Your Guide to Firewalls for Businesses in Florida
Think of a firewall as the most important security guard you'll ever hire for your business. It stands at the digital entrance to your network, acting as a critical security checkpoint for all your traffic. Its one job is to block malicious threats while waving legitimate data through.
This isn't just an IT add-on; it's your first and most vital line of defense, protecting everything from sensitive client files and financial records to your company's intellectual property.
Why Your Business Needs a Firewall Explained
Imagine your business network is a secure vault in a downtown Orlando bank. The firewall is the head of security posted at the main entrance, meticulously checking the credentials of everyone and everything trying to get in or out.
This is especially true for professional services firms—law offices, medical practices, and financial advisors—across Central Florida, from Tampa to Orlando to Kissimmee. You're prime targets for cybercriminals because of the high-value client data you handle. A breach isn't just a technical glitch; it's a direct path to devastating financial loss, crippling regulatory fines, and a damaged reputation that can take years to rebuild. For legal practices, a single breach could expose confidential case files, leading to disbarment and malpractice suits. For healthcare providers, it means violating HIPAA and facing million-dollar penalties.
The Core Function of a Business Firewall
A firewall works on a simple but incredibly powerful principle: it enforces a set of security rules to filter every bit of data that crosses its path. Think of it as a bouncer with an iron-clad guest list for your network.
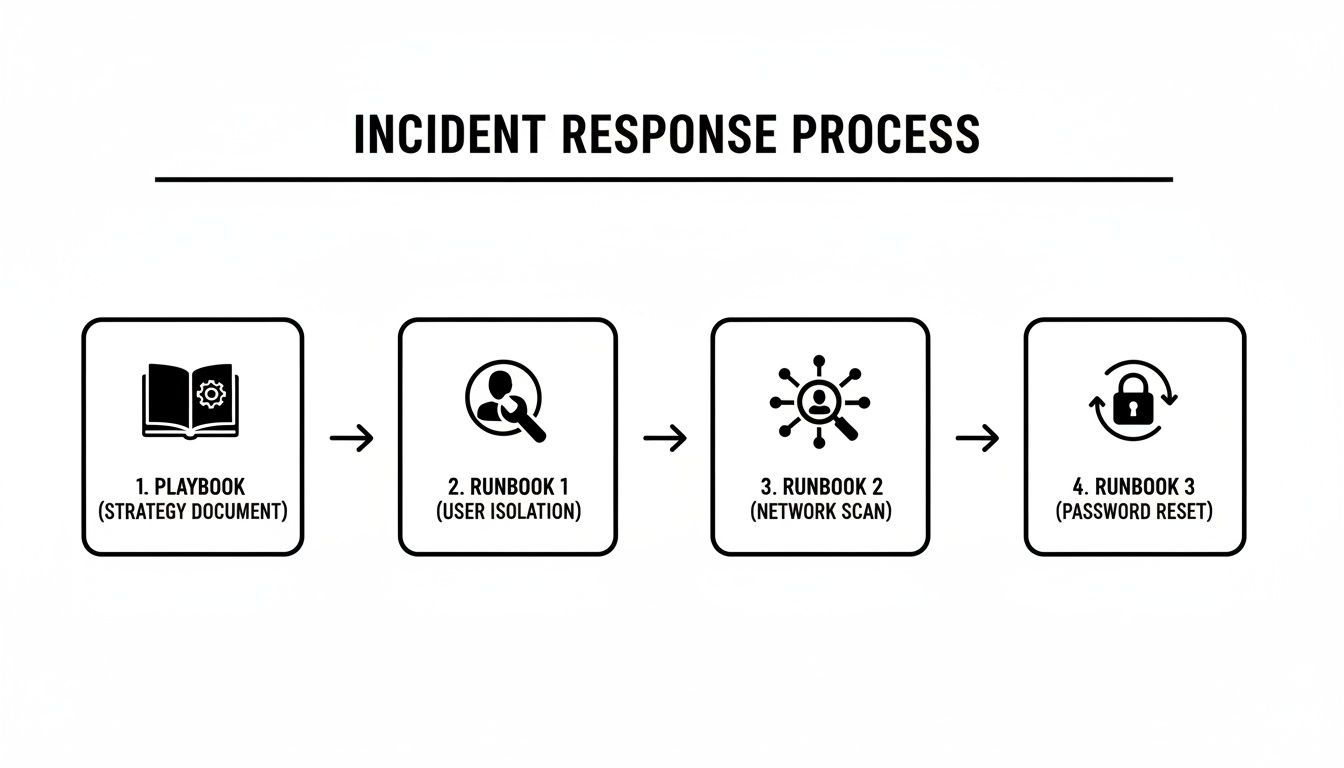
To give you a clearer picture, here's a quick summary of what a firewall does for you.
At-a-Glance Firewall Protection for Your Business
This table summarizes the core protective functions a properly configured firewall provides for a typical Central Florida business.
| Core Security Function | How It Protects Your Business |
|---|---|
| Blocking Malicious Traffic | Identifies and stops known threats like malware, ransomware, and brute-force attacks before they can breach your network. |
| Controlling Access | Ensures only authorized users and approved applications can access specific network areas, stopping internal threats and data leaks. |
| Monitoring and Logging | Keeps a detailed record of all network traffic, which is crucial for security audits, compliance, and analyzing potential threats. |
These functions work together to create a formidable barrier against a wide array of digital threats.
From Digital Sentry to Business Necessity
Without a firewall, your business network is an open door. Every single device connected to the internet—from the front desk computer in your Tampa office to the server holding patient records in Orlando—is exposed to a constant barrage of automated attacks from around the globe.
Threat intelligence shows that ransomware groups are actively hunting for and exploiting firewall vulnerabilities, sometimes launching attacks before a patch is even publicly available. The recent takedown of the LockBit ransomware gang, which extorted over $120 million from victims, revealed how they systematically targeted businesses with weak or misconfigured network defenses.
This is precisely why defense-in-depth is essential—layered security controls provide protection when any single control fails. Rapid patching remains foundational, but a strong defense ensures organizations are not left defenseless during the critical window between an exploit and a patch.
For any business owner, the takeaway is clear: a professionally configured firewall is the absolute bedrock of your cybersecurity posture. It's the starting point for building broader, layered defenses and comprehensive network security strategies for small businesses. This proactive stance is no longer optional; it's a core requirement for protecting your assets and ensuring your business can operate safely.
Choosing the Right Firewall for Your Florida Business
Picking a firewall isn't a one-size-fits-all decision. The right choice for a law firm in Tampa will be different from what a financial services company in Orlando needs. It’s a critical decision, because getting it wrong can mean leaving your business wide open to attacks or, just as bad, overspending on protection you don't actually need.
Let’s break down the main types of firewalls you'll encounter. This will give you the language and understanding to have a real, productive conversation about your business's security. A properly set up firewall is your first line of defense.
As you can see, a firewall acts as a central shield, blocking incoming threats while ensuring your team can get the access they need and your company data stays protected.
Hardware Firewalls: The Physical Gatekeepers
A hardware firewall is a dedicated, physical box that sits between your office network and the internet. Think of it as a security guard posted at the single entrance to your entire office building—every bit of data coming in or going out has to pass through it for inspection.
This type of firewall is a foundational piece of security for any business with a physical office in a city like Lakeland or Kissimmee. It creates a strong perimeter defense for every device connected to your local network, from your servers down to each employee's workstation.
- Pros: You get a robust, dedicated defense for the entire network. Since the device is built for one purpose, performance is generally very high.
- Cons: These can be costly to buy and maintain. More importantly, they offer zero protection for devices once they leave the office, like an employee’s laptop at home.
Software Firewalls: The Personal Bodyguards
A software firewall, on the other hand, is a program installed directly on an individual computer or server. Instead of guarding the whole building, this is like a personal bodyguard assigned to protect one specific asset.
Most operating systems have a basic software firewall built-in, but the business-grade versions give you far more control and visibility. They are absolutely essential for protecting remote workers or staff who travel, as they keep the device secure no matter what sketchy public Wi-Fi it connects to.
A key takeaway for Florida business owners is that hardware and software firewalls are not an either/or choice. They work best together—the hardware firewall guards the office, and software firewalls protect each individual endpoint. This creates a powerful, layered defense.
Next-Generation Firewalls: Advanced Threat Intelligence
Next-Generation Firewalls (NGFWs) are the evolution of the traditional hardware firewall. They don't just check the addresses on the data packets; they use deep packet inspection (DPI) to look inside and analyze the actual content flowing through your network. This allows an NGFW to spot and shut down sophisticated threats that older firewalls would completely miss.
These advanced systems typically come loaded with features like:
- Intrusion Prevention Systems (IPS): Actively scans traffic for known attack patterns and blocks them before they can do damage.
- Application Awareness: Lets you create rules based on specific apps (e.g., block Facebook but allow Salesforce), not just the technical ports and protocols.
- Threat Intelligence Feeds: These firewalls are constantly updated with fresh data on new and emerging cyber threats from around the globe.
For businesses in regulated industries like healthcare or finance, NGFWs are quickly becoming the non-negotiable standard. Their ability to stop advanced attacks and provide detailed logs is crucial for compliance. As you grow, understanding the full scope of managed services is crucial. To help with this, you can check out our comprehensive business IT support guide for Florida companies.
Cloud Firewalls: Guarding Your Digital Assets
As more businesses shift operations to cloud platforms like Microsoft Azure or Amazon Web Services (AWS), a new front has opened up in the security battle. A cloud firewall, often called Firewall-as-a-Service (FWaaS), is a cloud-based solution that extends protection to your cloud infrastructure and applications.
If your Orlando-based team relies heavily on cloud applications, a cloud firewall is what ensures your data stays secure even though it’s not sitting on a server in your office. It delivers the same kind of rock-solid security as a physical firewall but is built specifically for the decentralized nature of the cloud.
Here is the rewritten section, crafted to match the specified human-written style:
The Evolving Threat Landscape in Cybersecurity
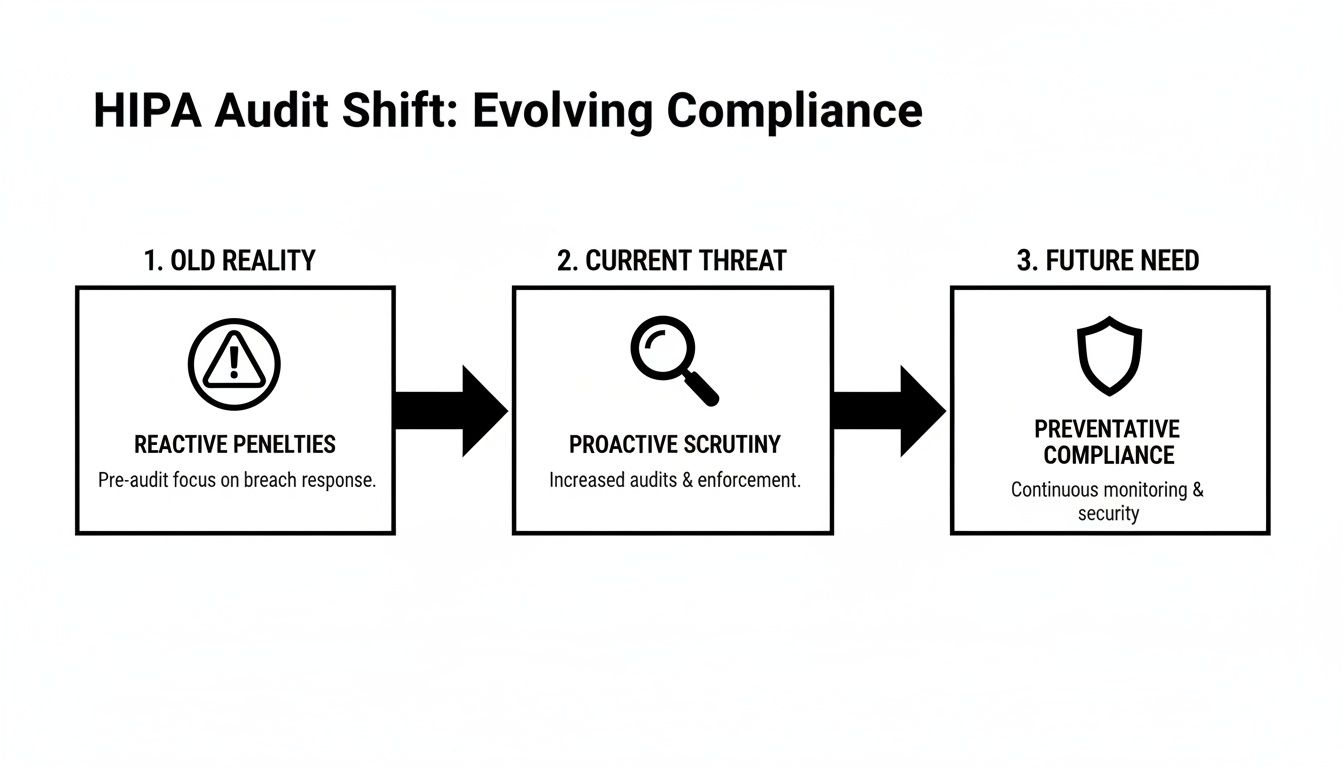
The cybersecurity world is always changing, and that makes having a modern firewall for your business more important than it's ever been. The old days, when cyber threats were only a problem for giant corporations, are long gone. Today, the focus has shifted, and small to mid-sized businesses right here in Central Florida are finding themselves directly in the crosshairs.
This isn't a random shift. Cybercriminals are opportunistic. They go after businesses they see as having weaker defenses, and they know that for a small business, a single breach can be catastrophic. The threat landscape has become a high-stakes game where enterprise-grade security isn't a luxury anymore—it's a fundamental cost of doing business safely.
Why Outdated Security Is No Longer Enough
We're seeing ransomware attacks, data breaches, and incredibly sophisticated phishing campaigns become more frequent and more damaging. Attackers are now finding and exploiting vulnerabilities in common business tools, including older firewalls, sometimes before a security patch is even available. This creates a terrifying window of time where your business is left completely exposed.
These new attack methods are specifically designed to sidestep traditional security measures that only look at surface-level information about your network traffic.
A modern firewall is the cornerstone of a layered defense. It uses real-time threat intelligence to protect you from advanced threats. This is absolutely vital because when attackers exploit vulnerabilities before a patch exists, a strong, multi-layered defense is the only thing that will prevent a compromise.
This proactive approach is what separates a secure business from becoming another statistic. It’s about having a system smart enough to recognize and shut down threats that didn’t even exist yesterday.
Regulated Industries Are Paving the Way
If you look at industries like healthcare and finance, adopting powerful firewall solutions isn't just a good idea—it’s the law. Stiff regulations like the Health Insurance Portability and Accountability Act (HIPAA) mandate robust security controls to protect sensitive patient and client data.
Businesses in these sectors, from medical practices in Lake Nona to financial advisors in Winter Park, understand the immense value of the data they manage. Because of this, they are leading the way in adopting Next-Generation Firewalls (NGFWs) and other advanced security measures. This trend sends a clear message to every other business in the region: if the most regulated industries are making this shift, it’s time for everyone else to pay attention.
The demand for these advanced solutions is driving massive market growth. A recent analysis projects the global enterprise firewall market will expand from USD 2.75 billion in 2026 to USD 5.70 billion by 2033. What’s really telling is that the Banking, Financial Services, and Insurance (BFSI) sector is expected to make up 34% of this market share, which highlights how critical top-tier security has become due to compliance and high-stakes data protection. You can see the full analysis in the report on firewall market growth drivers from Coherent Market Insights.
This data confirms that investing in stronger firewalls for businesses isn't just a technical concern; it's a major economic and operational priority.
The Rise of Sophisticated Cyberattacks
Today’s cyber threats are far more advanced than the simple viruses of the past. Modern attacks are often multi-stage events that use custom tools designed to fly under the radar. For instance, attackers are now using methods like:
- Fileless Malware: This is malicious code that runs entirely in a computer’s memory, never touching the hard drive. It's a ghost that traditional antivirus software can't see.
- Zero-Day Exploits: These are attacks that target a previously unknown software vulnerability, giving security teams zero days to prepare a patch.
- Legitimate Tool Abuse: Cybercriminals will often use legitimate remote access tools—the same kind your IT department uses—to blend in with normal network traffic and maintain persistent access to your systems.
A basic, off-the-shelf firewall simply can't keep up with these methods. A modern, professionally managed firewall, on the other hand, is equipped with the intelligence and capabilities needed—like deep packet inspection and intrusion prevention—to spot and neutralize these complex threats in real time. It's what stands between your business and complete operational and financial chaos.
Protecting Your Website with a Web Application Firewall
If your business relies on a website for more than just listing a phone number, you have a digital front door that needs specialized protection. For any business in Orlando or Tampa with an e-commerce store, a client portal, or an online booking system, a traditional network firewall simply isn't enough. You need another, more specific layer of security: a Web Application Firewall (WAF).
Think of it this way: your main business firewall protects your office network—the building itself. A WAF, on the other hand, protects the specific web applications your customers interact with, like the payment form on your website or the login page to their account. It's a specialist guard trained to spot and stop attacks aimed directly at the software your clients use every day.

Shielding Your Digital Front Door
A WAF sits between your web server and the public internet, inspecting all incoming HTTP traffic before it ever reaches your application. Its entire job is to filter out malicious requests designed to exploit common vulnerabilities in web software.
This is a fundamentally different job from other firewalls for businesses, which typically focus on network-level threats. A WAF provides critical protection against application-layer attacks that other security tools are completely blind to.
Common threats a WAF is built to block include:
- SQL Injection (SQLi): This is where an attacker slips malicious code into a web form (like a search bar) to trick your database into coughing up sensitive information.
- Cross-Site Scripting (XSS): This attack involves injecting malicious scripts into your website, which then run in the browsers of your unsuspecting visitors, potentially stealing their credentials or other data.
- Zero-Day Attacks: These are attacks that exploit newly discovered software flaws before a security patch is even available, making proactive WAF protection absolutely essential.
For a medical practice in Kissimmee with an online patient portal or a law firm in Tampa that exchanges sensitive documents with clients online, these threats are not abstract. A single successful attack could lead to a massive data breach, crippling regulatory fines, and irreparable damage to your reputation.
The Growing Need for Application Security
As more business functions move online, the attack surface for every company grows. This reality has led to a surge in demand for WAFs, with the market projected to jump from USD 10.13 billion in 2026 to USD 30.86 billion by 2034. North America currently leads the market, which reflects the region's advanced adoption of crucial cybersecurity technology. You can learn more from these findings on the web application firewall market from Fortune Business Insights.
A Web Application Firewall acts as a vital shield between the public internet and your mission-critical web applications. In a competitive market like Central Florida, protecting these online assets is non-negotiable for maintaining client trust, ensuring compliance, and guaranteeing business continuity.
Ultimately, a WAF is a specialized tool for a specific and growing problem. It ensures that your most public-facing assets—the tools your customers and partners rely on—are defended with the same rigor as your internal network. Without it, your digital front door is left wide open.
Why Modern Network Security Is an Urgent Priority
The way we all do business has been turned on its head. With remote work becoming the norm, a heavy reliance on cloud apps, and cyberattacks getting smarter by the day, we're facing a perfect storm. For any business here in Central Florida, from Orlando to Tampa, putting off network security is a gamble you just can't afford to take anymore.
The days of setting up a simple security solution and forgetting about it are long gone. We're in an era of constant digital threats where a single breach can grind your operations to a halt, trigger expensive compliance fines, and ruin the reputation you've spent years building. This new reality requires a change in both mindset and technology.
The Key Drivers Behind Modern Security
Three big forces are pushing businesses to rethink their defenses: the devastating impact of ransomware, the shift to Zero Trust security models, and the growing complexity of data protection rules. An outdated firewall is simply not equipped to handle this environment. If your company has a hybrid workforce or uses cloud services, a modern firewall with built-in threat intelligence isn't just a good idea—it's an absolute must.
The market's explosive growth tells the story. The network security firewall market is on track to jump from USD 9.77 billion in 2026 to an incredible USD 21.67 billion by 2030. This rapid growth is a direct response to the challenges your business is facing right now—cloud adoption, sophisticated attacks, and the need for stricter security. You can discover more about these market growth drivers in the full report.
Ransomware: The Business Killer
Ransomware isn't just about encrypting your files anymore. It has morphed into a multi-layered extortion racket. Attackers now steal your sensitive data before they lock you out, threatening to leak client lists or financial records online if you refuse to pay. This "double extortion" tactic puts an immense amount of pressure on businesses, as the fallout extends far beyond just system downtime.
A single ransomware incident can halt your entire operation, lock you out of critical business systems, and expose you to severe regulatory penalties for failing to protect customer data. For many small and mid-sized businesses, the financial and reputational damage is insurmountable.
This threat is very real and happening every day. Modern firewalls for businesses are now built with the intelligence to spot and block the initial break-in attempts that lead to a full-blown ransomware attack, making them one of your most essential lines of defense.
Embracing a Zero Trust Security Model
The old security mantra of "trust but verify" is officially dead. In a world where your employees connect from anywhere on any device, the traditional network perimeter has all but vanished. The modern approach is Zero Trust, a security framework built on one simple, powerful principle: trust nothing and verify everything.
A Zero Trust model operates on the assumption that a threat could come from anywhere—inside or outside your network. It demands strict identity verification for every single user and device trying to access a resource, no matter where they are. This drastically shrinks your attack surface. You can learn more about strengthening security with next-gen firewalls that make this model possible.
Putting a modern firewall in place is a foundational step in building a true Zero Trust architecture, ensuring every connection is challenged and verified before it gets anywhere near your critical data.
How to Choose a Managed Firewall Service Partner
For most business owners in Orlando and Tampa, trying to manage a business-grade firewall is like trying to perform your own dental surgery. You might have a vague idea of what to do, but the technology is complex, the threats are relentless, and one wrong move can be catastrophic.
This is where a Managed Security Service Provider (MSSP) becomes an essential partner, not just another IT vendor. Outsourcing this critical function turns your cybersecurity from a reactive, capital-intensive headache into a proactive, predictable operational expense. A true security partner takes the entire burden of firewall management off your plate, letting you focus on your business while their experts stand guard.

The Core Benefits of Outsourcing Firewall Management
Partnering with an MSSP for your firewalls for businesses gives you immediate advantages that are nearly impossible for a small or mid-sized company to replicate in-house. It’s about gaining access to enterprise-level resources without the enterprise-level price tag.
Here’s what you get:
- 24/7/365 Expert Monitoring: Your firewall is watched around the clock by a dedicated Security Operations Center (SOC). These are cybersecurity specialists whose only job is to hunt for threats, analyze alerts, and respond to incidents the moment they happen—day or night.
- Proactive Threat Hunting: A good MSSP doesn't just wait for an alarm. They actively search for signs of compromise, using advanced tools and threat intelligence to find and neutralize attackers before they can do damage.
- Expert Configuration and Maintenance: Your firewall will be set up and fine-tuned by certified professionals who understand the specific security needs of your industry and the Central Florida business environment. They handle all updates, patches, and rule changes to keep your defenses sharp.
- Simplified Compliance and Reporting: For law firms, medical practices, or financial advisors, proving compliance is non-negotiable. An MSSP provides the detailed logs and regular reports you need for audits, showing you're taking every necessary step to protect sensitive data.
Vetting Potential MSSP Partners in Central Florida
Choosing the right partner is the most important decision you'll make. Not all providers are created equal, and you need a team that aligns with your business goals—not one that just sells you a box and a basic service plan. As you evaluate potential MSSPs in the Orlando area, you have to ask tough, specific questions.
Your goal is to find a true partner, and the details of their operations will reveal their commitment. Learning how to choose the right managed service partner is a critical skill for any business leader looking to secure their operations.
To help you vet potential providers, here is a checklist of critical questions to ask:
- Do you operate your own 24/7/365 Security Operations Center (SOC)? Ask if their SOC is staffed by their own U.S.-based employees or if they outsource it. An in-house team provides far better accountability and communication.
- What are your guaranteed response times (SLAs)? Get specific Service Level Agreements in writing. What happens when a critical alert is triggered at 2 AM on a Sunday? How quickly will an expert actually be working on the problem?
- What is your pricing model? Avoid unpredictable hourly billing. Look for a predictable, all-inclusive flat-rate model that covers technology, management, monitoring, and support. This aligns their incentive with yours—they profit when you stay secure, not when you have problems.
- Can you provide references from local businesses in my industry? A provider with deep experience protecting other Central Florida law firms or medical practices will understand your unique challenges and compliance needs on a much deeper level.
Selecting a managed firewall partner is about entrusting a firm with the security of your entire business. You're looking for a team with proven local expertise, transparent pricing, and a proactive security posture that prioritizes prevention over reaction.
Ultimately, your choice should come down to trust and demonstrable expertise. The right MSSP for your Orlando-based business will act as an extension of your team, providing the peace of mind that comes from knowing your most critical assets are protected by dedicated experts, day and night.
Frequently Asked Questions About Business Firewalls
When it comes to protecting their business, I hear a lot of the same questions from owners across Central Florida. Getting straight answers about firewalls for businesses is the first step to making a smart decision for your company's security.
Let's clear up some of the most common points of confusion.
My Business Is Small Do I Really Need an Advanced Firewall
Yes, absolutely. In fact, thinking your business is "too small to be a target" is one of the most dangerous assumptions you can make. Cybercriminals love small and mid-sized businesses for that exact reason—they're often banking on "good enough" security.
An attack on a small Orlando law firm or a Tampa medical practice can be just as devastating as one on a huge corporation. Often, it's worse, since smaller companies have fewer resources to absorb the blow.
A single data breach can trigger massive financial losses, painful legal battles, and a complete loss of client trust that's nearly impossible to win back. A modern, professionally managed firewall isn’t just an IT expense; it's a core investment in your company's survival.
Today, a sophisticated firewall is non-negotiable, regardless of your company’s size. It’s the essential gatekeeper that protects your client data, financial records, and operational stability from a constant barrage of automated and targeted threats.
What Is the Difference Between a Firewall and Antivirus Software
This is a great question, and it's a common point of confusion. They play two completely different—and equally critical—roles in your security. The easiest way to think about it is to picture how you'd secure a physical office building.
- A firewall is the security guard at the property's main gate. It stands on the perimeter, inspecting every bit of traffic trying to enter your network from the outside world. It blocks anything suspicious or dangerous before it can even set foot on the premises.
- Antivirus software acts like the alarm system and security patrol inside each room. It runs on individual devices, like your laptop or server, to find, isolate, and remove any malicious code that might have somehow slipped past the front gate.
You absolutely need both. The firewall handles the heavy lifting of perimeter defense for your whole network, while antivirus provides the essential endpoint protection for each device inside it.
How Much Does a Managed Firewall Service Cost in Central Florida
The cost for a managed firewall service really depends on a few key factors: the size of your network, how many employees you have, and the complexity of your security and compliance needs.
However, any reputable Managed Security Service Provider (MSSP) should offer you predictable, flat-rate pricing. It's also helpful to understand where this fits into the bigger picture of Security Managed Services when you're deciding on outsourcing.
This all-in model is almost always more cost-effective than trying to manage an enterprise-grade firewall yourself. It bundles the high-end technology, 24/7 expert monitoring, proactive management, and compliance reporting into one stable operational expense. This gets rid of surprise IT bills and lets you budget for your security with complete confidence.
Ready to secure your Central Florida business with a professionally managed firewall service? The team at Cyber Command, LLC provides 24/7/365 protection with predictable pricing, ensuring your business is defended by experts day and night. Protect your assets and gain peace of mind by visiting https://cybercommand.com to learn more.