Cloud Based Backup Solutions Small Business Guide 2026
If you're running a medical practice in Winter Springs, a law firm in downtown Orlando, or an accounting office with staff spread across Central Florida, your backup problem probably isn't theoretical. It's immediate. You already know your files matter. What most business owners don't know is whether their current setup would let them recover after a ransomware event, a server failure, or a week where the office is inaccessible.
That's where a lot of "cloud backup" advice falls apart. Many providers sell storage and call it backup. Many small businesses buy a tool and assume they're covered. Then a restore is needed, versions are missing, retention wasn't configured correctly, or nobody knows how long recovery will take. At that point, the monthly subscription you paid for doesn't matter. Recovery does.
For Central Florida businesses, especially in regulated industries, cloud based backup solutions small business plans have to do more than hold copies of files. They need to support continuity, security, compliance, and fast decision-making during a bad day. The right system protects data. The right strategy protects the business.
What Cloud Backup Really Means for Your Business
A real cloud backup system is a digital vault outside your office. If your building has a power issue, hardware failure, water intrusion, or a security incident, the backup copy still exists somewhere separate and recoverable.
That sounds obvious, but many businesses still confuse backup with sync or storage. Dropbox, OneDrive, and Google Drive are useful collaboration tools. They are not, by themselves, a complete business continuity plan. If a file is deleted, overwritten, corrupted, or encrypted by ransomware, those changes can sync too.

Backup protects recovery, not just storage
The question isn't "Where are my files stored?"
The question is "How fast can I get the right version back, and how much work will I lose?"
A Winter Springs dental office is a good example. If the practice management workstation crashes at 4:30 p.m. and the latest usable backup is from the night before, the office may lose a full day's scheduling changes, intake updates, and billing activity. If the same office has a modern backup platform capturing changes continuously, the data loss window is much smaller.
That leads to the two terms owners need to understand:
- RPO
means how much data you can afford to lose. If your RPO is one day, you could lose everything created since the previous backup. - RTO
means how long you can afford to stay down. If your RTO is many hours, your team may sit idle while systems are restored.
Why RPO and RTO matter more than marketing features
Most backup sales pages talk about storage limits, dashboards, and "military-grade security." That's not what matters during an outage. What matters is whether your backup design matches how your business operates.
Practical rule: If your staff updates records all day, nightly backup alone is usually too blunt an instrument.
Modern platforms that use Continuous Data Protection capture file changes in near real time instead of waiting for a nightly job. According to this review of cloud backup for small businesses, providers such as Acronis and IDrive Business demonstrate RPOs under 15 minutes, while scheduled backups can create 24-hour data loss windows. The same analysis notes that block-level differencing and deduplication can reduce storage costs by up to 90% for database-heavy workloads.
What works and what doesn't
In practice, these are the setups that usually work best:
- Good fit for smaller offices
Endpoint and server backup with continuous protection, versioning, and offsite retention. - Good fit for heavier operations
A mix of local recovery plus cloud copy, so large restores don't depend entirely on internet speed. - Weak fit for serious operations
USB drives, a single NAS in the same office, or a sync folder that everyone assumes counts as backup.
A proper backup system should answer four plain questions without hesitation:
- What exactly is being backed up?
- How often are changes captured?
- How long does recovery take for one file, one server, and the whole office?
- Who verifies restores work?
If you can't get clean answers to those four questions, you don't have a backup strategy. You have backup hope.
Why Florida Businesses Need More Than Just Data Storage
Small businesses in Orlando don't operate in a neutral environment. They deal with weather risk, infrastructure interruptions, and a steady stream of cyber threats. That changes what a good backup strategy looks like.
A storage account is passive. A business continuity backup plan is active. It assumes something will eventually go wrong and builds for recovery before that happens.
Your office can be unavailable even when your company isn't
A lot of owners still picture disaster recovery as a worst-case building loss. That's one scenario, but it's not the only one that matters. You can have a functioning business with a non-functioning office.
If your team can't get into the building, if local systems are offline, or if one location goes down while another stays open, staff still need access to current data and a clear restoration path. That's where offsite copies, role-based access, and tested recovery workflows matter more than raw storage space.
For firms with more than one office, or even one office plus remote staff, consistency is often the hidden problem. One branch may have current data, another may not. A restore may be possible for one location but incomplete for another.
Multi-location sync failure is a real operational risk
Generic backup advice usually misses the mark. Distributed businesses don't just need copies; they need reliable replication and version consistency across sites.
A 2025 Gartner finding summarized by Lenovo reported that 47% of SMBs with multiple branches experienced data synchronization failures in their cloud backups. It also found that those failures amplified ransomware impact by 3x because replication was incomplete. The same summary notes that hybrid solutions from Acronis and Veeam use edge caching and WAN optimization, cutting sync times by 40% for remote teams and reducing overall TCO by 30% compared to cloud-only models for distributed organizations.
For a Central Florida business with an Orlando office, a second location, and remote users working from home, that's not abstract. It means a backup plan can look healthy on paper while still leaving gaps in the data your team needs.
A backup that works for one office can fail a multi-location business if the replication design is sloppy.
Florida risk changes the backup conversation
Three local realities push businesses toward stronger backup architecture:
- Weather exposure
Storms, flooding, and building access problems make same-site-only backups risky. - Power and connectivity instability
Even short outages can interrupt backup jobs, corrupt local systems, or delay restores if there's no local recovery option. - Professional services targeting
Law firms, dental offices, accounting firms, and medical practices hold sensitive, operationally critical data that attackers know can't stay down long.
What doesn't work in this environment is the minimalist approach. One copy in the office is fragile. One cloud repository with no restore testing is fragile too. Businesses that need uptime usually end up with layered protection, not a single tool.
Operating from anywhere requires design, not luck
The practical goal is simple. If your office is unavailable, your business should still be able to function in a controlled way. That means staff can access the systems they need, leadership knows what's recoverable first, and the backup environment isn't tangled up with the same failure that hit production.
For Orlando-area firms, the right backup system isn't just a place to park files. It's part of how the business keeps moving when the office, the network, or a user endpoint fails.
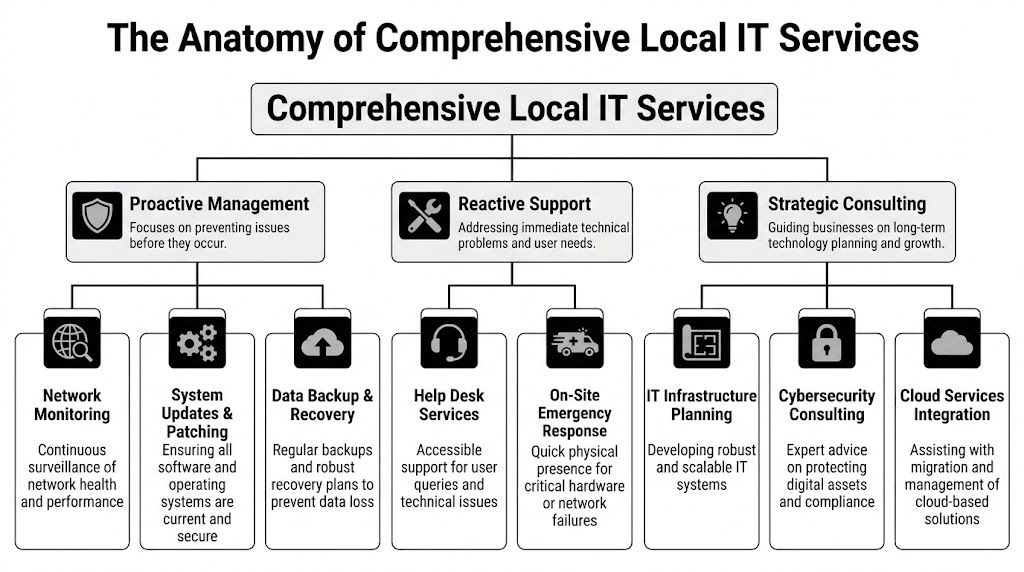
Key Architectures and Components of a Modern Backup Solution
When owners hear "cloud backup," they often picture one thing. In reality, there are several architectures, and each one solves a different problem. Picking the wrong model creates pain later, usually during restore.
Here's the visual map most buyers never get from providers.
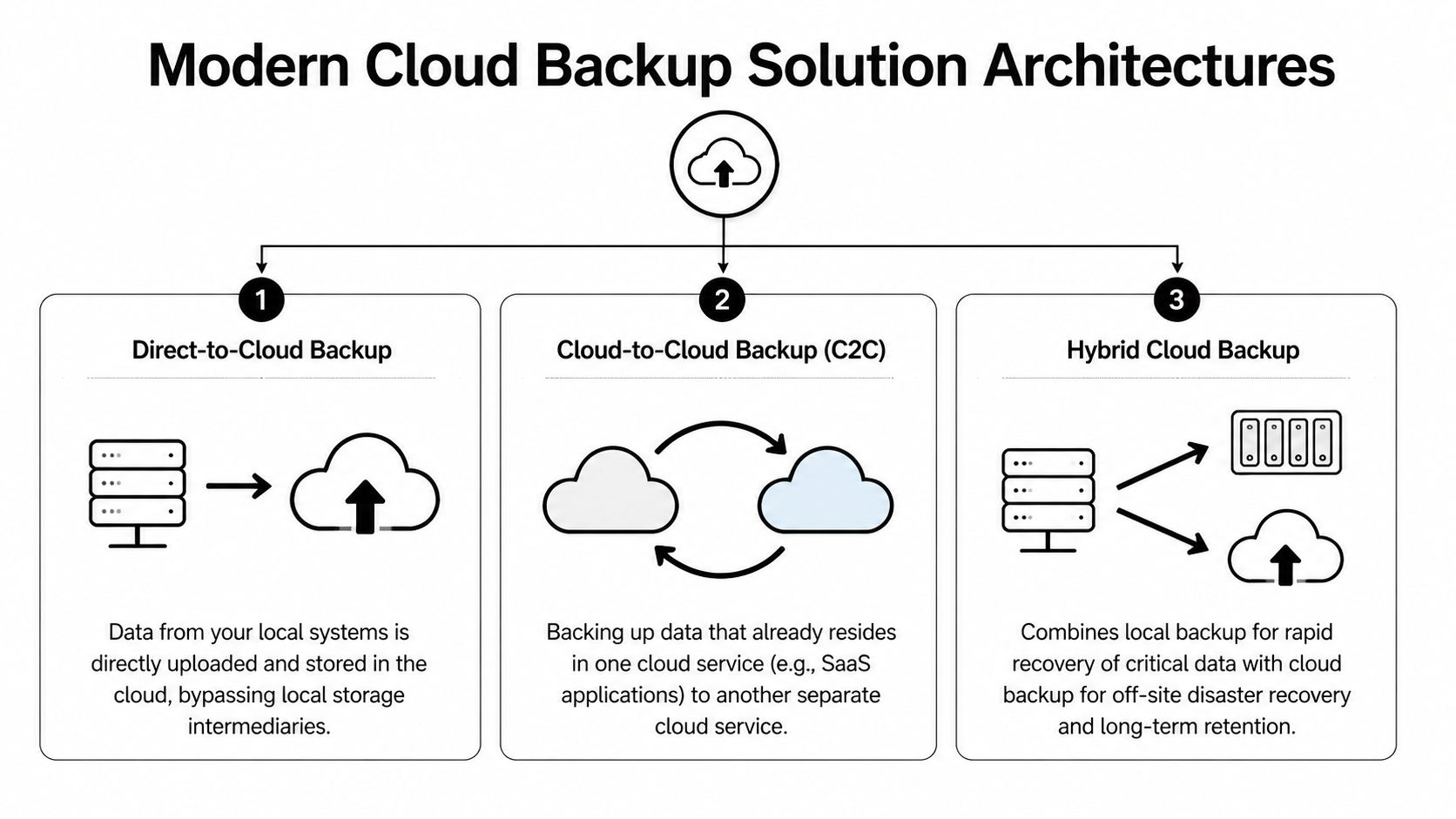
Direct-to-cloud works best when simplicity matters
In a direct-to-cloud model, backup agents on laptops, desktops, and servers send data straight to the provider's cloud repository. This is often a sensible fit for smaller offices without much infrastructure.
Benefits are straightforward:
- Less local hardware
You don't need to maintain a separate backup appliance for basic protection. - Strong fit for remote users
Laptops can keep backing up even when employees aren't in the office. - Cleaner deployment
Endpoint coverage is usually easier to standardize.
The trade-off is recovery speed for large restores. If you need to pull back a full server or a large file set, your internet connection becomes part of the recovery path.
Hybrid is usually the practical answer for serious uptime needs
A hybrid backup design keeps a local backup copy for fast recovery and a cloud copy for offsite disaster recovery. For many small and midsize businesses, this is the architecture that balances speed, resilience, and operational sanity.
If an employee deletes a shared folder, a local recovery target can return it quickly. If the office is compromised, the offsite copy still exists. If ransomware reaches the production environment, a properly isolated backup design gives you a cleaner recovery option.
That local component is often a NAS, backup appliance, or dedicated storage target. The cloud component handles the geographic separation that local-only systems can't provide.
The best architecture usually isn't the one with the most features. It's the one that matches how your business restores.
Cloud-to-cloud fills a gap many firms miss
Many businesses assume Microsoft 365 or another SaaS platform handles backup for them. That's a dangerous assumption. A cloud-to-cloud architecture backs up data that's already in a cloud platform into a separate backup system.
This matters for:
- Exchange and mailbox data
- OneDrive and SharePoint files
- Teams and collaboration content
- Sales and client records in SaaS apps
If your business lives inside Microsoft 365, that data needs a backup strategy of its own. SaaS availability isn't the same as business-controlled retention and point-in-time restore.
The components you should expect to see
A modern backup environment usually includes several moving parts:
| Component | What it does | Why it matters |
|---|---|---|
| Endpoint agent | Captures changes on laptops and desktops | Protects remote users and key workstations |
| Server backup service | Backs up physical or virtual servers | Covers line-of-business systems |
| Local recovery target | Stores a nearby copy for fast restore | Reduces downtime for common incidents |
| Cloud repository | Holds offsite backup data | Protects against site-level disasters |
| Management console | Shows status, failures, retention, and restore options | Lets IT verify protection instead of guessing |
| Recovery testing process | Validates that backups can actually be restored | Turns backup from theory into proof |
For businesses running cloud workloads, it's also worth understanding how infrastructure-level backup fits into the picture. A useful reference is this guide to AWS backup and disaster recovery planning, especially if your applications or data stores already live in the cloud.
What buyers should ask before choosing an architecture
Ask providers to design around your recovery priorities, not their standard package.
- Which systems need rapid local recovery?
- Which users need backup even when offsite?
- Which cloud apps need separate protection?
- What is isolated from production so an attacker can't erase everything at once?
A lot of backup failures start before any attack happens. They start when the architecture was never matched to the business.
Navigating Compliance and Security in Regulated Industries
For regulated businesses, backup isn't just an IT tool. It's part of your compliance posture. A dental office handling patient records, a law firm retaining client documents, or an accounting practice protecting financial data can't treat backup as an afterthought.
The mistake I see most often is buying a general-purpose backup service and assuming compliance will sort itself out. It won't. Providers can offer encryption and storage, but that doesn't automatically produce the safeguards, retention controls, and audit evidence your business may need.

What regulated firms should care about first
If you operate in healthcare, legal, accounting, or financial services, these backup features move from "nice to have" to "required for responsible operations":
- Encryption at rest and in transit
Sensitive records should remain unreadable whether stored or moving across networks. - Immutability
Backup data shouldn't be easy to alter or delete after it's written. - Access control and authentication
Not every employee should be able to browse or remove backup sets. - Audit trails
You need records showing what was backed up, when, and who accessed it. - Retention policy control
Compliance isn't only about making copies. It's also about keeping the right copies for the right amount of time. - Restore verification
If you can't prove recoverability, the backup isn't doing its compliance job.
AES-256 matters because it changes the exposure profile
For regulated businesses, one of the most important baseline controls is AES-256 encryption. According to Box's overview of cloud backup for small business, cloud backup solutions for regulated businesses rely on AES-256 encryption for data at rest and in transit, and it describes that NIST standard as practically unbreakable. The same source notes that leading solutions such as Acronis and CrashPlan encrypt data client-side before upload, which prevents provider access and reduces insider-threat exposure.
That client-side piece matters. If the provider never receives your files in plaintext, you've reduced one category of risk before the data even leaves your environment.
How this maps to real compliance pressures
For Orlando-area regulated firms, the details differ by industry, but the practical requirements look similar.
Medical practices and HIPAA
A medical spa, dentist, orthodontist, or veterinary clinic needs backup controls that protect electronic patient information and support reliable restoration after an incident. Encryption helps protect confidentiality. Access controls limit exposure. Immutable or protected backup copies help when ransomware hits systems that staff use every day.
HIPAA conversations also force a question many small practices avoid. If a patient record must be restored, how quickly can that happen, and who owns that process?
Law firms and accountants under GLBA-style pressure
Law offices and accounting firms hold sensitive financial records, tax data, case files, and communications. Even when the exact regulatory framework varies, the operational expectation is the same. Sensitive client data needs controlled access, secure retention, and documented recovery capability.
A provider saying "we're secure" isn't enough. Ask how deletion is prevented, how restores are logged, and who can access backup data.
Financial and professional services with audit expectations
Firms serving financial clients often need proof, not promises. That means logs, reports, policy enforcement, and recoverability evidence. During a client security review or internal audit, "our backups run every night" is weak. A defensible answer includes encryption method, retention policy, access restrictions, and restore test records.
Security features that actually improve recovery
Security in backup isn't just about confidentiality. It also affects whether recovery works under pressure.
Box's overview also states that in simulated ransomware tests, Acronis's encrypted backups demonstrated a 99.9% data recovery success rate and a 40% faster RTO compared to non-encrypted alternatives. That's useful because it cuts through a common misconception that stronger security always slows recovery. In backup design, the opposite can be true when integrity checking and protected restore paths are built in.
What to reject during vendor review
Be cautious if a provider can't clearly answer these points:
- Where is data stored
If they can't explain data residency and control, keep pushing. - How are backups protected from deletion
If the answer is vague, assume the design is weak. - Can they support regulated documentation
Agreements, logs, and compliance-oriented reporting shouldn't be optional extras. - How often are restores tested
Marketing language is easy. Restore evidence is harder, and that's what matters.
The safest approach for regulated small businesses is usually not the cheapest subscription on a website. It's a backup design built for security controls, operational recovery, and auditability from the start.
Choosing Your Cloud Backup Strategy DIY versus Managed
Some business owners want direct control. Others want clear accountability. Both instincts are reasonable. The real question is whether your team has the time and skill to build, monitor, test, and document backup properly.
DIY can work. It often works poorly when backup is one of fifteen responsibilities assigned to an office manager, internal admin, or busy IT generalist. The software may be installed, but alerting, retention, restore testing, and access control drift over time.
Where DIY usually breaks down
The problem isn't buying the tool. The problem is everything after purchase.
A small business has to make dozens of decisions that marketing pages tend to skip:
- What gets backed up, and what gets excluded
- How retention should differ for servers, endpoints, and SaaS data
- Which backup copies are protected against deletion
- How often restore tests should happen
- Who reviews failed jobs and who fixes them
- How compliance evidence gets documented
If you're still comparing local hardware and offsite options, this plain-language piece on understanding your data storage choices is a useful companion before you commit to a model.
DIY vs Managed Cloud Backup Comparison
| Factor | DIY (Do-It-Yourself) | Managed Service (e.g., Cyber Command) |
|---|---|---|
| Ownership | Your team owns setup, monitoring, policy decisions, and restores | A service partner owns day-to-day management and escalation |
| Internal time | Staff must review alerts, fix failed jobs, and document results | Internal staff spends less time on backup administration |
| Skill requirement | Requires backup, security, and recovery expertise | Lets non-specialist teams rely on experienced operators |
| Compliance support | You must map retention, logging, and controls yourself | Managed oversight usually makes audit preparation more structured |
| Disaster accountability | Recovery depends on whoever is available and qualified | Responsibility is clearer during an incident |
| Hidden costs | Missed alerts, weak testing, and rushed recovery create expensive risk | Monthly cost is higher on paper but often lowers operational risk |
| Fit | Works best for firms with capable in-house IT and time to spare | Works best for firms that need predictable outcomes |
Managed service is about risk transfer, not convenience alone
The strongest argument for managed backup isn't that it's easier. It's that someone is watching the system when you aren't.
That matters when:
- backups fail unnoticed,
- a retention policy is misconfigured,
- ransomware starts touching unusual data patterns,
- or a restore has to happen outside business hours.
For many small businesses, especially regulated ones, the better question isn't "Can we run this ourselves?" It's "Do we want recovery to depend on improvisation?"
A managed approach also fits well when backup is tied to broader continuity planning. If you're comparing service models, this overview of managed disaster recovery as a service helps frame the discussion beyond just storage and backup licensing.
If nobody is responsible for testing restores, nobody is responsible for recovery.
A direct recommendation
Choose DIY only if you already have disciplined internal IT ownership, documented procedures, and a real testing cadence. Don't choose it just because the monthly line item looks smaller.
Choose managed when uptime, compliance, and accountability matter more than the feeling of direct control. For most Orlando-area medical, legal, financial, and professional services firms, that's the safer business decision.
A Practical Checklist for Selecting Your Solution
Vendor demos are polished. Backup failures are messy. The easiest way to cut through sales language is to ask direct questions and keep asking until you get specific answers.
Questions that reveal whether the provider is serious
Bring this checklist into every evaluation call.
- What are our recovery targets
Ask for your expected RTO and RPO by workload, not a generic platform statement. - What exactly gets backed up
Endpoints, servers, virtual machines, Microsoft 365, shared folders, databases, line-of-business apps. - How is backup data protected from deletion or tampering
You're looking for clear language around immutability, isolation, and protected administrative access. - How are restores tested
Ask whether they perform regular test restores and whether they document results. - How do you handle failed backup jobs
A mature provider has an escalation process, not just automated emails no one reads. - Where is the data stored
You need a clear answer on hosting location and control. - What compliance documentation can you support
For regulated businesses, ask about agreements, audit logs, retention records, and reporting. - Who has access to backup data
Administrative scope should be controlled and auditable. - How are remote users protected
Staff working from home or traveling shouldn't fall outside the backup plan. - What is the restore process during ransomware
Ask them to walk through the steps in plain English.
Questions many buyers forget to ask
These often uncover the biggest gaps:
- If our office is unavailable, how do we access restored data?
- If one server fails, what comes back first?
- If one employee deletes a folder, can we restore only that folder?
- If a backup fails overnight, who notices before our staff logs in?
- If we leave your service, how do we retrieve our backup data?
Ask every provider to describe the last restore problem they had to solve and how they handled it. The quality of that answer tells you more than the product demo.
Red flags during selection
Watch for these responses:
- "Unlimited" with no retention clarity
Unlimited storage doesn't mean unlimited recoverability. - Vague compliance language
If they speak in generalities, assume you will do the hard compliance work yourself. - No restore evidence
If they can't show testing discipline, don't assume they have it. - One-size-fits-all packaging
Dental practice, law office, and architecture firm backups should not all be designed the same way.
The right provider should make backup feel less mysterious, not more.
Putting Your Backup Plan into Action
Good backup projects don't start with software. They start with recovery priorities. Identify what must come back first, what can wait, and which systems create the biggest operational risk if they're unavailable.
Then deploy in a practical order. Install agents on endpoints and servers. Configure retention and access policies. Run the initial full backup. Add cloud app coverage if your business depends on Microsoft 365 or similar services. Document the restore path for the systems your team uses every day.
After that, testing becomes the definitive dividing line.
A backup that has never been restored is an assumption. A backup that is restored and verified on a schedule becomes part of business operations. That includes single-file restores, server-level recovery, and scenario testing for ransomware or office outage conditions. If your team doesn't already have a documented process, start with a structured disaster recovery plan template and build backup decisions around that plan, not the other way around.
Most small businesses don't fail because they ignored backup entirely. They fail because they assumed setup was the finish line. It isn't. The finish line is verified recovery.
If your business in Orlando, Winter Springs, or the surrounding Central Florida area needs a backup strategy that covers cybersecurity risk, compliance, and real-world recovery, Cyber Command, LLC can help you design, manage, and test a solution that fits how your business operates. Their team supports regulated firms, multi-location organizations, and small businesses that need more than basic storage. They focus on recoverability, accountability, and ongoing protection so you can spend less time worrying about backups and more time running the business.