problem immediately.
Compliance and cybersecurity are now the same operational conversation
Most owners still separate “HIPAA” from “cybersecurity.” In practice, that split causes trouble. If your team uses weak access controls, shares accounts, stores files in the wrong place, or can’t tell whether a vendor touches protected data, you don’t have a compliance issue on one side and a security issue on the other. You have one operational risk with two consequences: exposure and enforcement.
Practical rule: If a control protects patient data, it belongs in both your security plan and your compliance program.
That’s why a good expert doesn’t hand you a binder and disappear. They help you identify where patient data lives, who can access it, which vendors touch it, how your team is trained, and what happens after hours if something looks wrong.
If you want a simple way to sanity-check your starting point, a comprehensive HIPAA compliance checklist can help you spot obvious gaps before you start interviewing vendors.
What survival actually looks like
For a small practice or professional office, survival means four things:
- You know your risks: Not in broad terms, but system by system and workflow by workflow.
- Your staff knows what to do: Especially front desk, billing, and support roles that handle sensitive data every day.
- Your vendors are controlled: Cloud software, billing firms, answering services, and IT tools all create exposure if nobody owns the relationship.
- You can respond fast: Nights, weekends, and holidays count too.
That’s the value of hipaa compliance experts. They reduce uncertainty. And for small organizations, uncertainty is usually the most expensive part.
What a HIPAA Compliance Expert Actually Does
The phrase “HIPAA expert” gets thrown around so often that it stops meaning much. For a small practice, the better question is this: what work should this person or firm perform that lowers your risk and makes your operation easier to manage?
The job is broader than policy writing and narrower than magic. Good experts build a repeatable compliance system around your real workflow, your software stack, and your staff behavior.
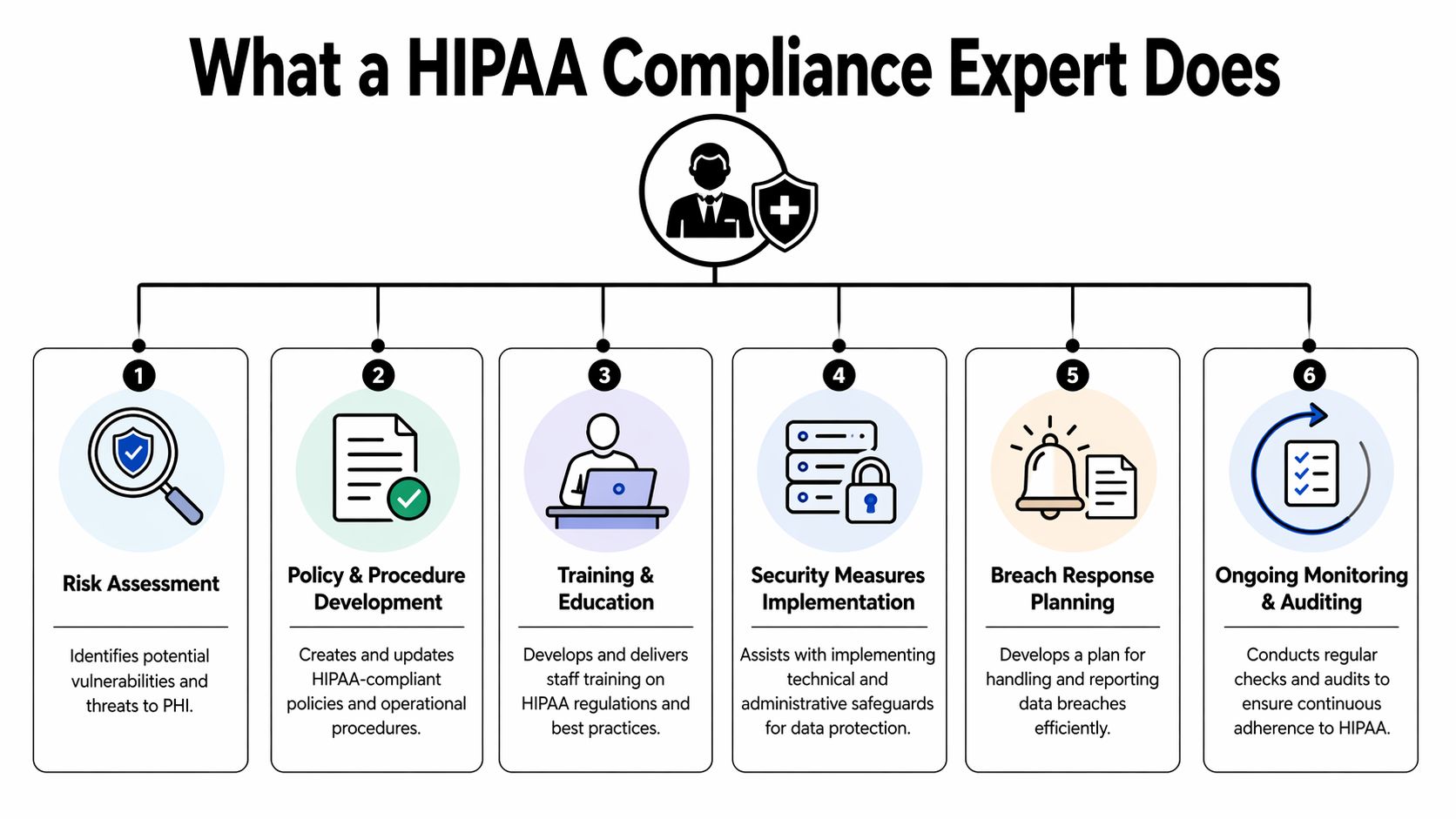
They start with risk analysis
If a vendor can’t explain how they conduct and update a formal risk analysis, you’re not talking to a serious compliance partner. The Office for Civil Rights has consistently identified failure to conduct a proper risk analysis as a top HIPAA violation, most entities in the 2016-2017 audits failed this requirement, and in 2024 OCR launched a dedicated enforcement initiative targeting this provision, as noted in HIPAA violation case analysis from HIPAA Journal.
That matters because many firms still sell “assessments” that are really short questionnaires. A real risk analysis looks at where protected health information is created, stored, transmitted, and accessed. It examines workstations, cloud systems, remote access, email workflows, user permissions, vendor dependencies, and physical handling of records or devices.
A real expert should also show you how the output turns into action. If the report says laptops need stronger safeguards or user access is too broad, there should be an owner, a priority, and a timeline.
They help assign real internal accountability
A lot of practices assume an outside expert can “be HIPAA” for them. That isn’t how this works. An external partner can guide, document, monitor, and support. But someone inside the organization still needs authority to make decisions, approve changes, and hold people accountable.
If you’re unclear on what that internal ownership should look like, the HIPAA Privacy Officer role is a useful reference point because it clarifies responsibilities that many small practices leave vague.
The best outside partner strengthens internal ownership. They don’t replace it.
That also applies beyond healthcare. Law firms, accounting firms, and architecture practices may not all be covered entities in the same way, but they still handle sensitive data, rely on vendors, and need a named decision-maker for privacy and security issues.
They connect policy to operations
Most failed compliance programs have documents. What they don’t have is follow-through.
An expert should help with:
- Policy and procedure development: Documents should match how your office operates, not how a template assumes it operates.
- Business associate oversight: If a vendor handles protected data, someone needs to review that relationship, confirm obligations, and track agreements.
- Technical safeguard alignment: Access controls, endpoint protection, patching, encryption choices, and monitoring must support the policy set.
- Audit readiness: Your evidence has to be organized before anyone asks for it.
For organizations that need to tie HIPAA work into a broader governance effort, compliance mapping across business frameworks helps clarify how overlapping obligations affect operations.
They stay involved after the assessment
Many one-time consultants often fall short. They identify problems, deliver a report, and leave the practice owner holding a list of unresolved issues. That model can create awareness, but awareness alone doesn’t harden systems or train employees.
A stronger partner usually provides ongoing monitoring, recurring reviews, incident support, and evidence management. They revisit the environment after changes such as a new EHR module, a new location, a vendor switch, or a major staffing shift.
In short, hipaa compliance experts should do more than explain the rules. They should turn those rules into routines your office can sustain.
How to Identify and Vet True HIPAA Experts
Not every IT company that says “we do HIPAA” knows how to support a small practice. Some are good at infrastructure but weak on policy. Some are strong on paperwork but can’t guide a real incident. Some know hospital environments but don’t understand a five-provider dental group, a veterinary clinic, or a law office without internal IT staff.
You need a vetting process that exposes those gaps before you sign.
Start with fit, not branding
Begin with firms that understand your size and operating model. A practice with one office manager, rotating support staff, outsourced billing, and a handful of cloud apps needs a different partner than a regional health system.
Local relevance matters too. In Central Florida and North Texas, owners often need someone who can talk plainly, coordinate with existing vendors, and support a mix of older systems and newer cloud platforms without turning every project into a consulting engagement.
A practical shortlist usually comes from three places:
- Peer referrals: Ask owners of similar practices who they trust and why.
- Industry adjacency: Your EHR reseller, legal counsel, or insurance advisor may know who’s credible and who creates cleanup work.
- Technical depth checks: Review whether the firm discusses risk analysis, incident response, vendor oversight, and training with any specificity.
Training is a non-negotiable test
One of the easiest ways to spot weak vendors is to ask how they train staff. If the answer is “we do annual HIPAA training” and nothing else, keep looking.
Human error accounts for over 80% of HIPAA breaches, and 54% of healthcare organizations identify staff education as the most effective mitigation strategy, according to research on HIPAA breaches and training effectiveness available through PubMed Central. Support staff are often the highest-risk group, which means front-desk workflows, scheduling, billing, intake, and records handling deserve more attention than generic slide decks usually provide.
A serious expert should describe role-specific training, documented completion, follow-up for missed sessions, and some way to check whether people understood the material.
If a vendor treats training like a yearly formality, they’re telling you exactly how they’ll handle the rest of your compliance program.
Use a simple scorecard
Don’t rely on chemistry alone. Use a written scorecard and force each vendor into clear pass or fail decisions.
| Vetting Criteria | What to Look For | Pass/Fail |
|---|---|---|
| Industry fit | Experience with practices similar to yours, such as dental, veterinary, specialty medical, or professional services | |
| Risk analysis method | A documented process that goes beyond a checklist and leads to remediation actions | |
| Training approach | Role-specific staff education, documentation, and follow-up for support staff and new hires | |
| Incident response readiness | Clear after-hours process, named roles, and evidence preservation steps | |
| Vendor management | Ability to identify vendors touching sensitive data and organize agreement tracking | |
| Policy practicality | Policies tailored to your workflow instead of generic templates | |
| Technical competence | Ability to explain access controls, endpoint safeguards, patching, and monitoring in plain language | |
| Ongoing support model | Recurring reviews, support after onboarding, and a defined cadence for updates | |
| Reporting quality | Clear action plans, ownership, due dates, and executive-level summaries | |
| Communication style | Direct answers, no jargon fog, and willingness to explain trade-offs |
Watch for the common failure patterns
Weak vendors often reveal themselves in the sales process. Look for these signals:
- Template dependence: They talk about documents more than workflows.
- No operating detail: They can define HIPAA terms but can’t explain what happens during a Saturday night incident.
- Overpromising: They imply they can “make you compliant” without discussing your staff responsibilities.
- No remediation discipline: They find issues but have no process for closing them.
- Hospital bias: Their examples and service model assume a much larger organization than yours.
Ask for proof without demanding fairy tales
You may not get named case studies, and that’s fine. You can still ask for evidence. Request redacted samples of risk registers, policy review workflows, incident runbooks, or training records. Ask how they coordinate with office managers, practice administrators, and outside software vendors.
The right partner won’t hide behind buzzwords. They’ll show you how work gets done, who does it, and what happens when something goes wrong.
Questions That Reveal a Vendor's True Capabilities
By the time you’re interviewing finalists, most of them will sound competent. They’ll all say they understand HIPAA. They’ll all mention cybersecurity. They’ll all tell you they’re responsive.
That’s why the interview has to move from claims to operating detail.

A 2025 HIPAA Journal survey on compliance maturity found that many organizations still lack a dedicated HIPAA Privacy Officer with real authority, and many provide training less than annually. That tells you where to press. Ask vendors how they address those maturity gaps in small organizations where the owner, office manager, and outside IT provider all share pieces of responsibility.
Ask questions that force process answers
These questions work because weak vendors answer them vaguely.
Walk me through your exact process if we suspect a breach at 10 PM on a Saturday.
A strong answer includes alerting, triage, containment, evidence preservation, decision authority, and communication steps. A weak answer leans on “we’ll assess the situation” and never gets specific.How do you help us assign internal authority for privacy and security decisions?
Strong vendors explain roles, escalation paths, and who owns approvals. Weak ones act as if outsourcing removes the need for internal accountability.How do you tailor training for front desk, billing, providers, and managers?
Good answers mention job function, practical examples, retraining, and documentation. Bad answers reduce everything to annual compliance content.How do you review our vendors that touch sensitive information?
Strong answers include inventorying vendors, reviewing contracts or agreements, documenting risk, and escalating issues. Weak answers say vendor compliance is “mostly on the vendor.”
A capable partner can describe actions in order. A sales-led vendor stays abstract.
Ask how they mature a small practice over time
One of the best questions is simple: What will our program look like in six to twelve months if this engagement goes well?
A real expert should talk about maturity, not just deliverables. They should describe what gets standardized, what gets documented, what gets reviewed regularly, and what your staff will be doing differently. They should also acknowledge the trade-offs. Small practices can’t do everything at once. Good partners know how to prioritize.
If you want a broader framework for evaluating service providers before you sign, these questions to ask before hiring managed IT services are useful because they expose response discipline, ownership, and accountability.
Listen for honesty about limitations
Trust is built through such transparency. Strong vendors will tell you where they need cooperation from your office, where another specialist may be needed, and what they won’t promise. That’s a good sign.
Weak vendors usually do one of two things. They either overstate what they can solve alone, or they dodge specifics by saying every situation is unique. Of course every environment is unique. That’s not an answer.
The right interview questions don’t just test knowledge. They test whether the vendor has a real operating model.
Budgeting for Compliance in Orlando and North Texas
Most owners don’t need a lecture on why security matters. They need to know what this will cost, what model makes sense, and whether the spend will stay predictable.
That’s where the market gets messy. Small practices often talk to two very different kinds of vendors. One offers one-time consulting, usually centered on an assessment and a packet of documents. The other offers an ongoing service model that combines compliance work with operational security support.
For small private practices, that distinction matters a lot. According to analysis of HIPAA consulting options for smaller organizations, 60% cite limited expertise as their top barrier, many consultants are geared toward large hospitals, and outsourced compliance-as-a-service on a flat-rate model can cut breach risk by 40% more than one-off consulting projects.
What you’re really paying for
You’re not just paying for forms, meetings, or a risk assessment. You’re paying for continuity and follow-through.
A one-time consultant may be the right fit if you already have internal IT, someone accountable for compliance, and the discipline to manage remediation yourself. Many small offices don’t. In those environments, a flat-rate or recurring support model usually makes more sense because the work doesn’t stop after the report is delivered.
The practical cost drivers are usually:
- Environment complexity: Number of users, devices, offices, and software platforms
- Vendor sprawl: Billing firms, cloud systems, phone vendors, scanning tools, and remote support providers
- Support expectations: Whether you need periodic guidance or active ongoing security involvement
- Documentation maturity: Clean environments cost less to govern than messy ones
Why predictable pricing matters more in smaller markets
In Orlando and North Texas, many practices operate with tight administrative teams. They don’t want surprise project bills every time a vendor changes, an employee leaves, or a risk review uncovers work that should have been done months ago.
That’s why many owners prefer providers that bundle recurring support into a steady monthly structure. It’s easier to budget, easier to manage, and less likely to leave known issues unresolved because nobody approved another statement of work.
If you’re comparing managed support options in Central Florida, this overview of why businesses need managed IT support in Orlando is a useful way to think about predictable service models beyond break-fix support.
Cheap compliance usually becomes expensive remediation.
The right budget decision isn’t the lowest line item. It’s the model that your office can sustain.
Your First 90 Days with a HIPAA Compliance Partner
A good engagement should feel calmer by the end of the first few weeks, not more confusing. You should see structure show up quickly. Not perfection, but structure.
Days 1 through 30
The first month should focus on discovery and clarity. Your new partner should inventory systems, map where sensitive information lives, review user access, identify key vendors, and collect the policies and agreements you already have.
Expect a lot of questions. That’s a good sign. The fastest way to fail an engagement is for the vendor to assume they already understand your workflow.
You should also expect a clear list of immediate risks. Not ten pages of theory. A practical set of issues with priorities, owners, and next actions.
Days 31 through 60
This period should move from findings to remediation. Access issues get tightened. outdated processes get rewritten. Staff training gets scheduled. Vendor relationships that touch sensitive information get reviewed and organized.
This is also when a strong partner starts separating “important” from “urgent.” Small practices can’t fix everything at once, so sequencing matters. The point is to reduce meaningful risk fast while building habits your team can maintain.
Progress in the first 90 days should be visible in calendars, task lists, approvals, and staff behavior. Not just in documents.
Days 61 through 90
By the end of the third month, you should be operating from a new baseline. Staff should know who to contact with questions. Leadership should know what remains open. Evidence should be easier to find. Your partner should have a recurring review rhythm in place so compliance doesn’t drift.
For a law firm or small medical practice, this is usually the moment where the mental load drops. You’re no longer wondering whether anything is being managed. You can see the process, the owners, the cadence, and the gaps that still need work.
That’s what a useful compliance partnership changes. It replaces uncertainty with accountability.
If your practice in Central Florida or North Texas needs a partner that can combine managed IT, cybersecurity operations, and ongoing compliance support without forcing you into reactive project work, Cyber Command, LLC is built for that role. The team supports organizations that need predictable pricing, live U.S.-based helpdesk coverage, 24/7 SOC support, and practical guidance that fits real business operations, not enterprise theory.

